Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Once Devtron is installed, it has a built-in admin user with super admin privileges with unrestricted access to all Devtron resources. We recommended to use a user with super admin privileges for initial and global configurations only and then switch to local users or configure SSO integration.
Only users with super-admin privileges can create SSO configuration. Devtron uses Dex for authenticating a user against the identity provider.
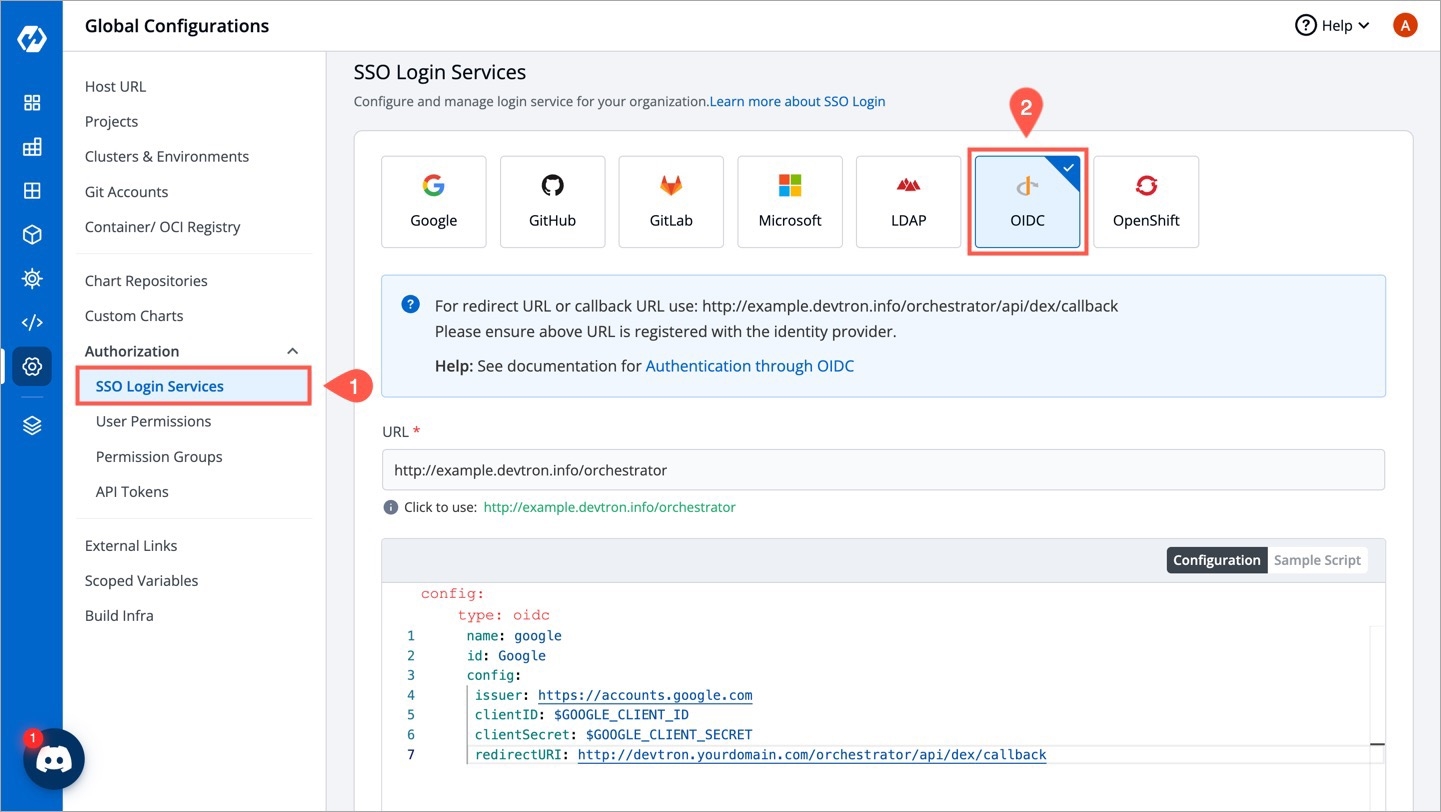
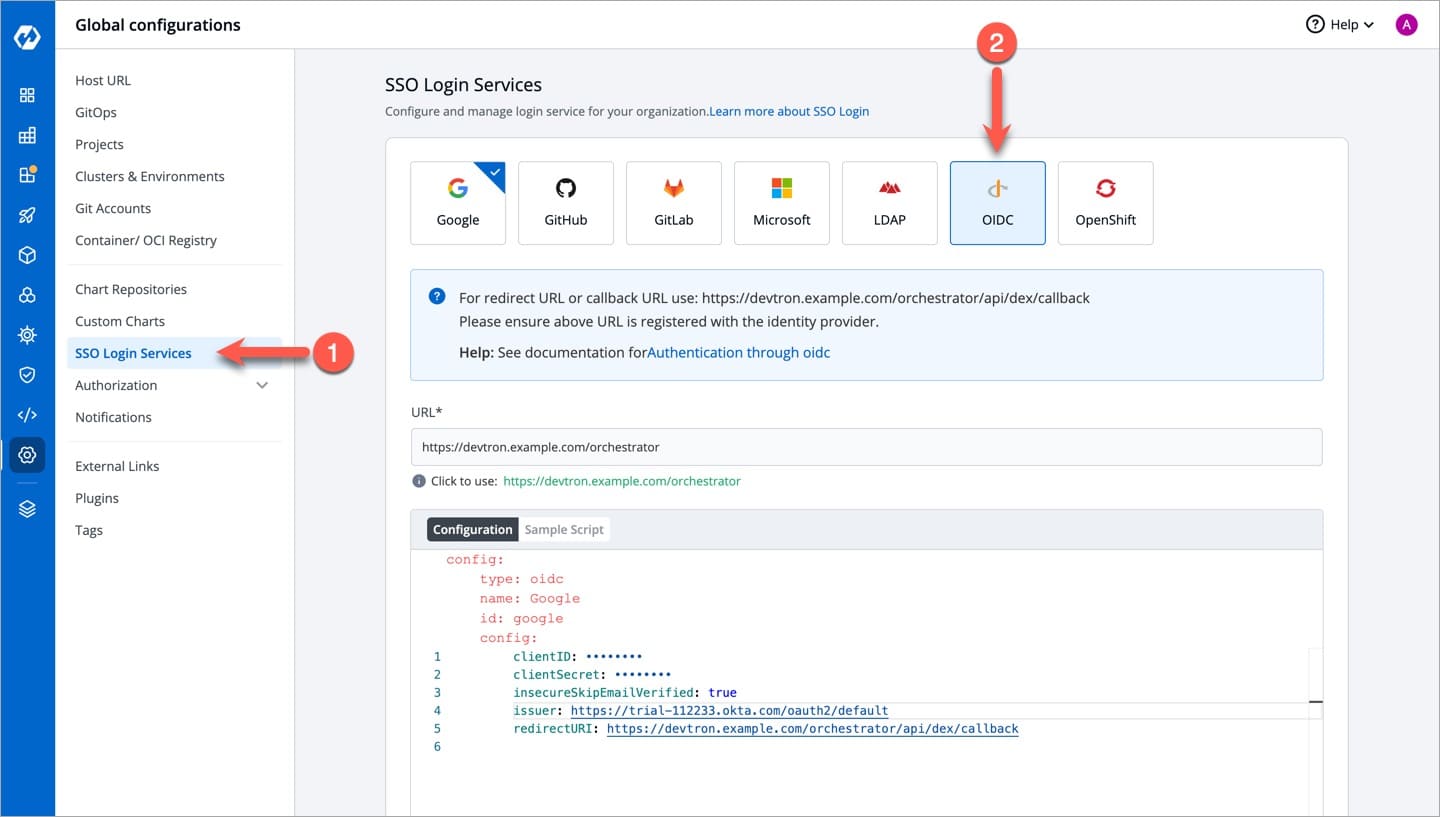
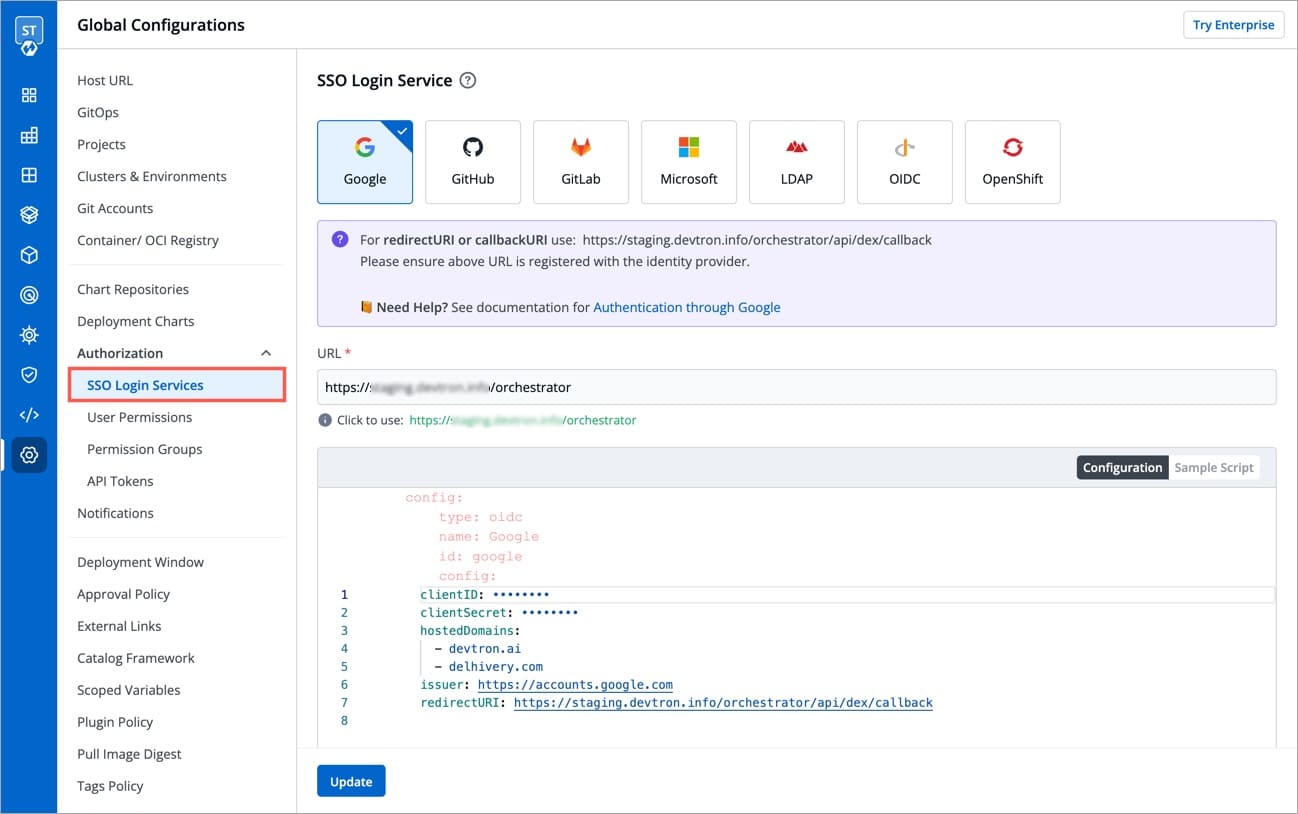
To add/edit SSO configuration, go to the SSO Login Services section of Global Configurations.
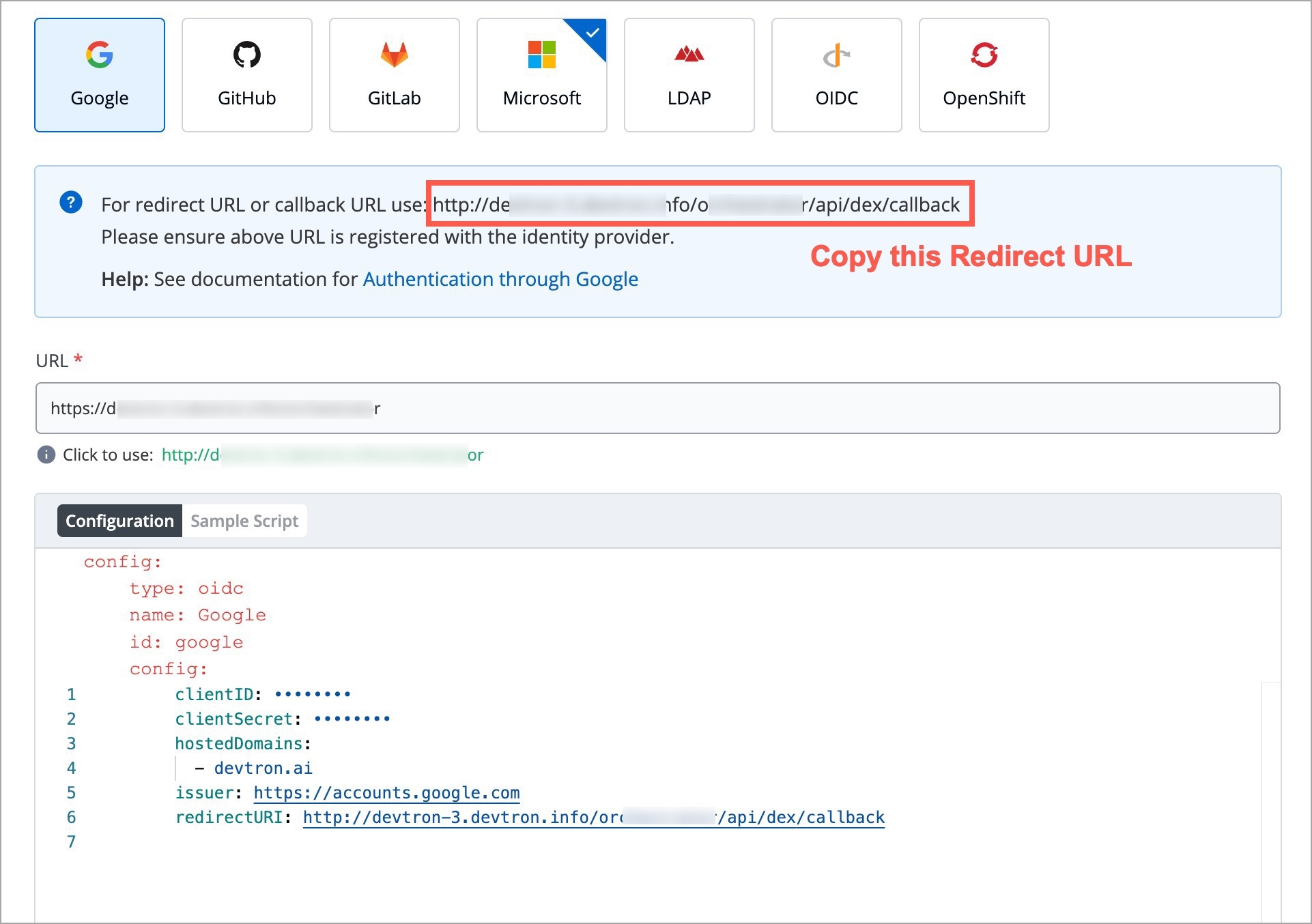
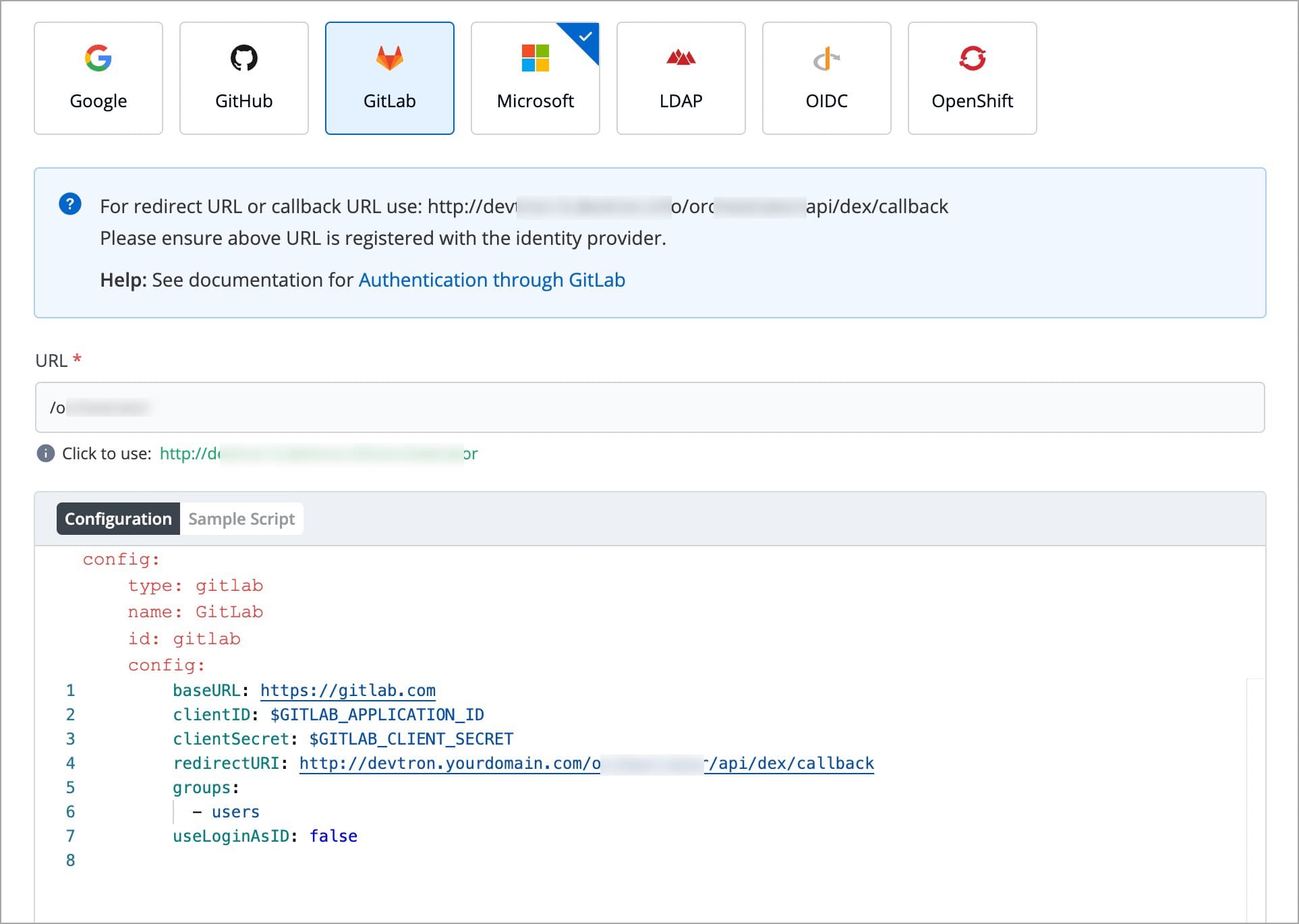
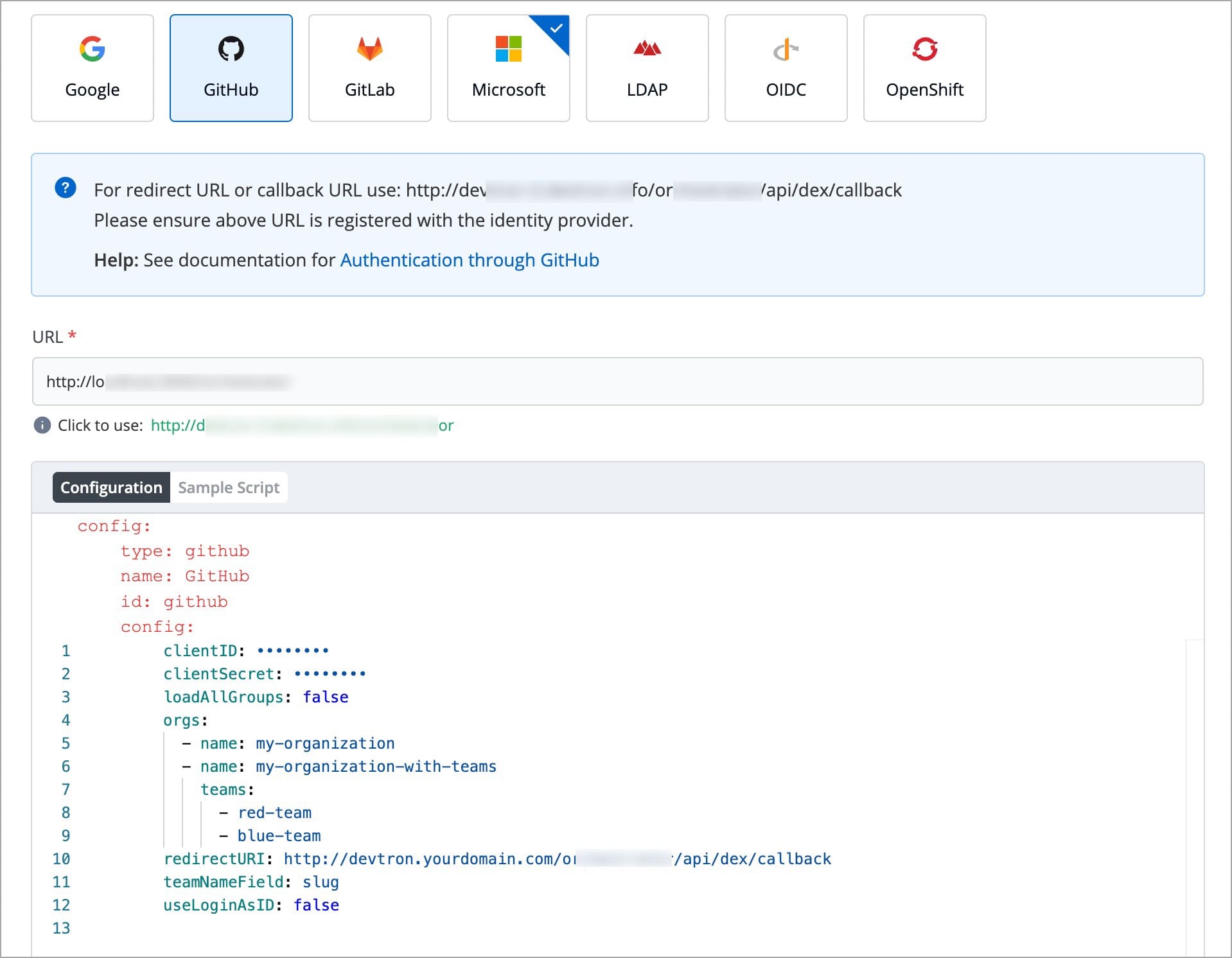
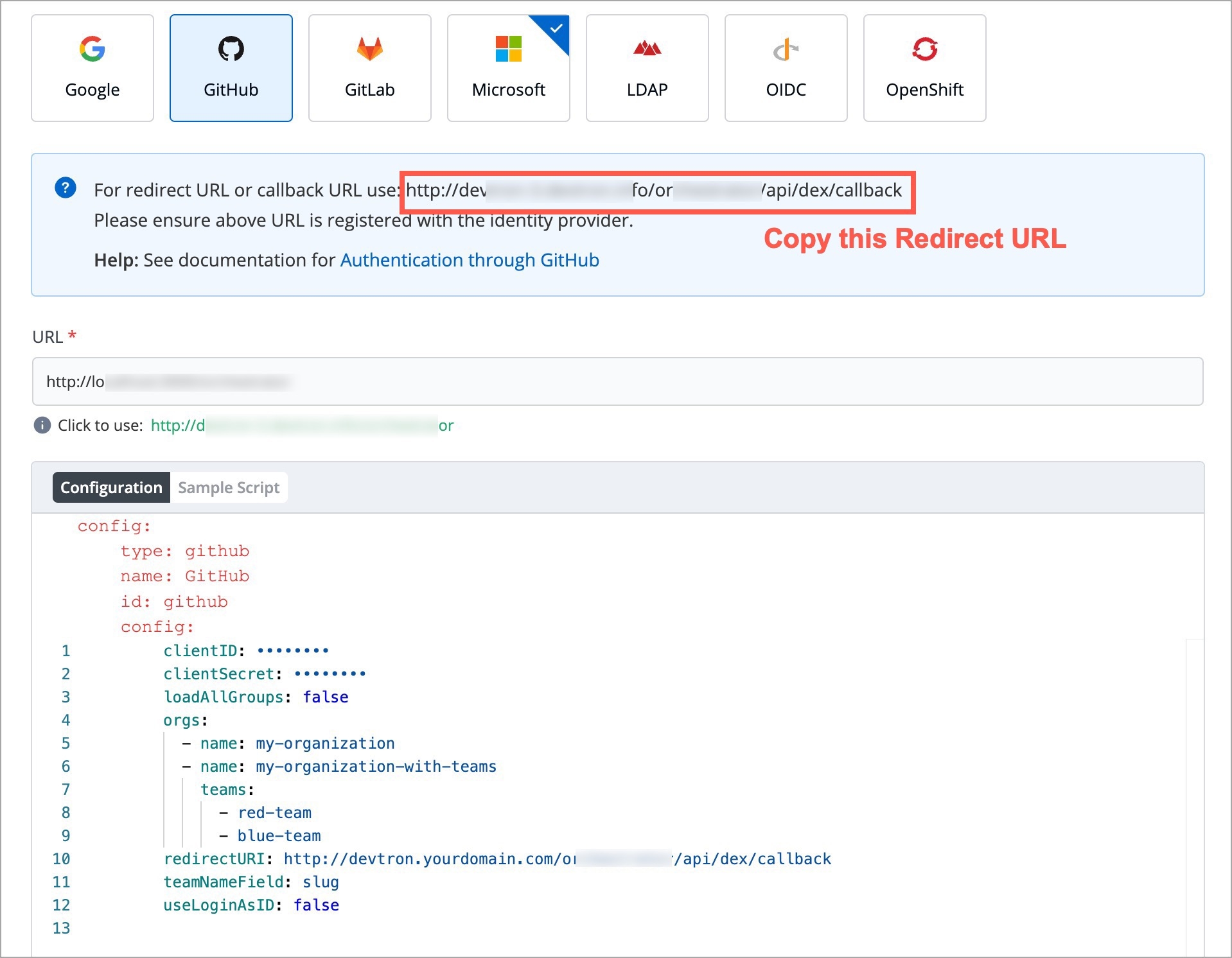
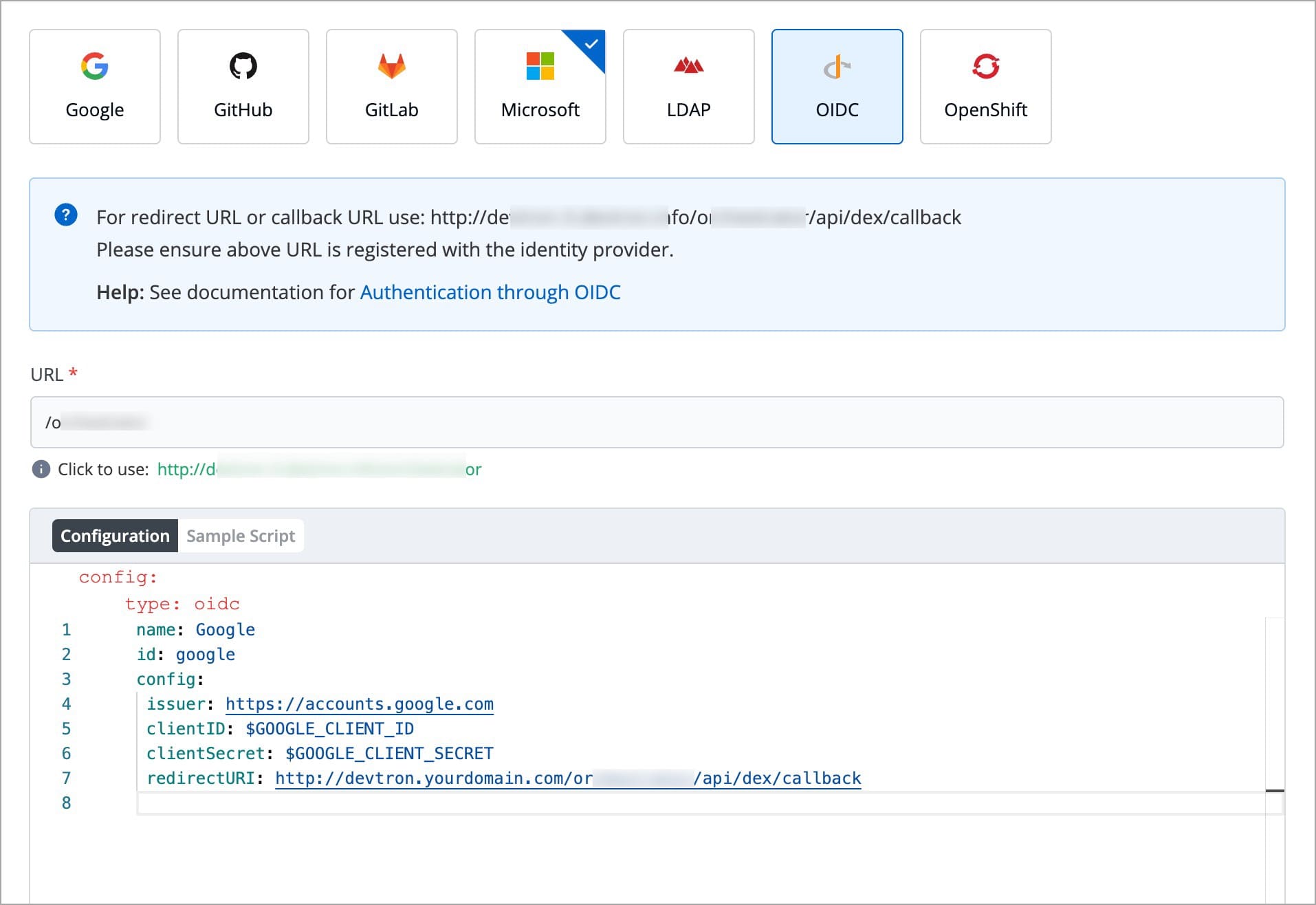
Below are the SSO providers which are available in Devtron. Select one of the SSO providers (e.g., GitHub) to configure SSO:
Google GitHub GitLab Microsoft LDAP OpenID Connect OpenShift
Dex implements connectors that target specific identity providers for each connector configuration. You must have a created account for the corresponding identity provider and registered an app for client key and secret.
Refer the following documents for more detail.
https://dexidp.io/docs/connectors/
https://dexidp.io/docs/connectors/google/
Make sure that you have a super admin access.
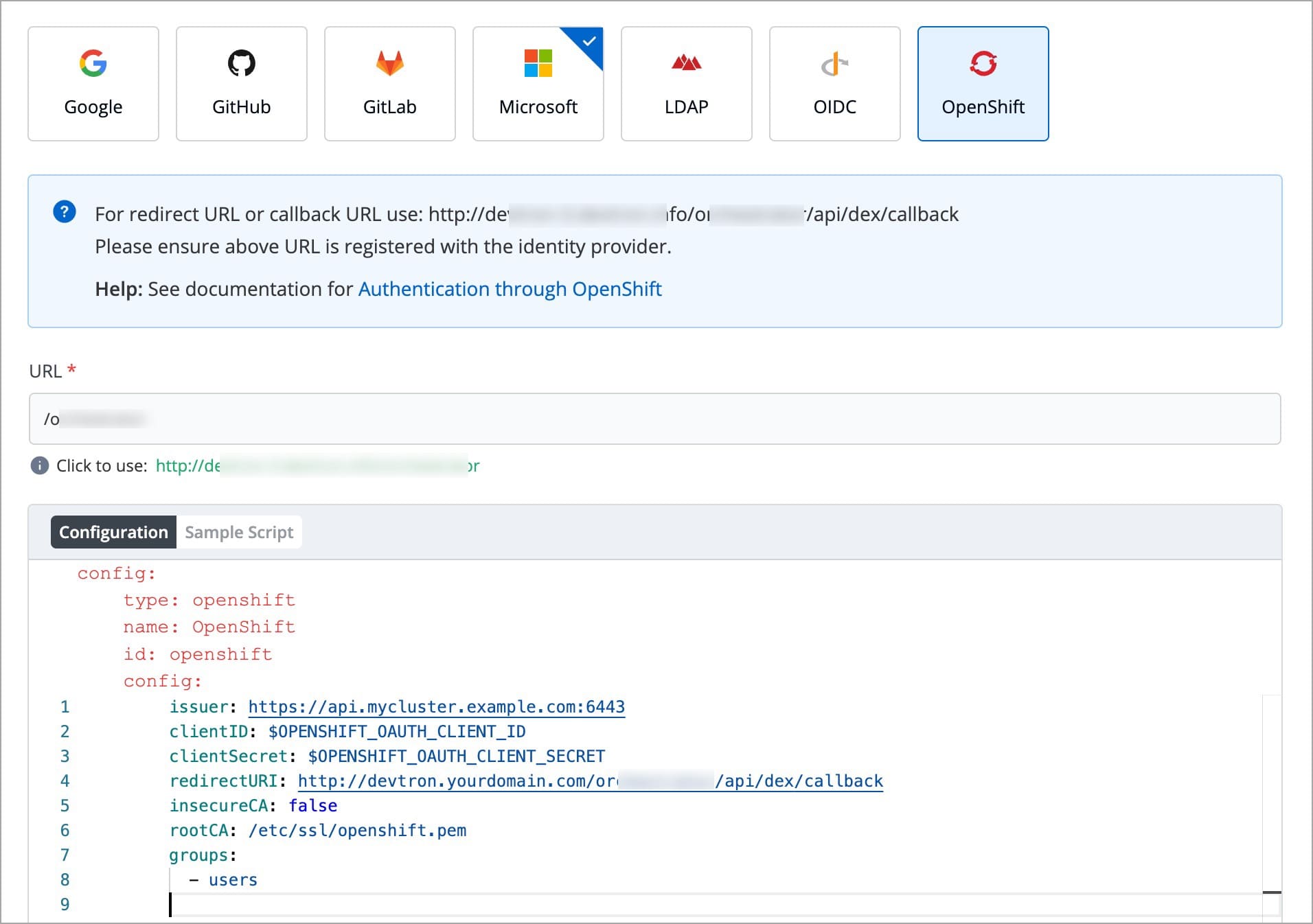
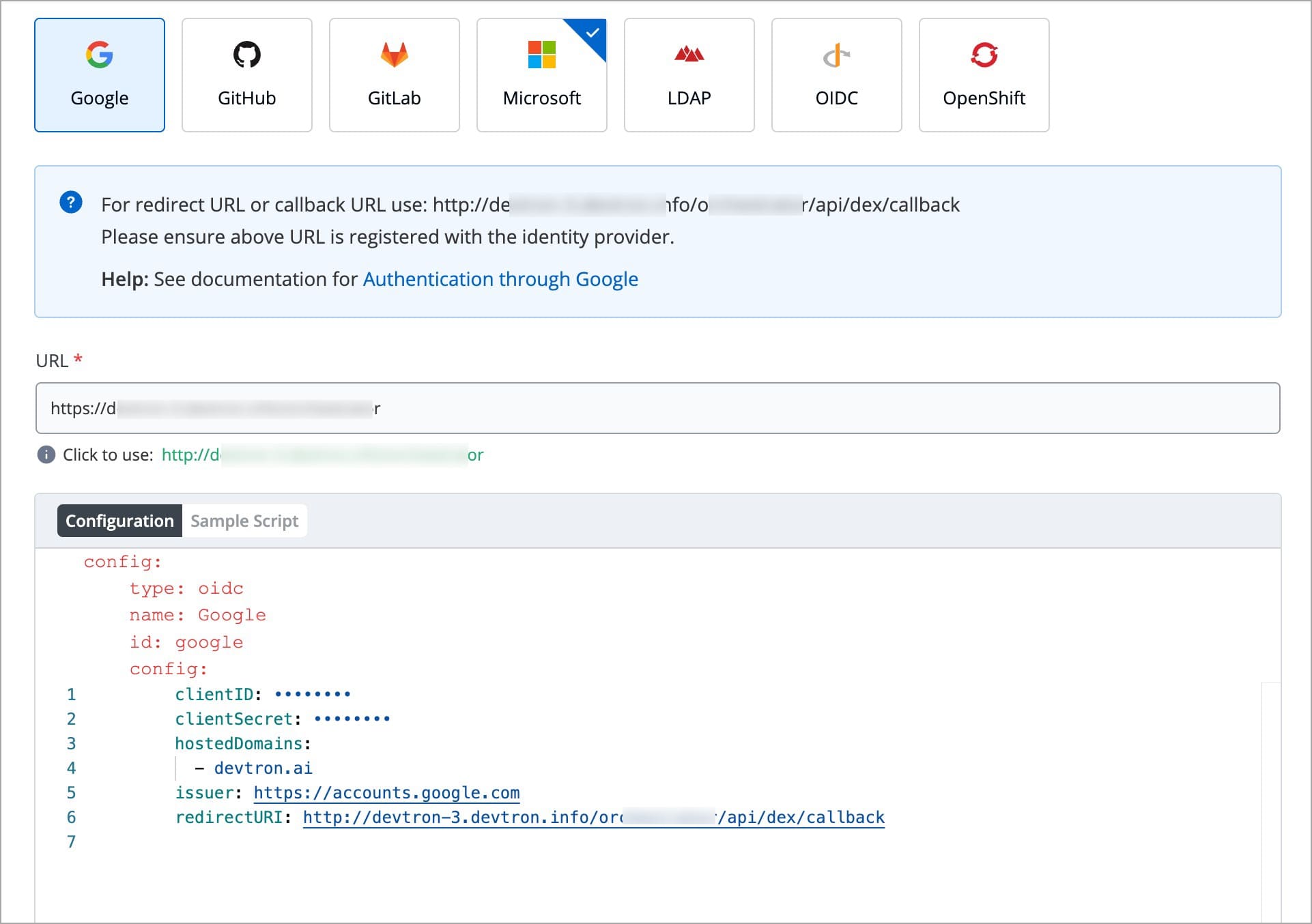
Go to the Global Configurations → SSO Login Services and click any SSO Provider of your choice.
In the URL field, enter the valid Devtron application URL where it is hosted.
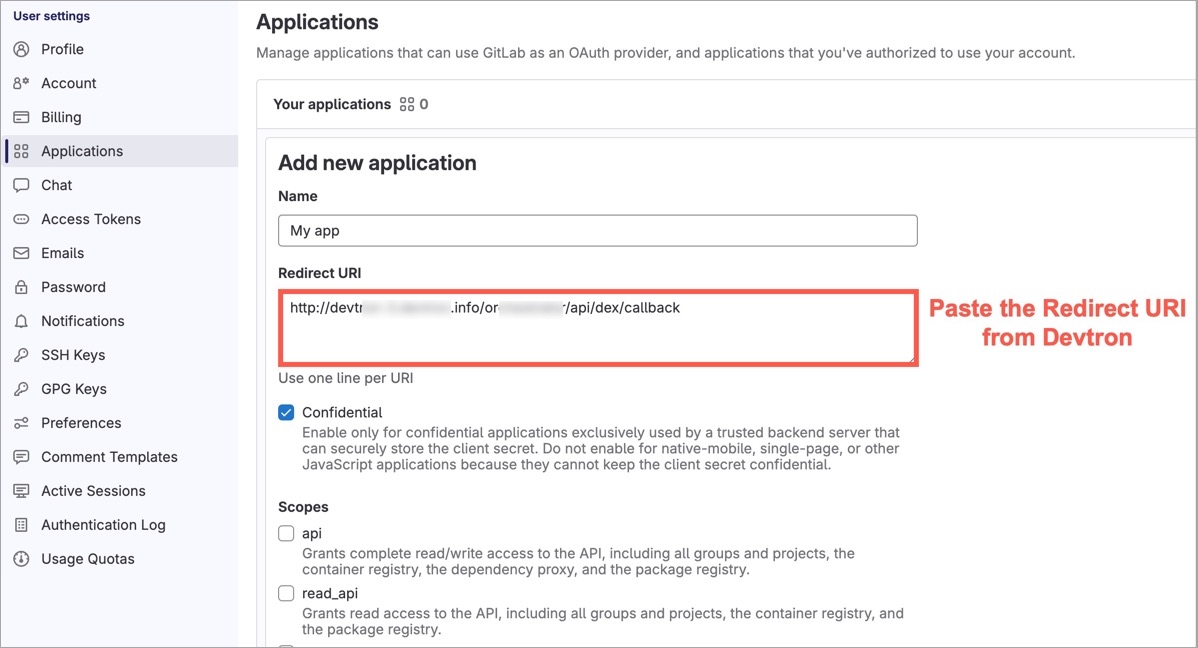
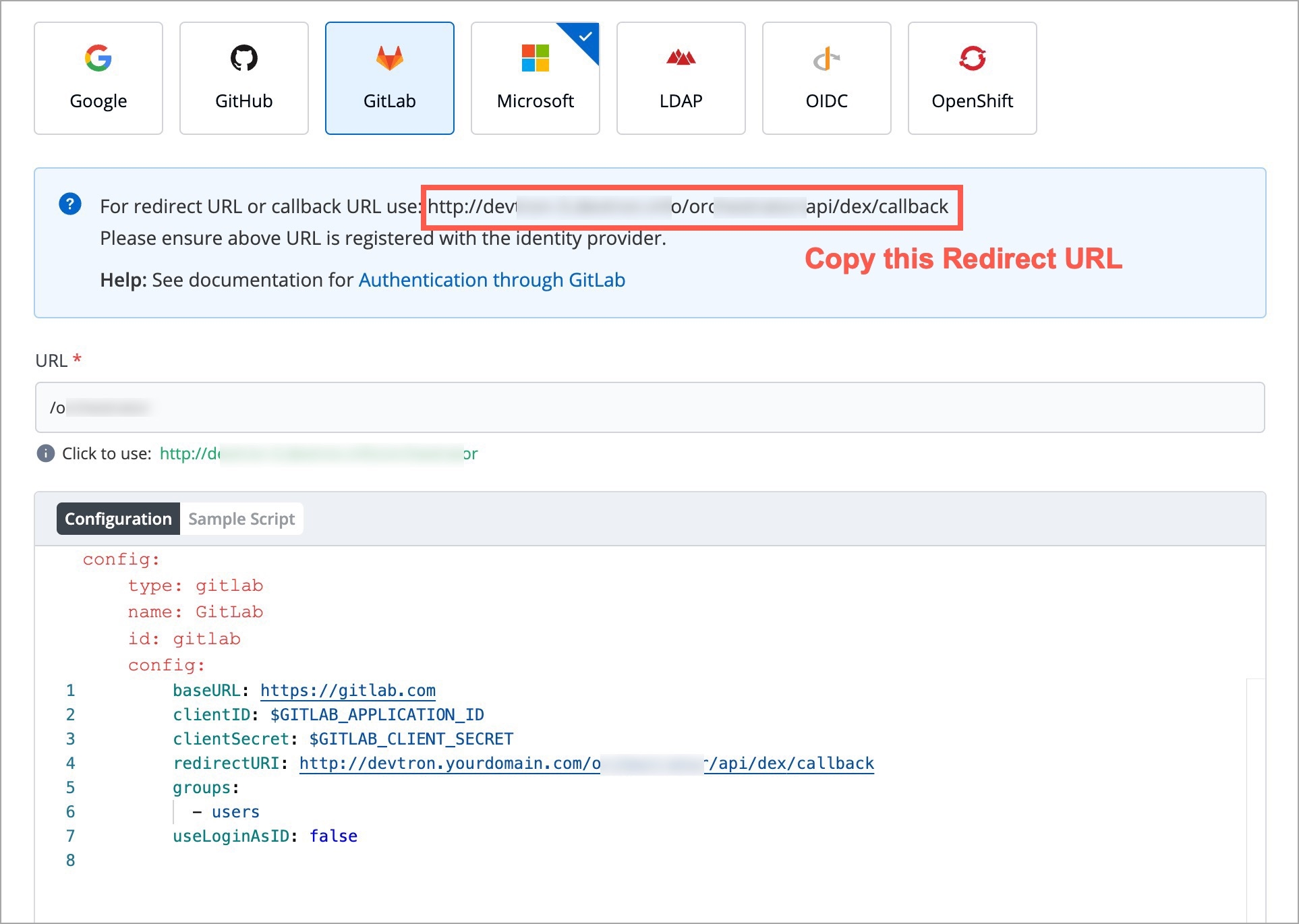
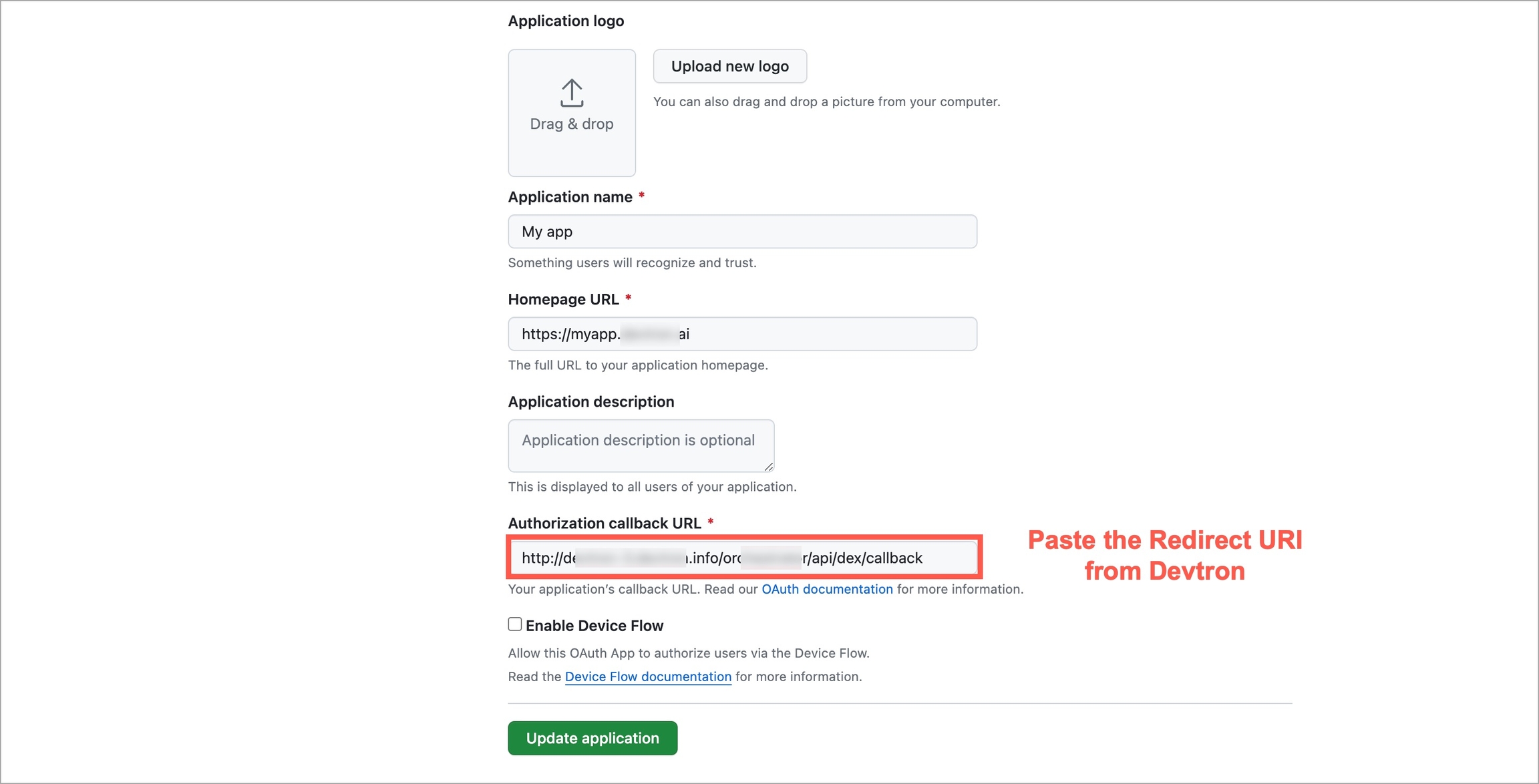
For providing redirectURI or callbackURI registered with the SSO provider, you can either select Configuration or Sample Script.
Provide the client ID and client Secret of your SSO provider (e.g. If you select Google as SSO provider, then you must enter $GOOGLE_CLIENT_ID and $GOOGLE_CLIENT_SECRET in the client ID and client Secret respectively.)
Select Save to create and activate SSO Login Service.
Note:
Only single SSO login configuration can be active at one time. Whenever you create or update any SSO configuration, it will be activated and used by Devtron and previous configurations will be deleted.
Except for the domain substring, URL and redirectURI remains same.
You can change SSO configuration anytime by updating the configuration and click Update. Note: In case of configuration change, all users will be logged out of Devtron and will have to login again.
type : Any platform name such as (Google, GitLab, GitHub etc.)
name : Identity provider platform name
id : Identity provider platform which is a unique ID in string. (Refer to dexidp.io
config : User can put connector details for this key. Platforms may not have same structure but common configurations are clientID, clientSecret, redirectURI.
hostedDomains : Domains authorized for SSO login.
After configuring an SSO for authentication, you need to add users in Devtron, else your users won't be able to log in via SSO.
In case you have enabled auto-assign permissions in Microsoft or LDAP, relevant permission groups must also exist in Devtron for a successful login.
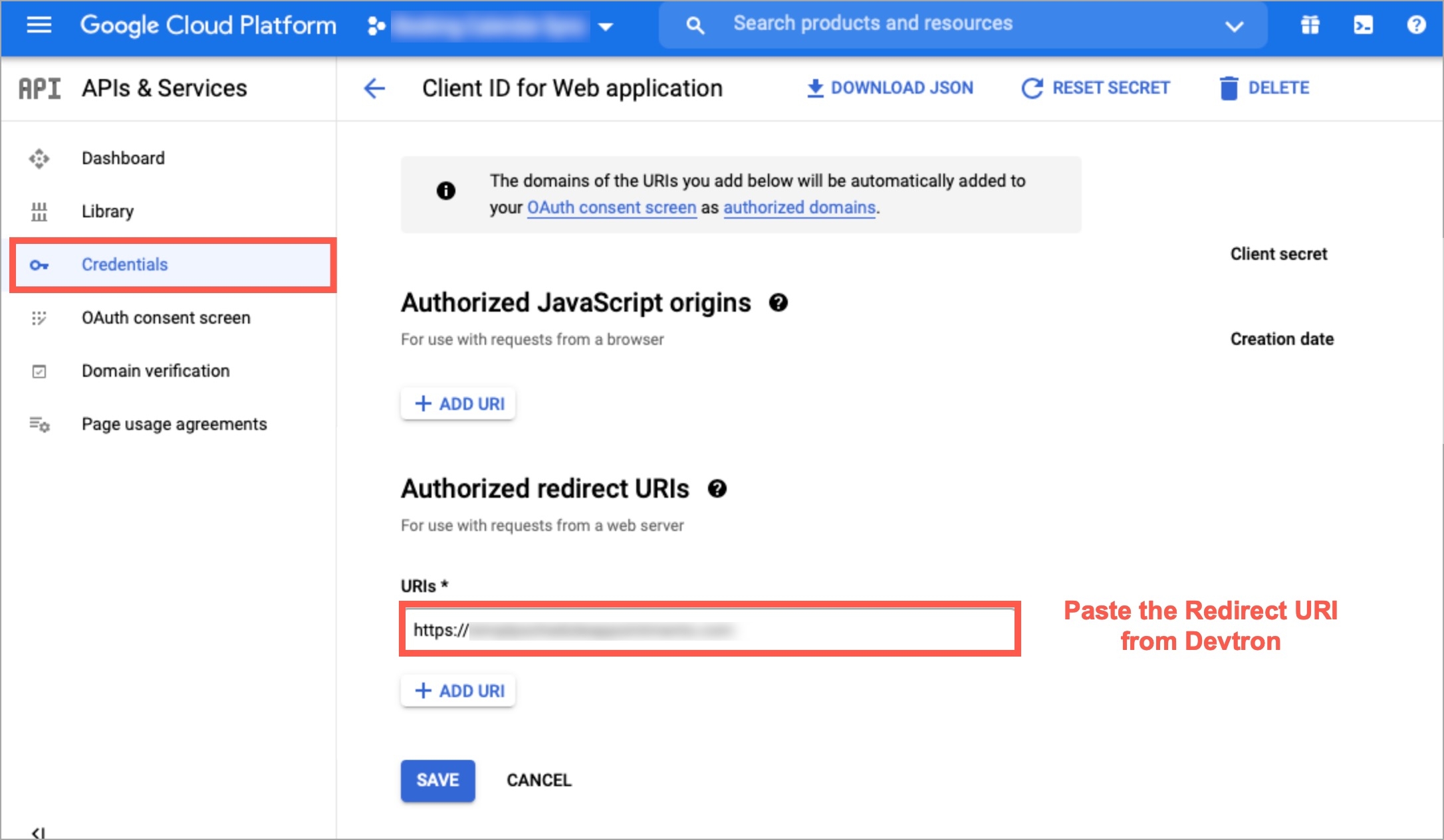
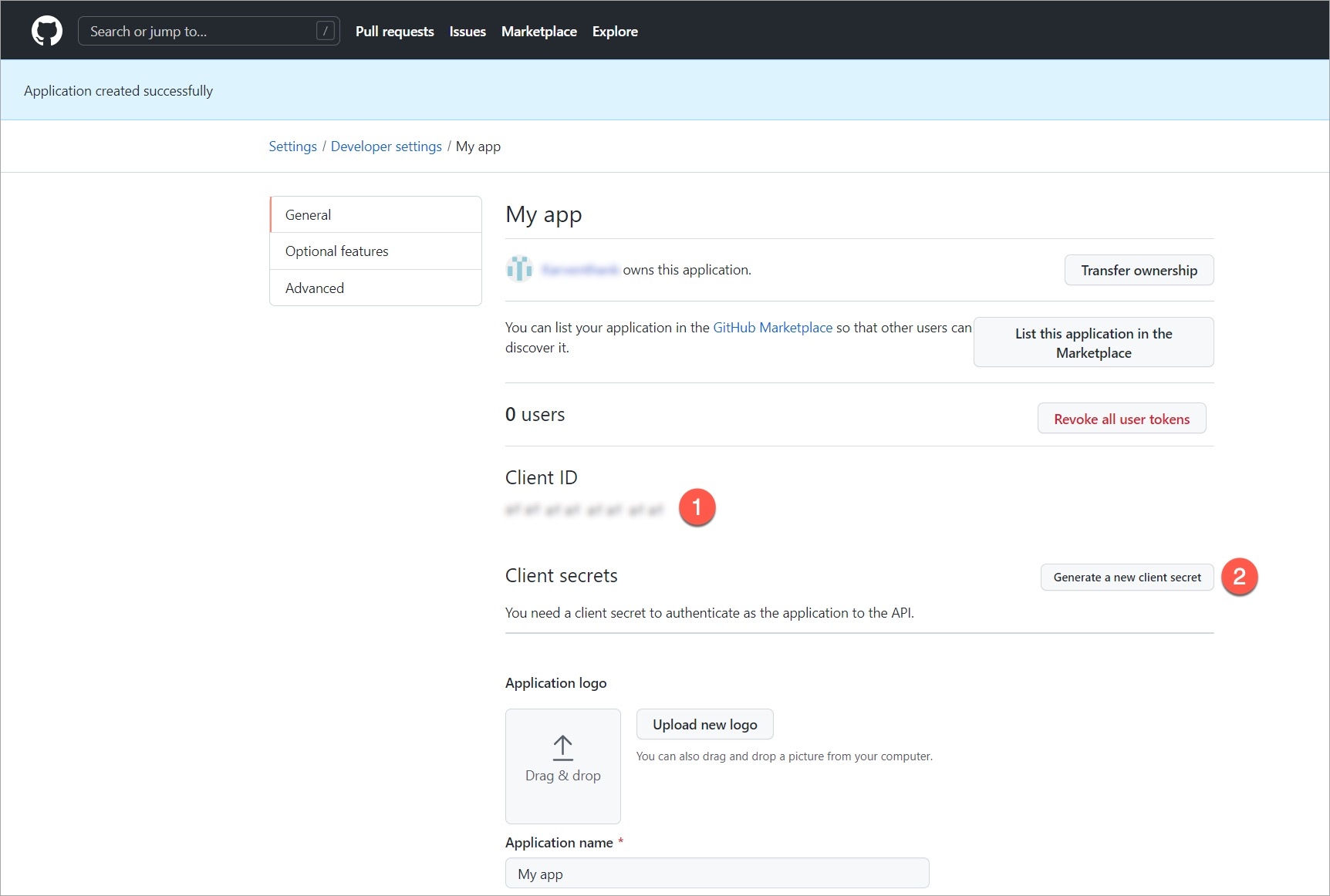
Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
clientSecret
redirectURI (provided in SSO Login Services by Devtron)
Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
clientSecret
redirectURI (provided in SSO Login Services by Devtron)
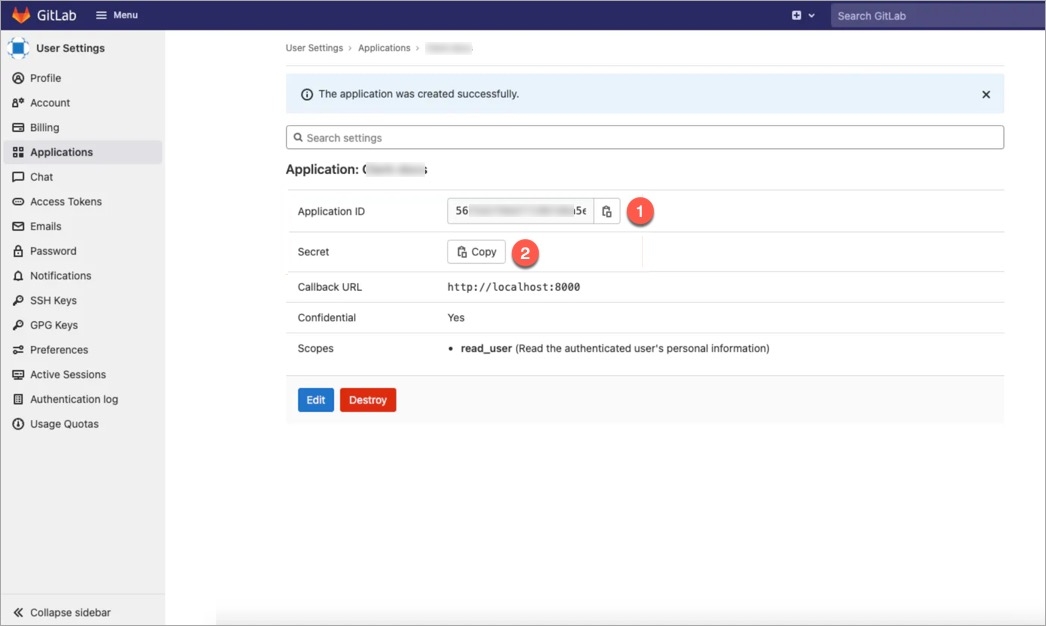
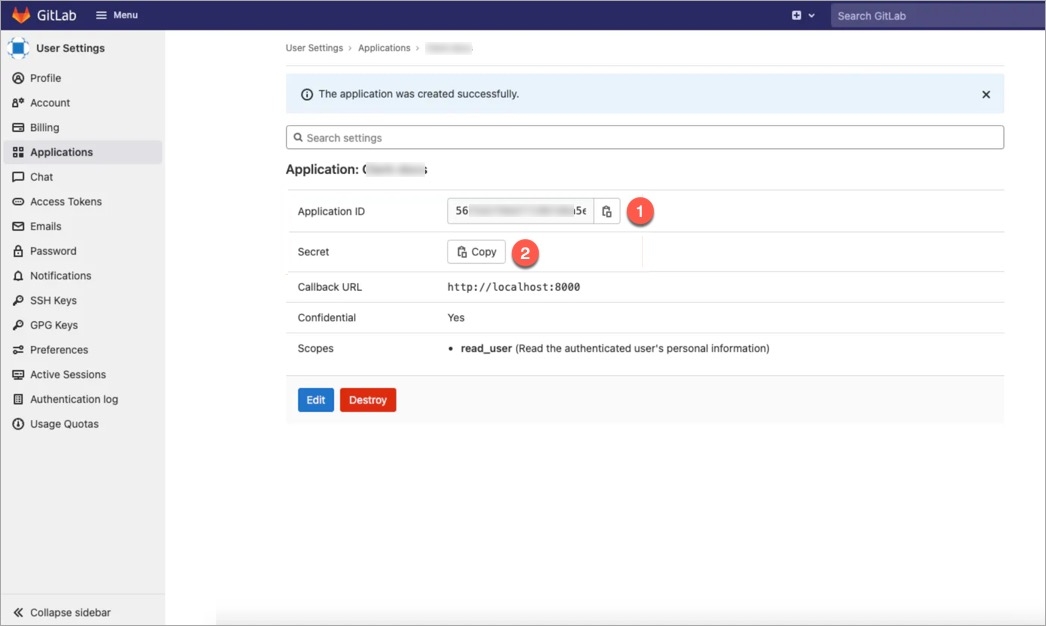
Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
clientSecret
redirectURI (provided in SSO Login Services by Devtron)
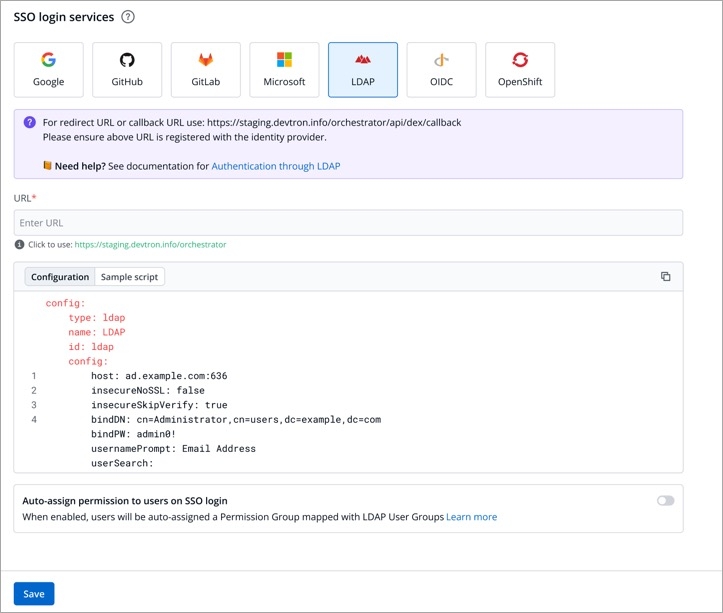
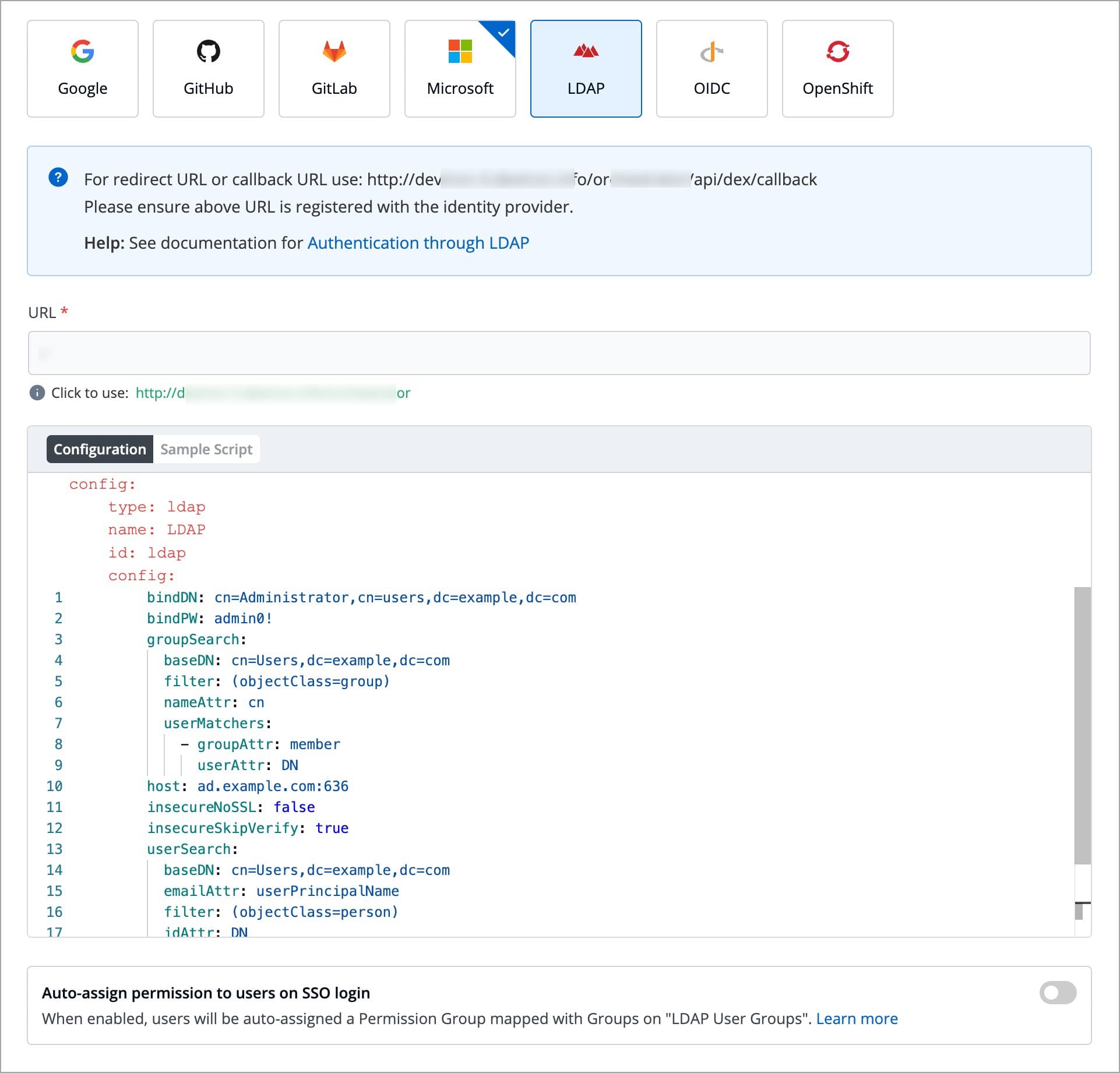
Devtron provides a sample configuration out of the box. Here are some values you need to fetch from your LDAP.
bindDN
bindPW
baseDN
Since LDAP supports creation of User Groups, this feature simplifies the onboarding process of organizations having a large headcount of users. It also eliminates repetitive permission assignment by automatically mapping your LDAP User groups to Devtron's Permission Groups during single sign-on (SSO) login.
If you've created user groups in LDAP, you can create corresponding permission groups in Devtron with the same names. When members of those user groups first log in to Devtron, they'll automatically inherit the permissions from their Devtron permission group. This means you can't manually adjust or add individual permissions for users mapped to a permission group.
SSO login requires exact matching between Devtron permission group names and LDAP user groups. Any discrepancies or missing groups will prevent successful login.
Once you save the configuration with this auto-assign feature enabled, existing user permissions will be cleared and the future permissions will be managed through Permission Groups linked to LDAP user groups.
If you're missing some permissions that you know you should have, try logging out and signing back in to Devtron. This will refresh your permissions based on your latest LDAP user group.
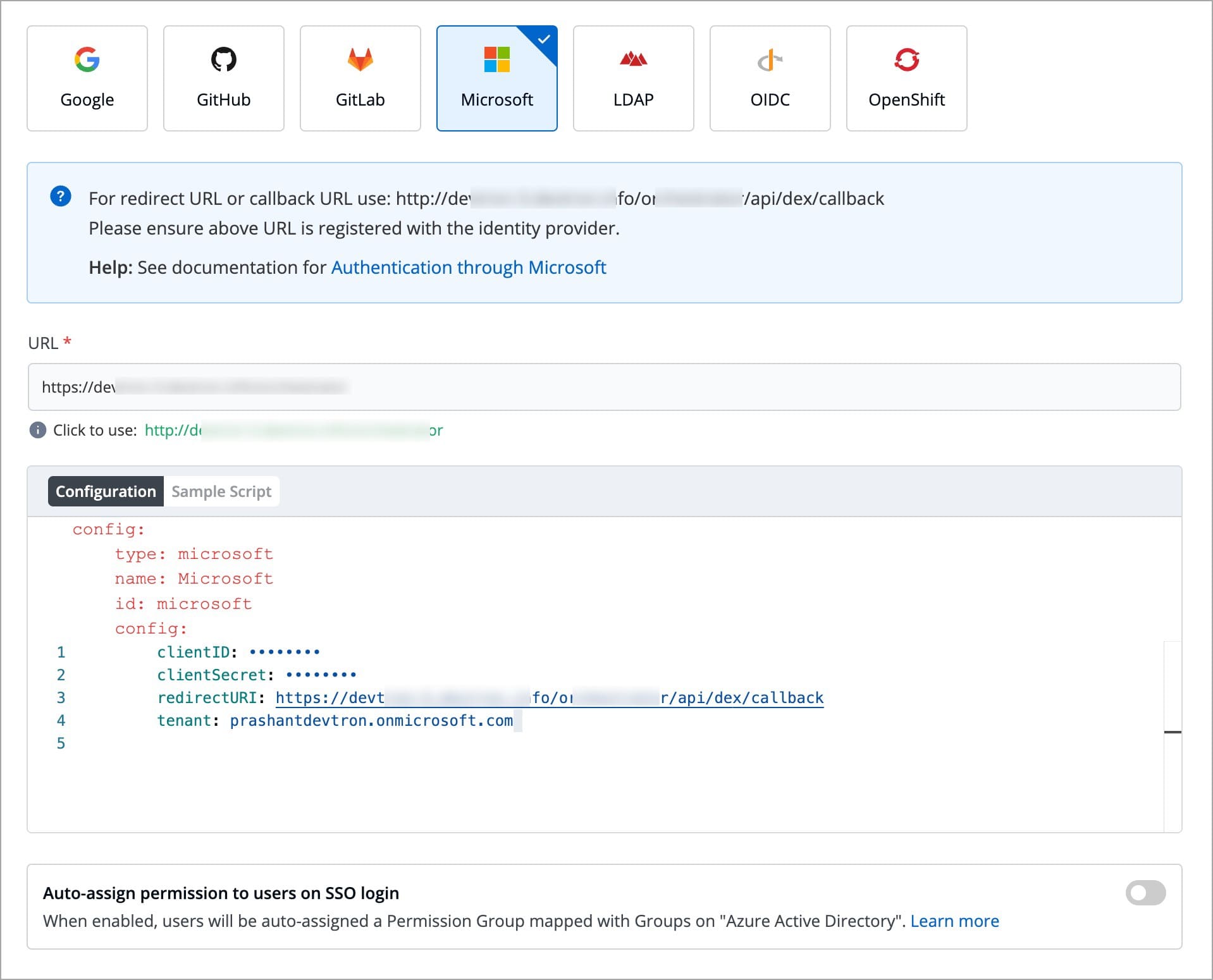
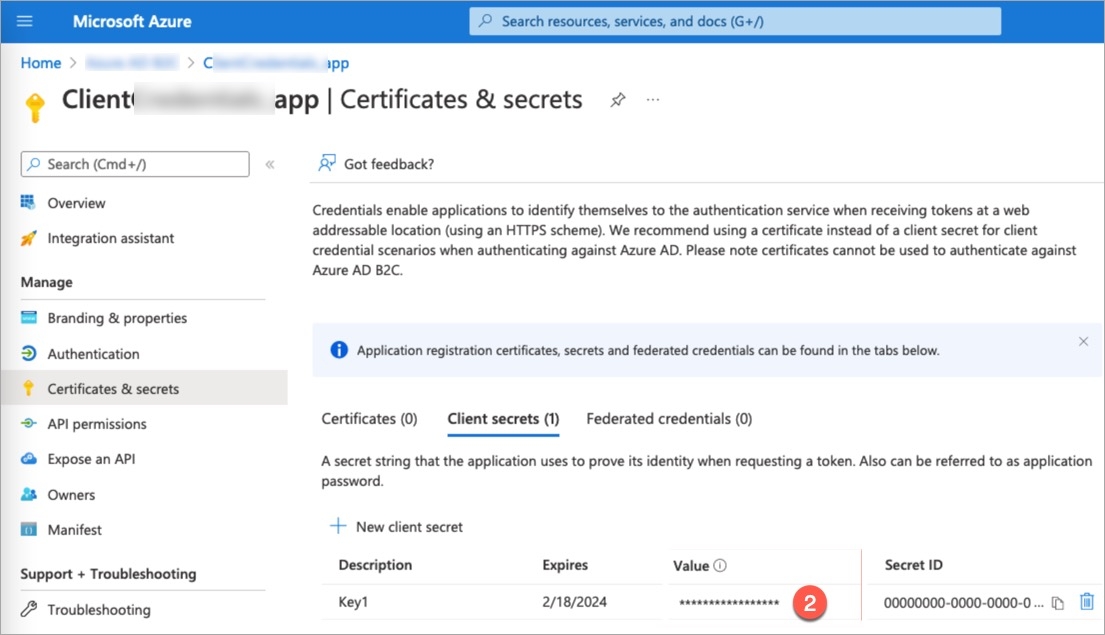
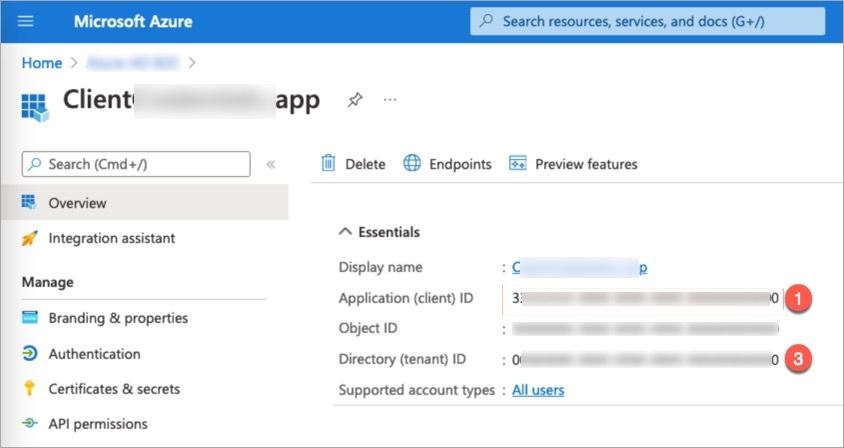
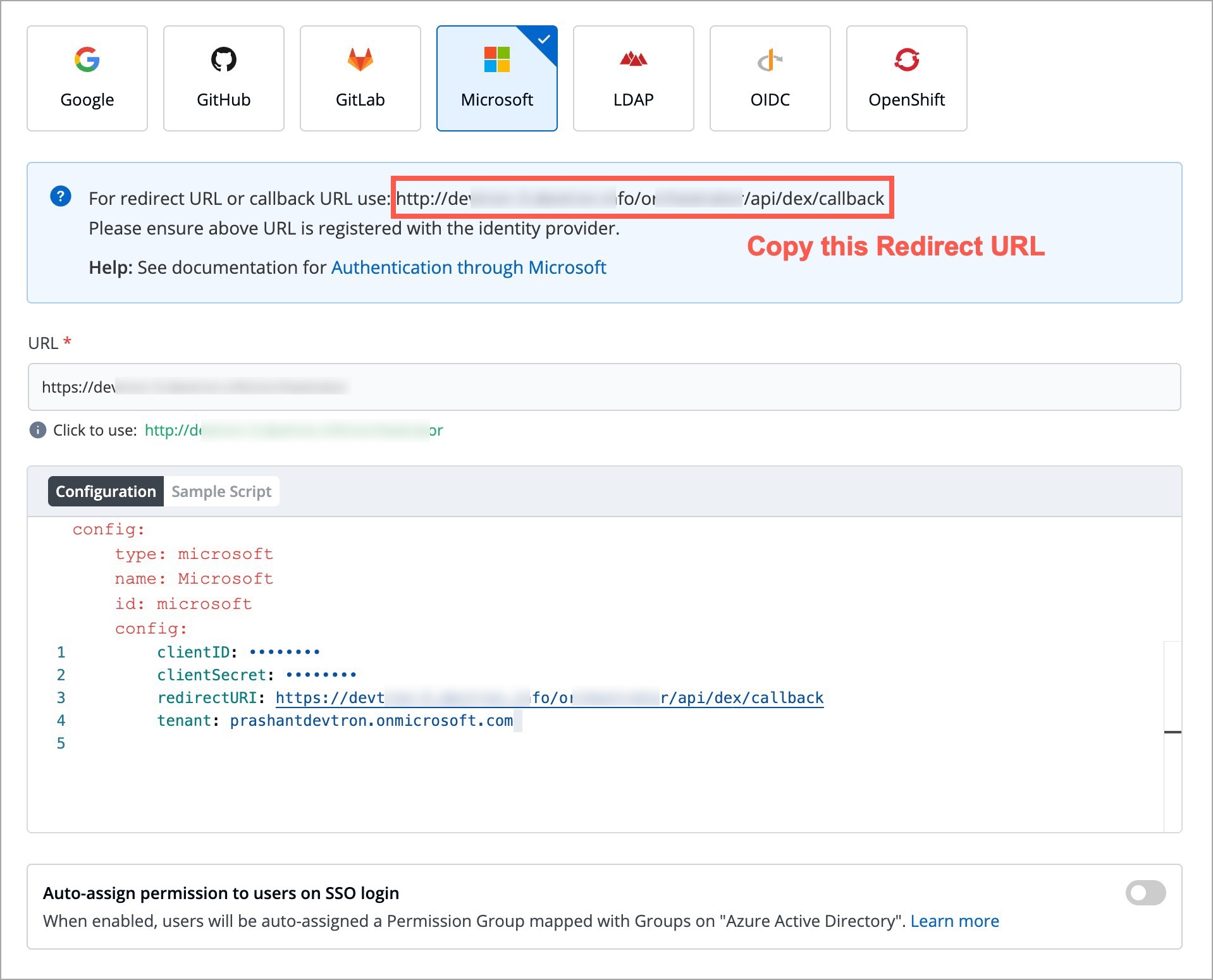
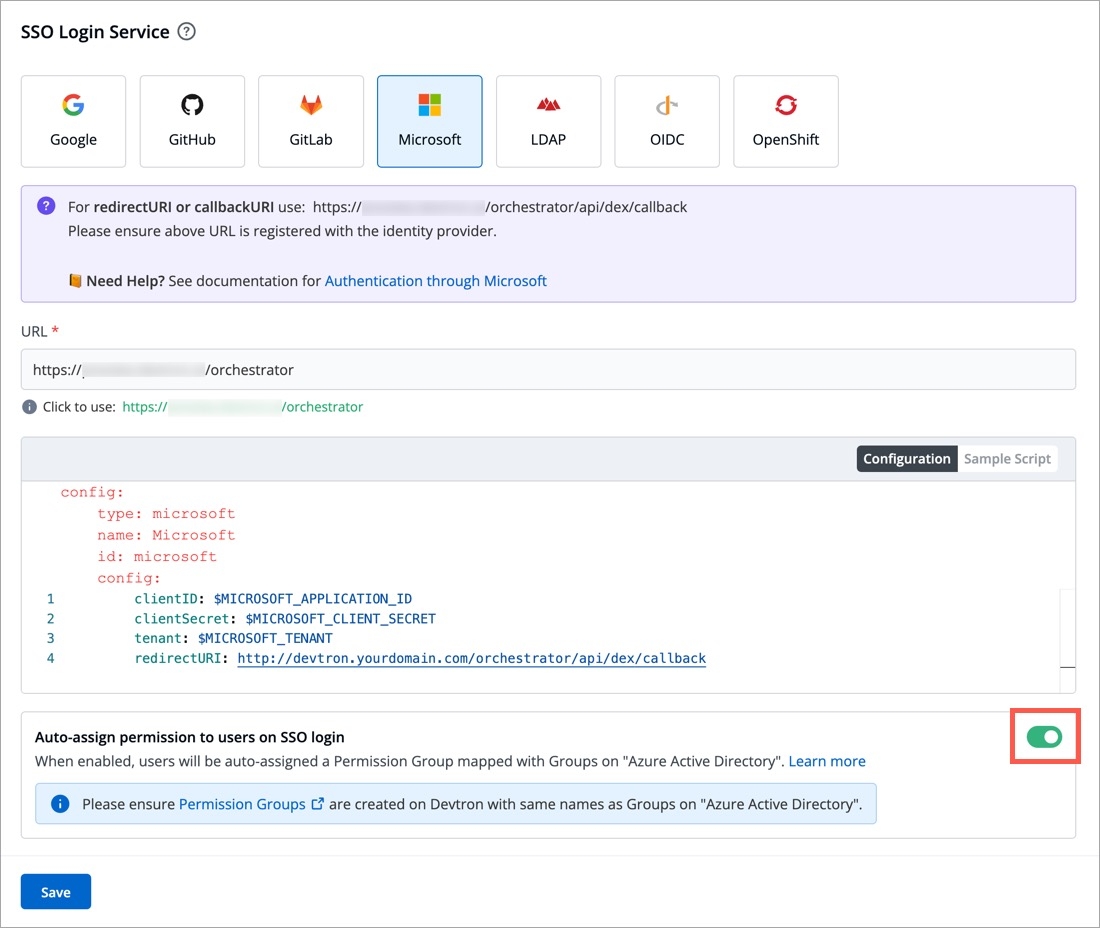
Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
tenantID (required only if you want to use Azure AD for auto-assigning permissions)
clientSecret
redirectURI (provided in SSO Login Services by Devtron)
Make sure to add tenantID in the SSO configuration field without fail.
Since Microsoft supports Active Directory (AD) , this feature further simplifies the onboarding process of organizations having a large headcount of users. It also eliminates repetitive permission assignment by automatically mapping your Azure AD groups to Devtron's Permission Groups during single sign-on (SSO) login.
If you've defined groups in your Active Directory, you can create corresponding permission groups in Devtron with the same names. When members of those Active Directory groups first log in to Devtron, they'll automatically inherit the permissions from their Devtron permission group. This means you can't manually adjust or add individual permissions for users mapped to a permission group.
SSO login requires exact matching between Devtron permission group names and AD groups. Any discrepancies or missing groups will prevent successful login.
Once you save the configuration with this feature enabled, existing user permissions will be cleared and the future permissions will be managed through permission groups linked to Azure Active Directory (Microsoft Entra ID) groups.
If your AD permissions aren't reflecting in Devtron, a quick sign-out and sign-in can resolve the issue.
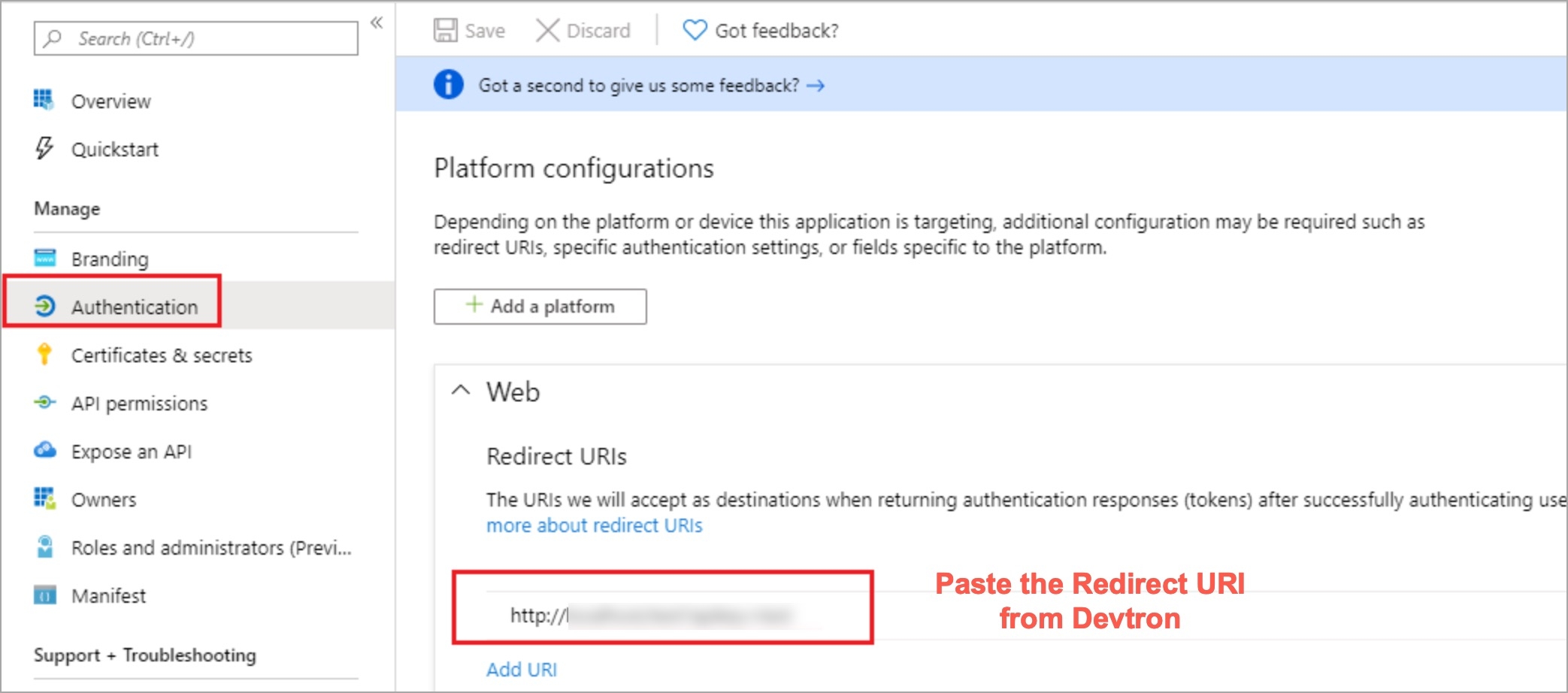
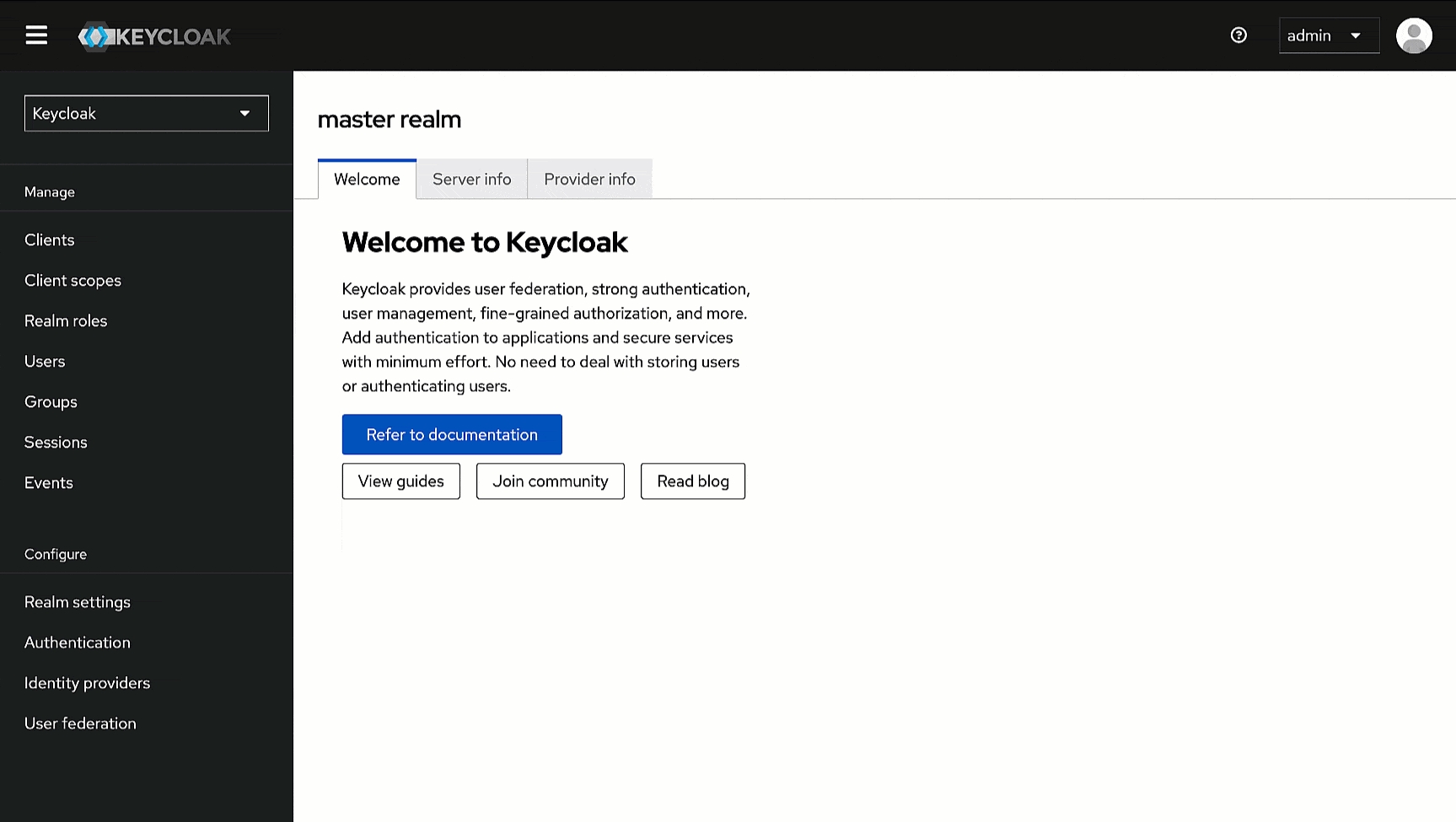
Install and configure Keycloak on your server or cloud environment.
Create a new realm in Keycloak for your application.
Here, we will add Devtron as a client for using Keycloak SSO.
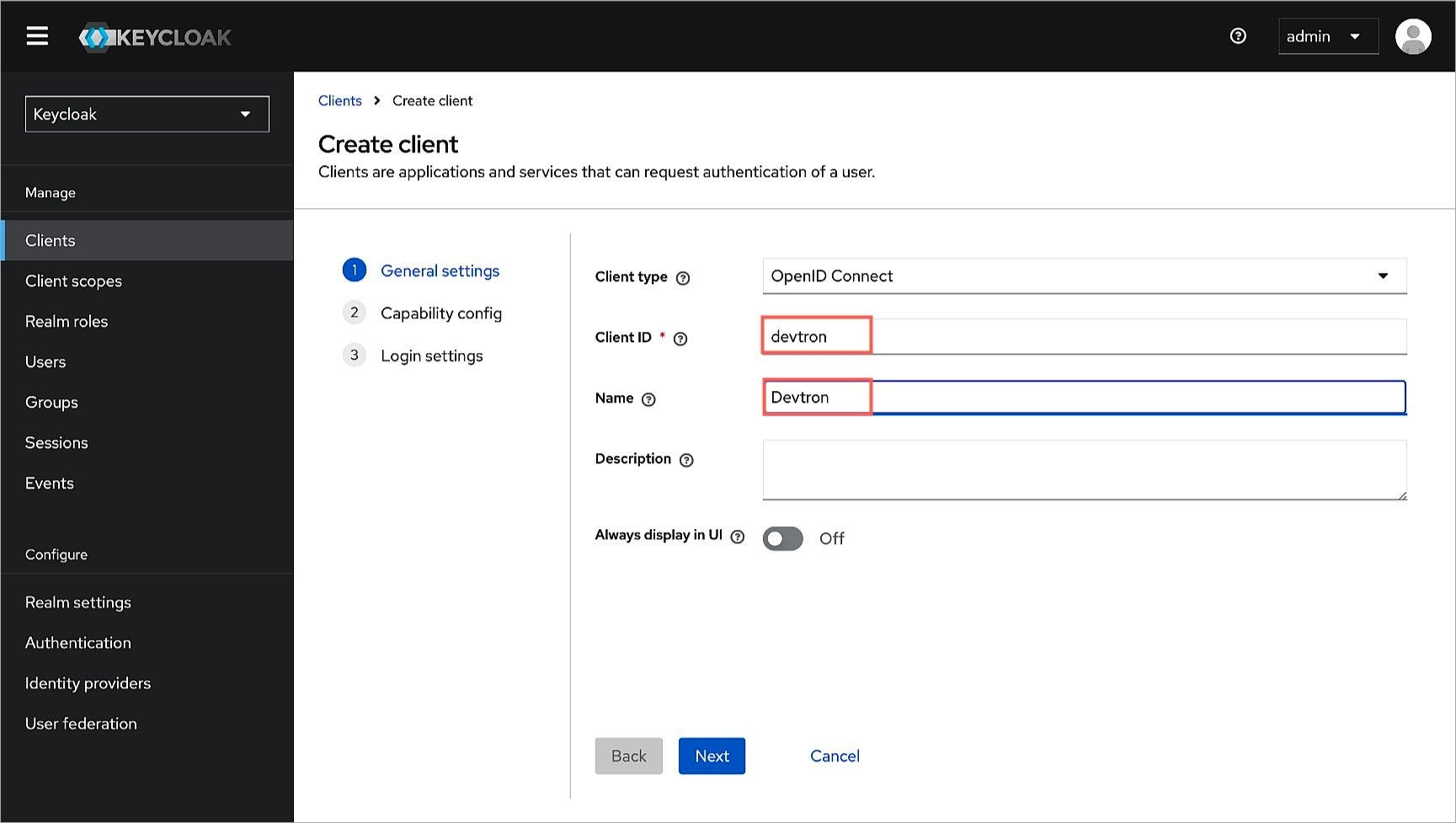
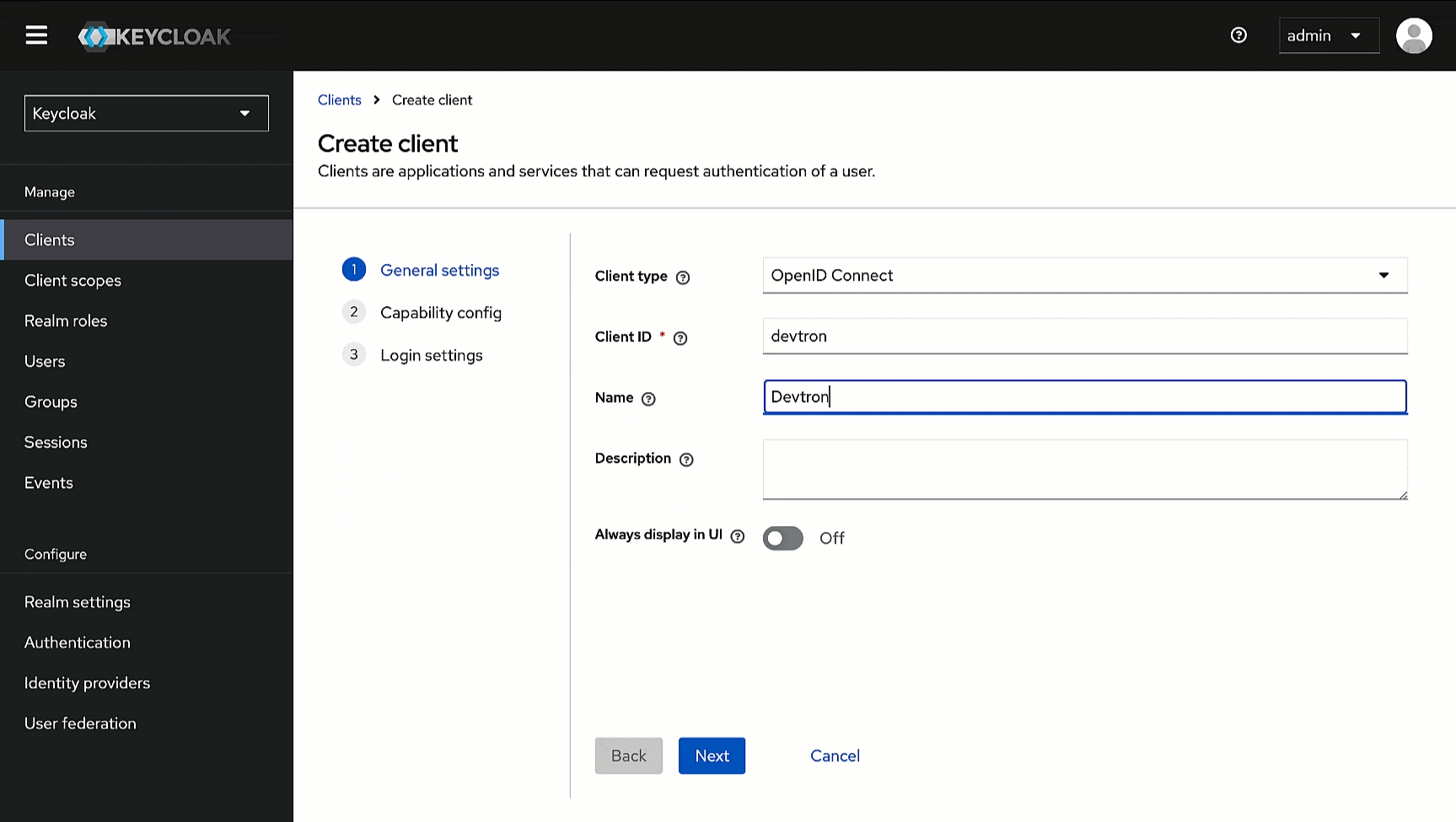
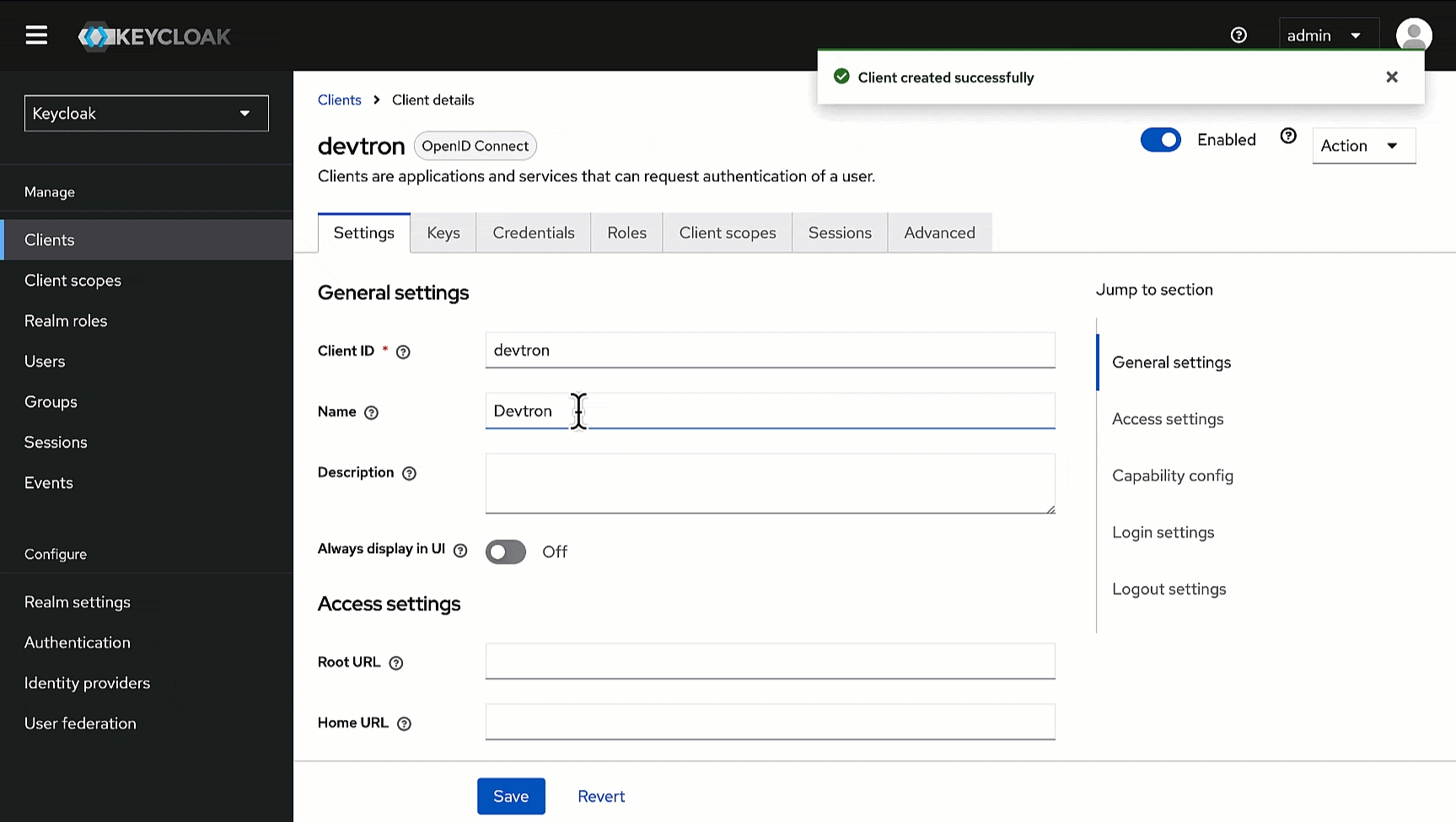
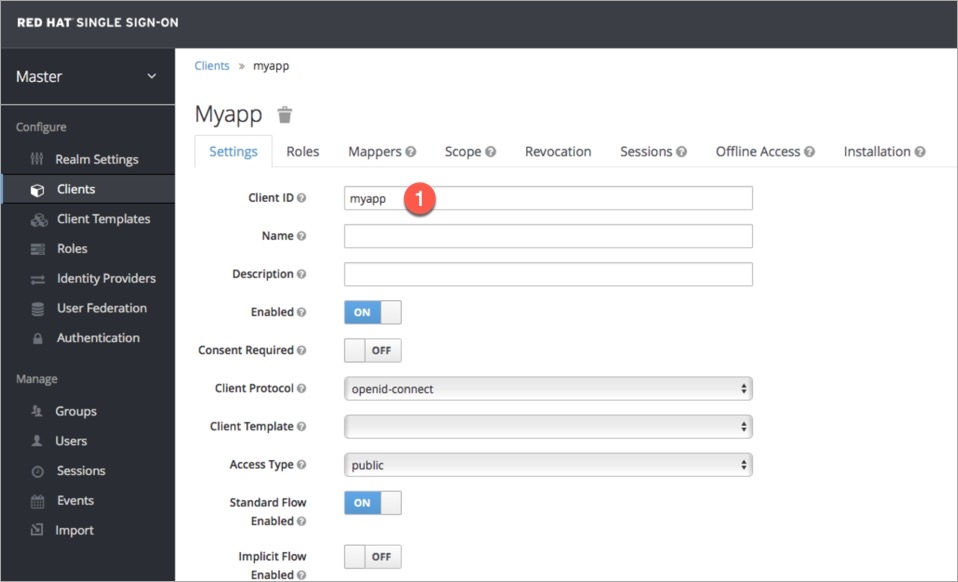
In the Admin Console, go to Clients and click Create client.
Within General Settings:
Enter devtron in the Client ID field. We will use this ID while configuring SSO later in Devtron.
Enter Devtron in the Name field.
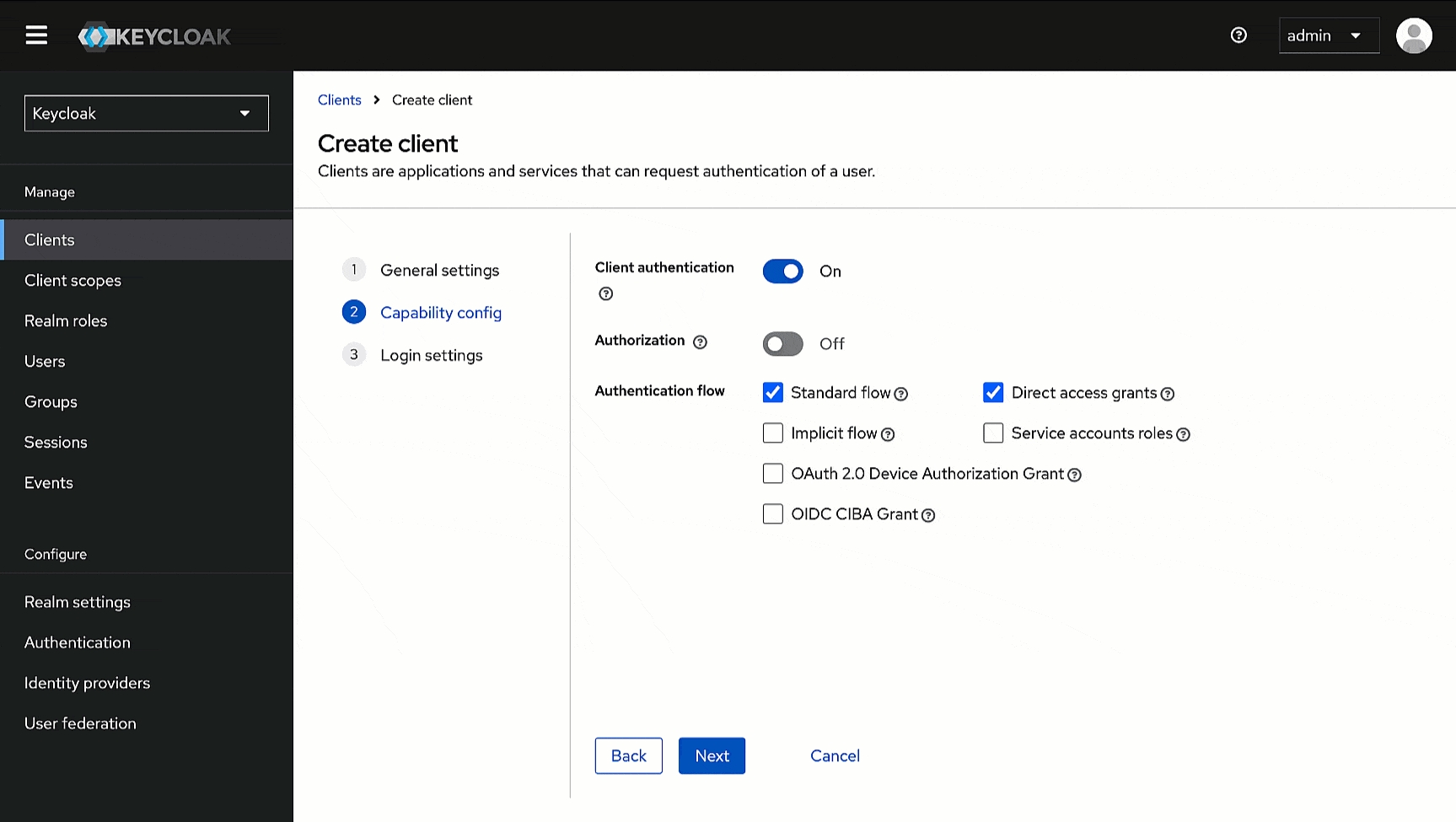
Within Capability config, turn on Client Authentication.
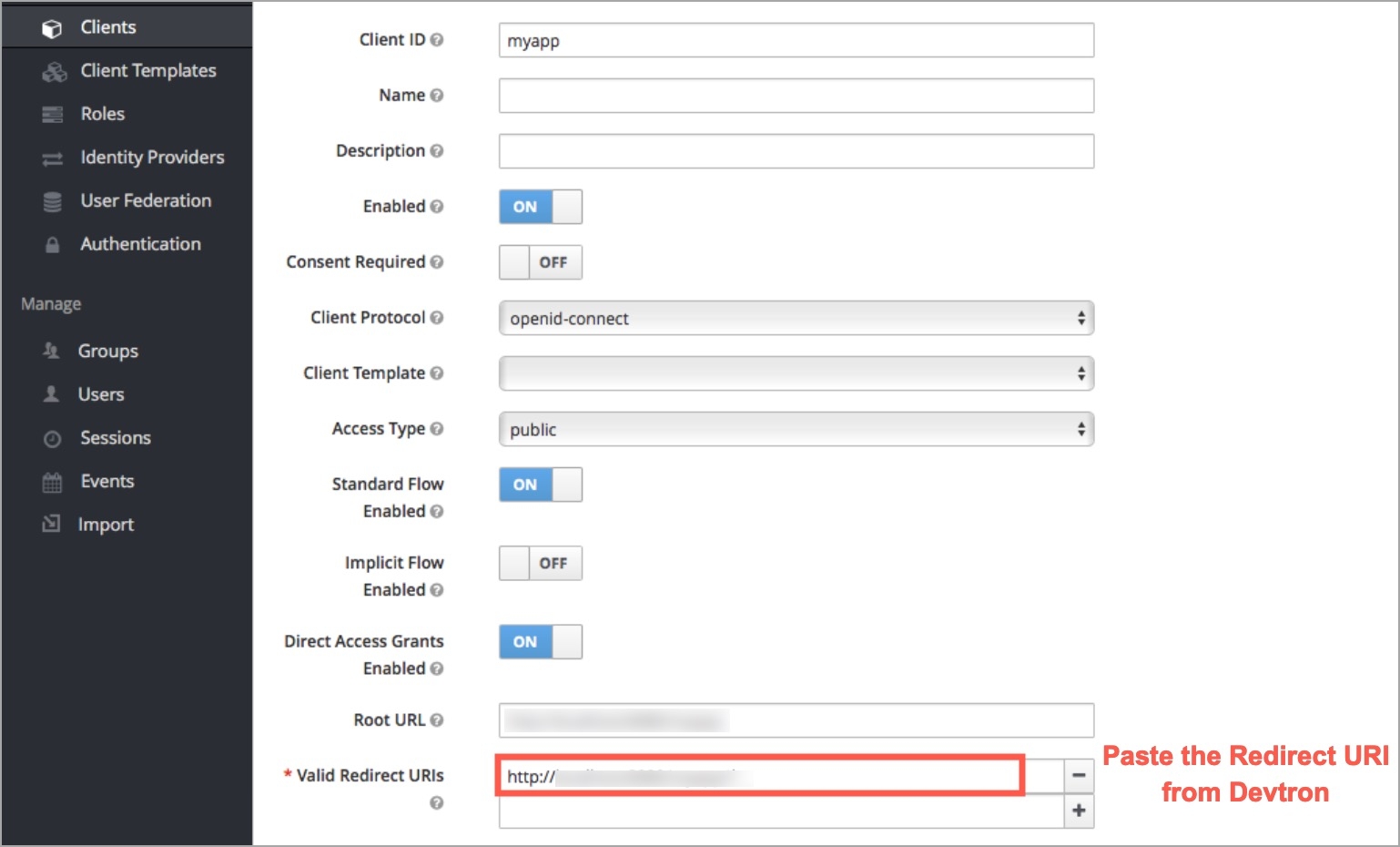
Within Login settings, enter https://<DEVTRON_BASE_URL>/orchestrator/api/dex/callback in the following fields.
Valid redirect URIs
Valid post logout redirect URIs
Web origins
Click here to know where to find DEVTRON_BASE_URL.
Click Save.
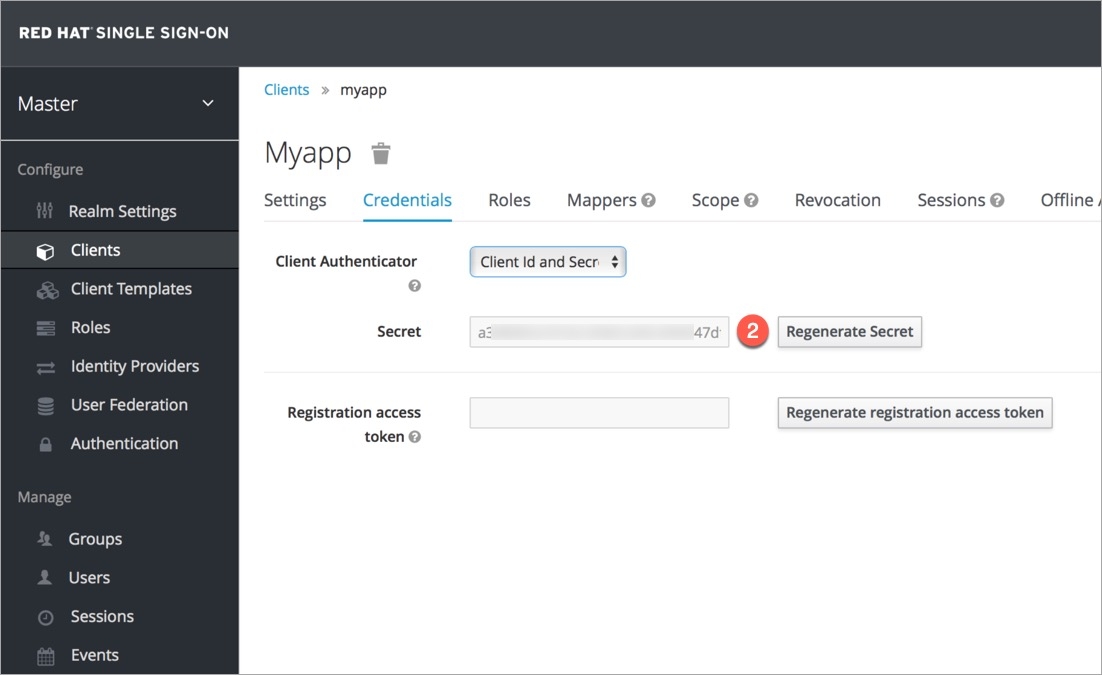
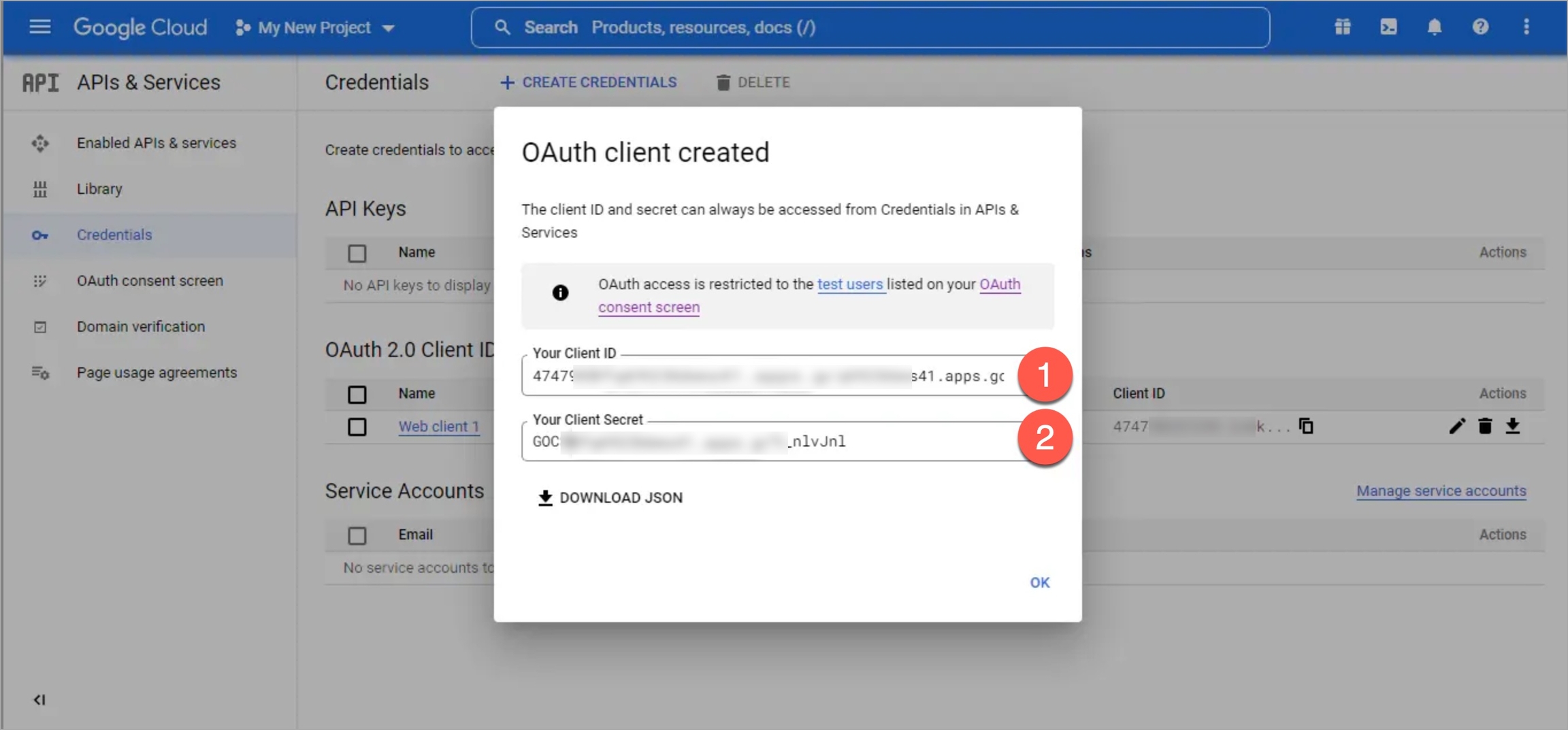
Here, we will obtain the secret we need while configuring SSO in Devtron.
Go to the Credentials tab of the client you created.
Use the copy button next to the Client Secret field and paste it somewhere for future reference.
Here, we will create a user that can log in to Devtron via SSO. We will assign a username and password that the user can enter while logging in to Devtron via Keycloak SSO.
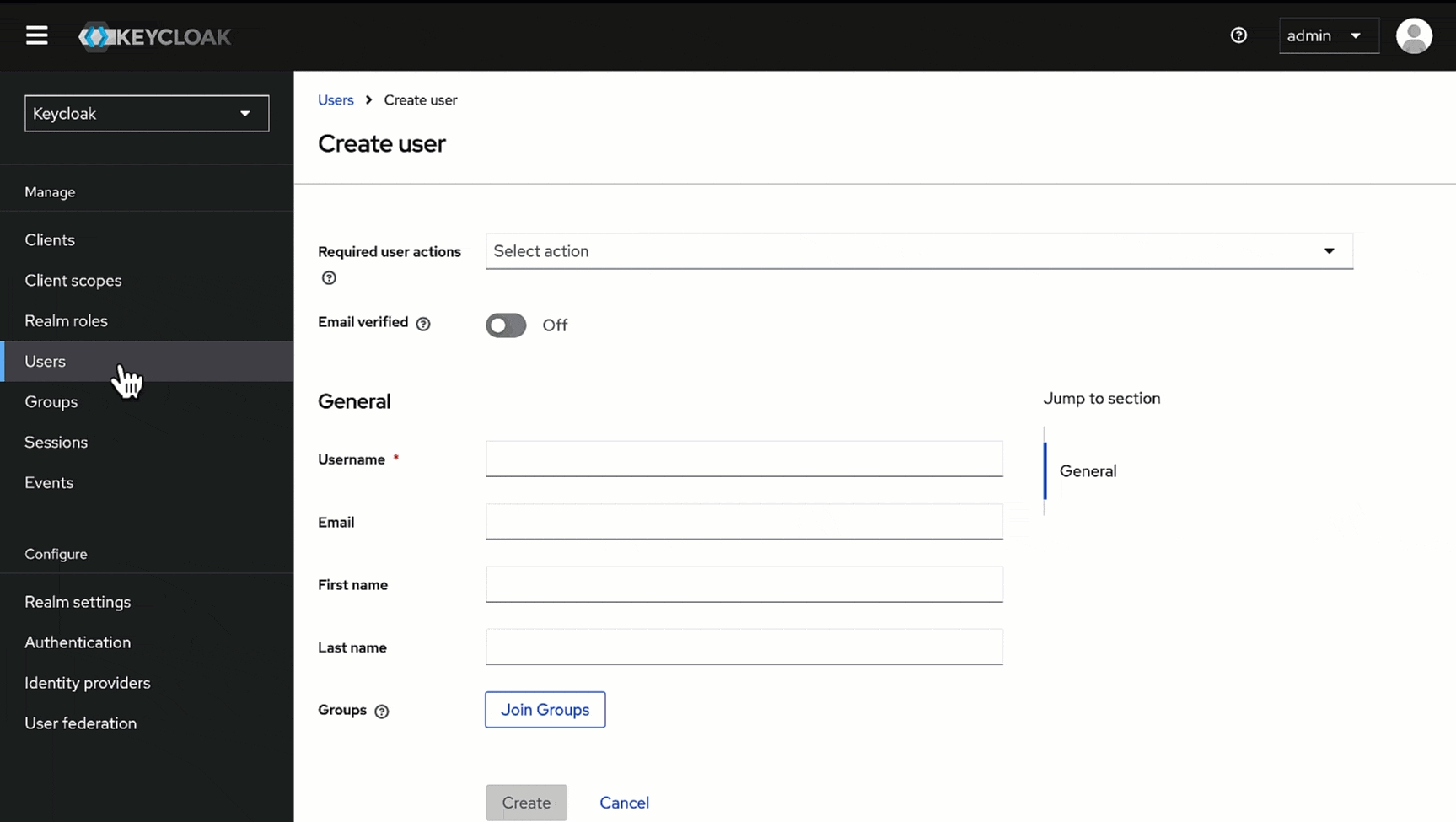
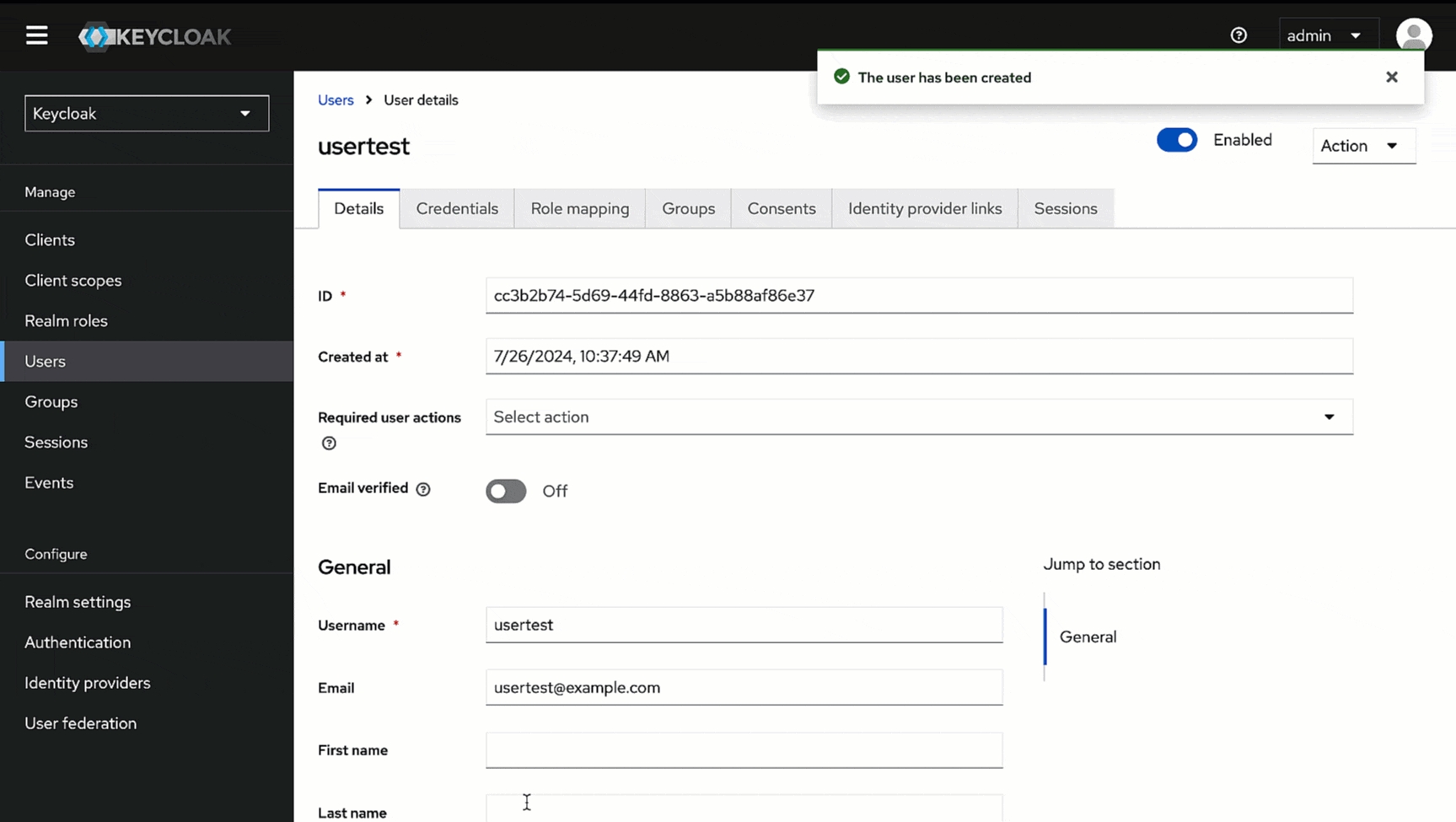
In the Admin Console, go to Users and click Add user.
Give a username (e.g., usertest) in the Username field and enter the user's email address (e.g., usertest@example.com) in the Email field.
Click Create. Your user creation will be successful.
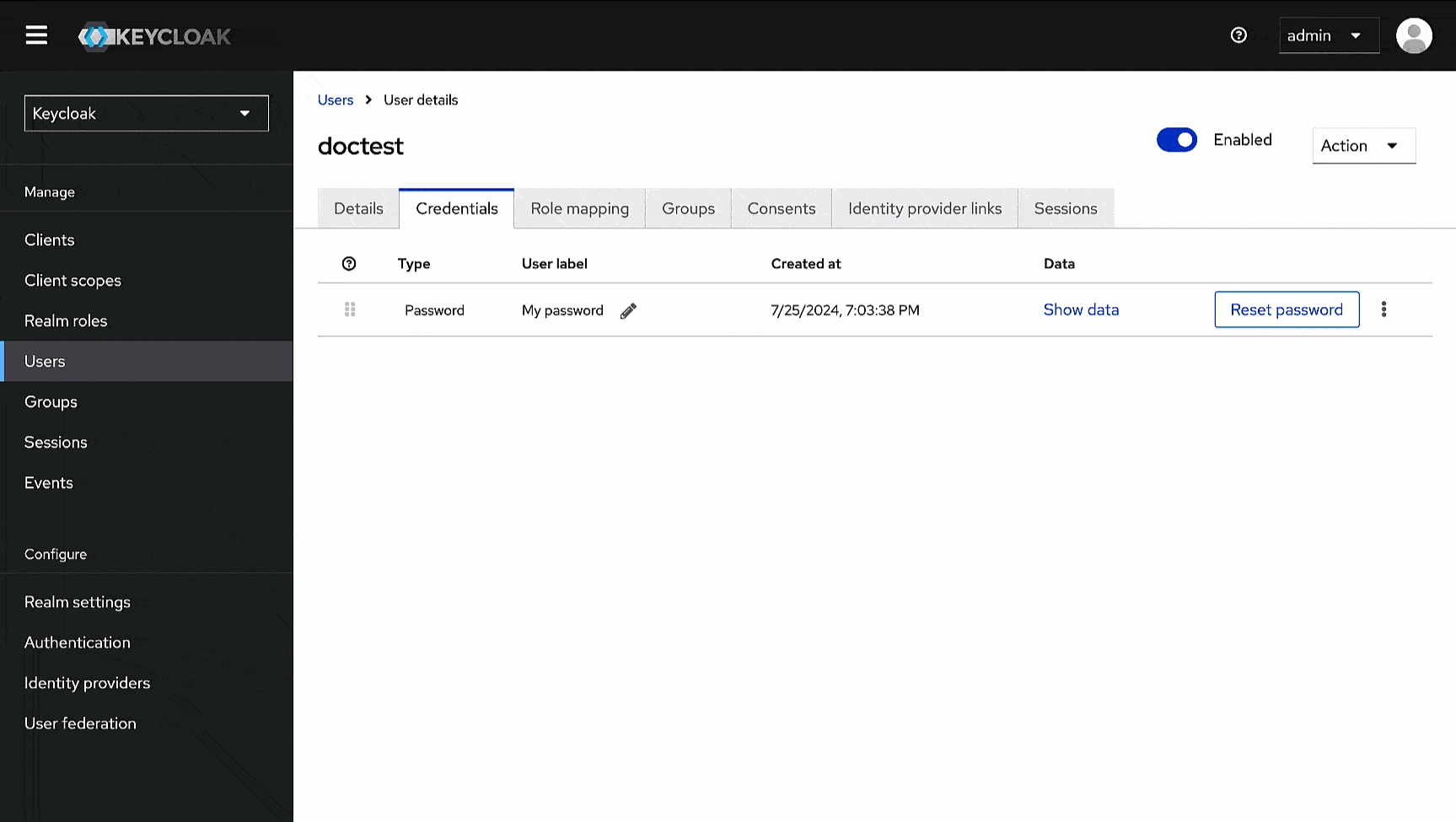
Go to the Credentials tab of the user you created.
Click Set password.
Enter the password and confirm it.
Click Save.
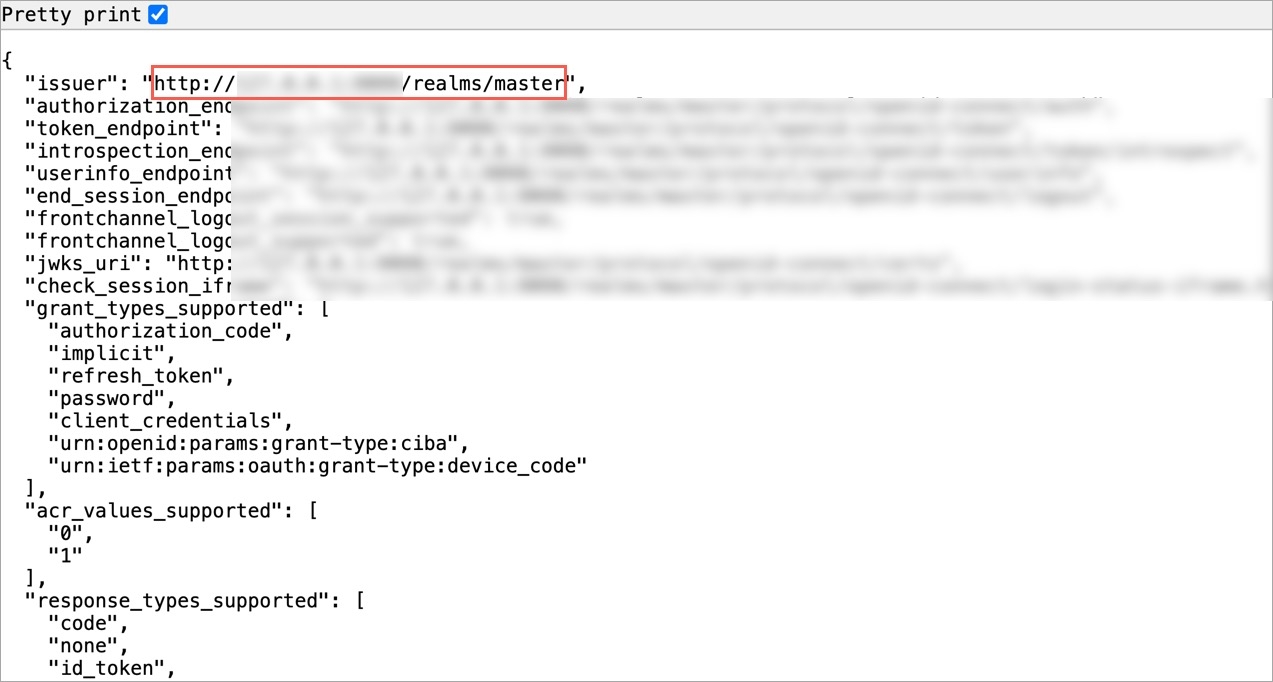
Here, we will obtain the Issuer URL we need while configuring SSO in Devtron.
In the Admin Console, go to Realm settings.
In the General tab, scroll down to the Endpoints field, and click the OpenID Endpoint Configuration link.
This will open a new page, copy the value of the key named issuer, and paste it somewhere for future reference.
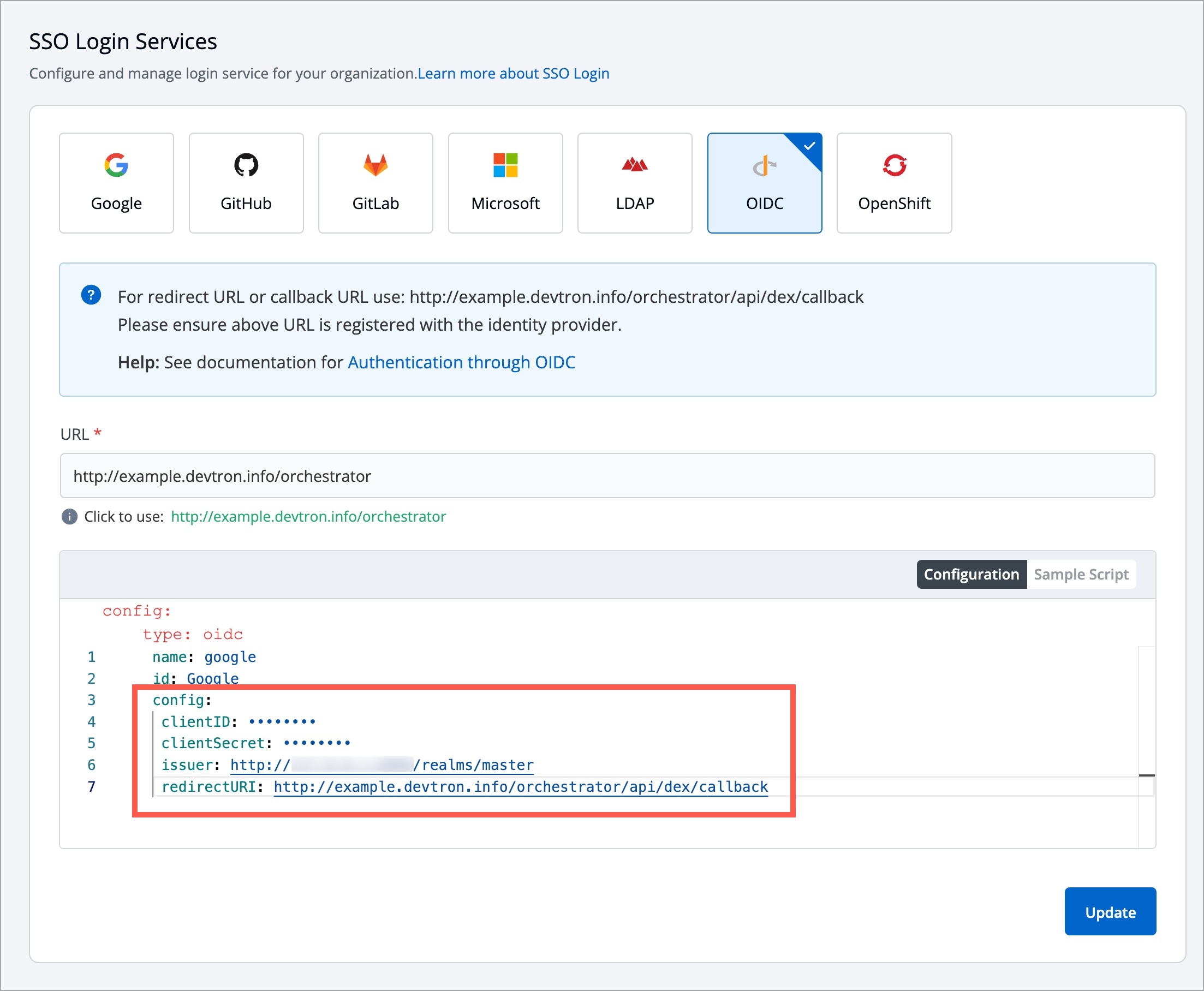
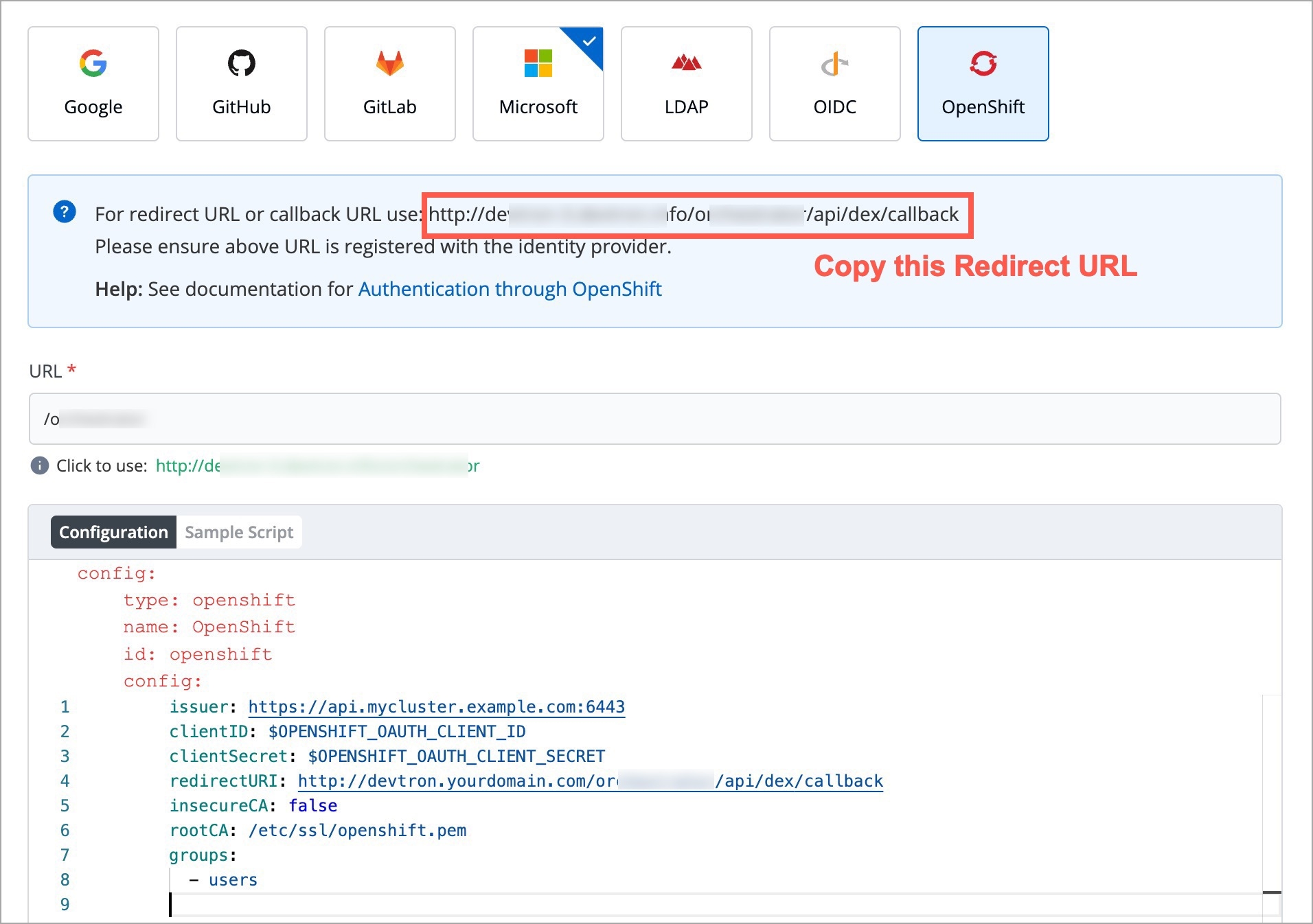
Here, we will set up an OIDC SSO and enter the values we obtained in the previous section.
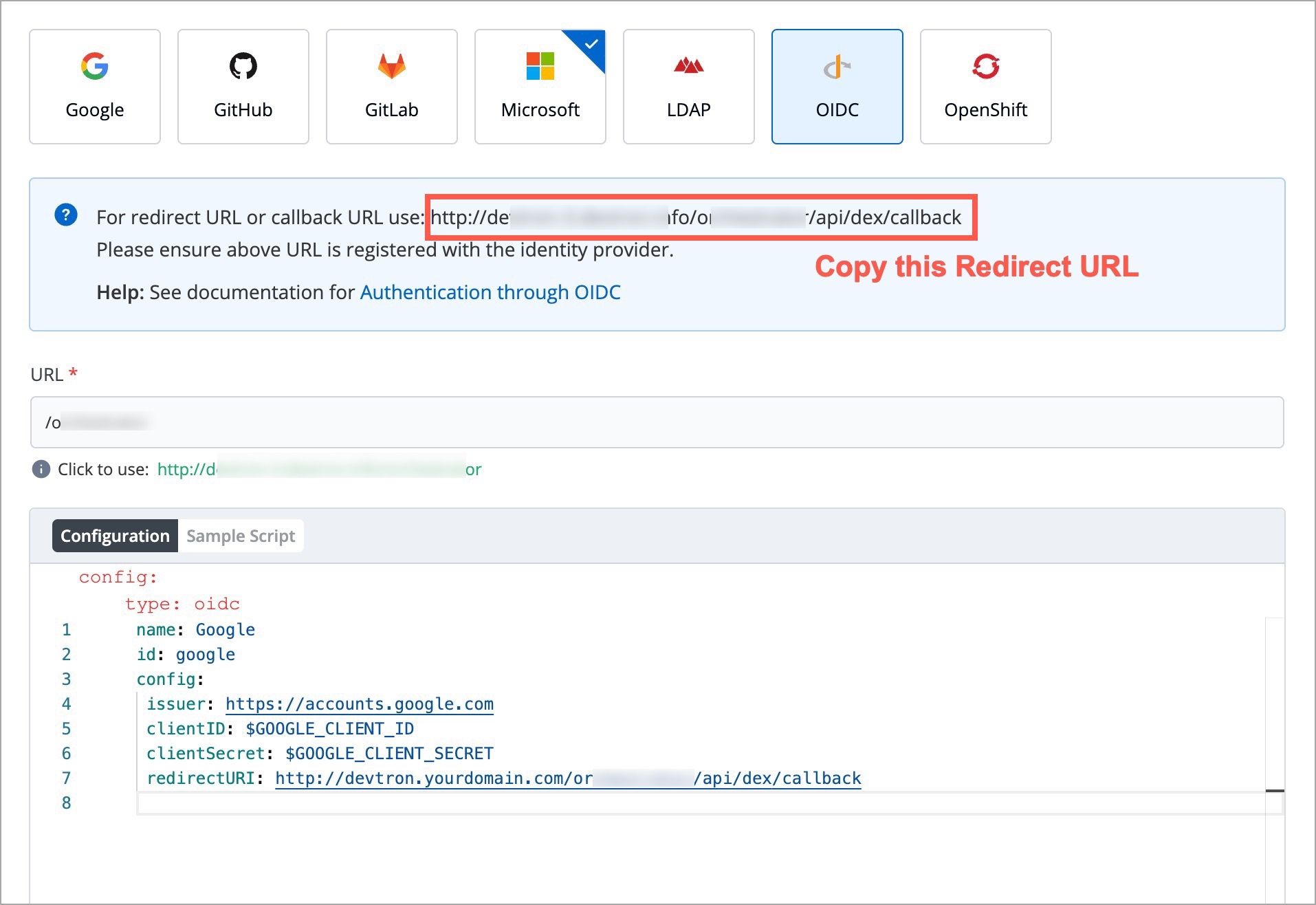
Go to Global Configurations → SSO Login Services → OIDC.
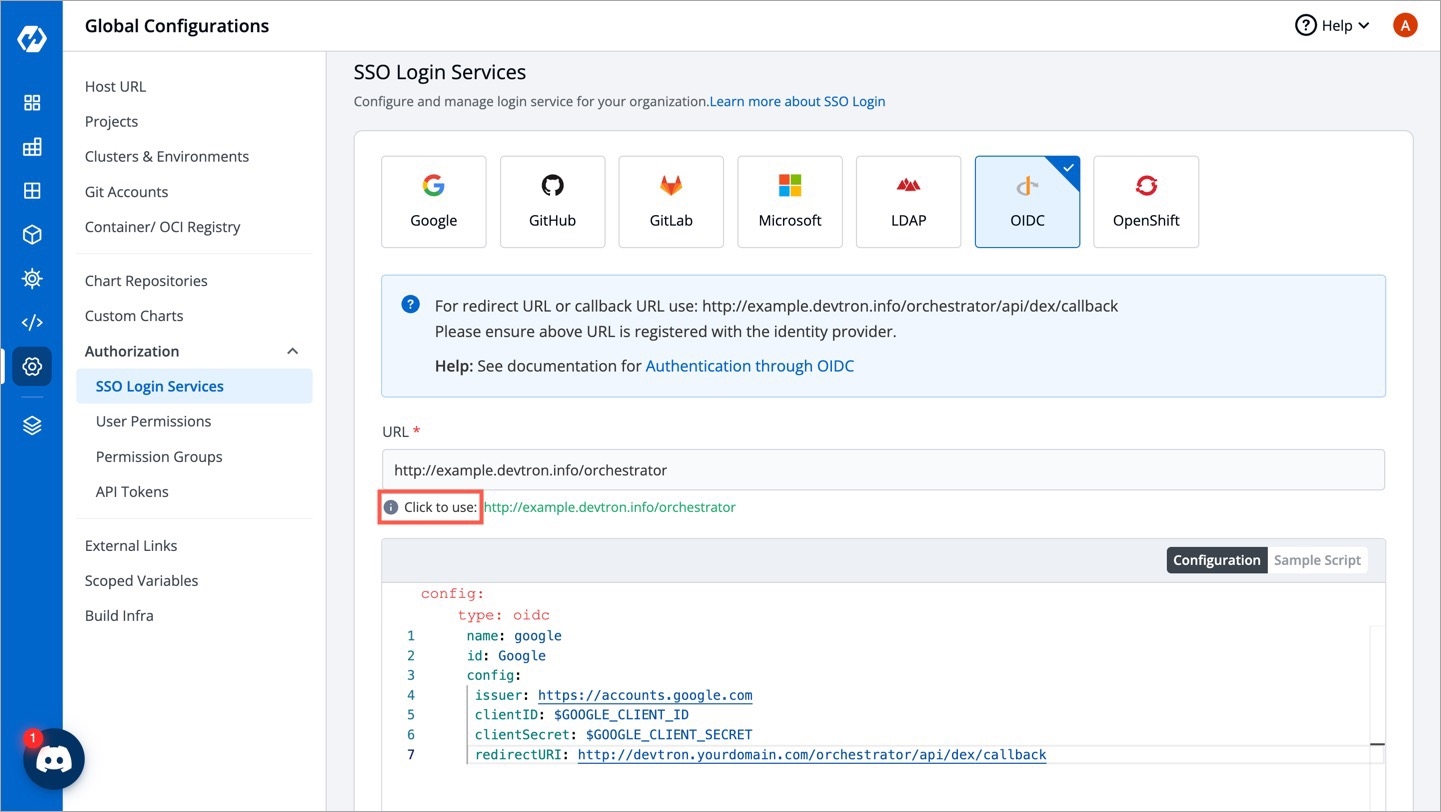
Below the URL field, take the help of the Click to use option to populate the exact URL if the displayed one is incorrect.
In the Configuration editor, do the following:
In the issuer field, paste the URL you got while retrieving issuer URL.
In the clientID field, paste the ID you entered while creating the client.
In the clientSecret field, paste the secret you got under client credentials tab.
In the redirectURI field, make sure to enter the same redirect URI you gave in step 4 of client creation.
Click Save or Update to activate Keycloak SSO login.
Here, we will add the user we created in the Keycloak Admin Console. If this step is skipped, the user might not be able to log in to Devtron via Keycloak.
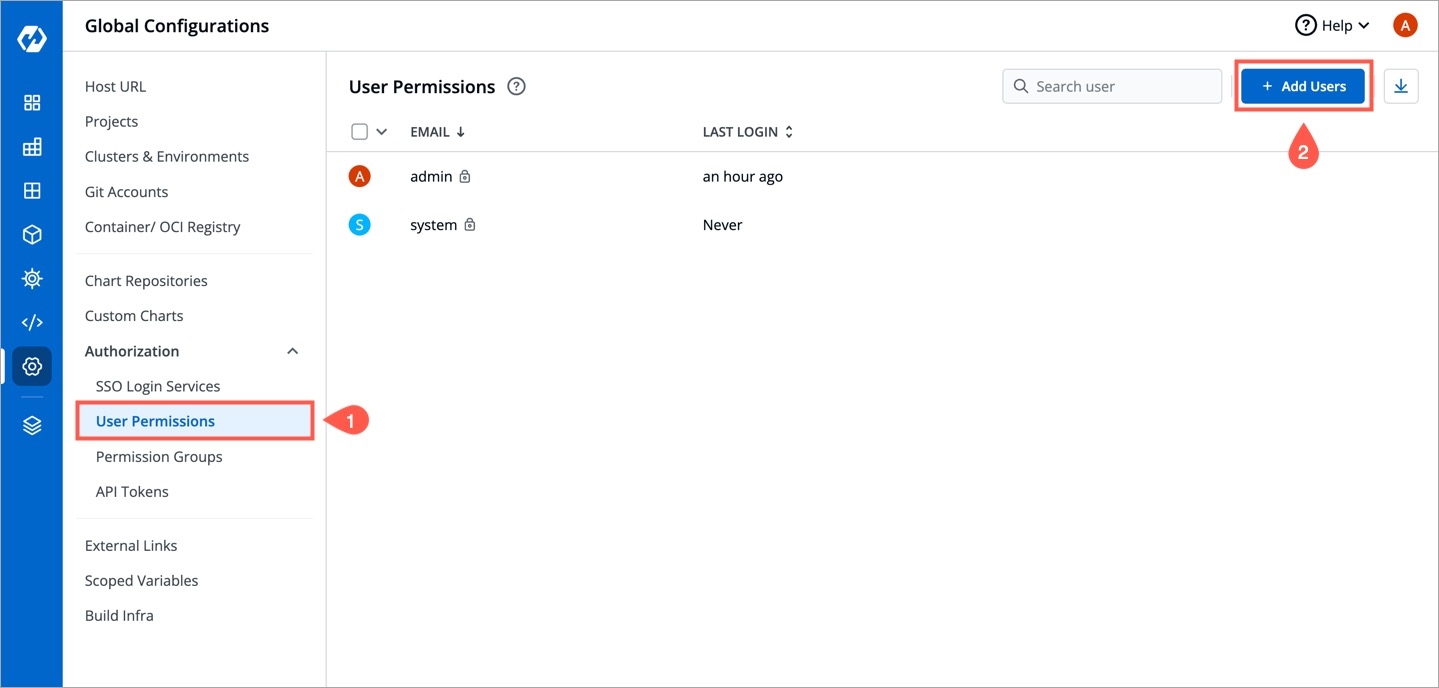
Go to Global Configurations → Authorization → User Permissions.
Click + Add Users.
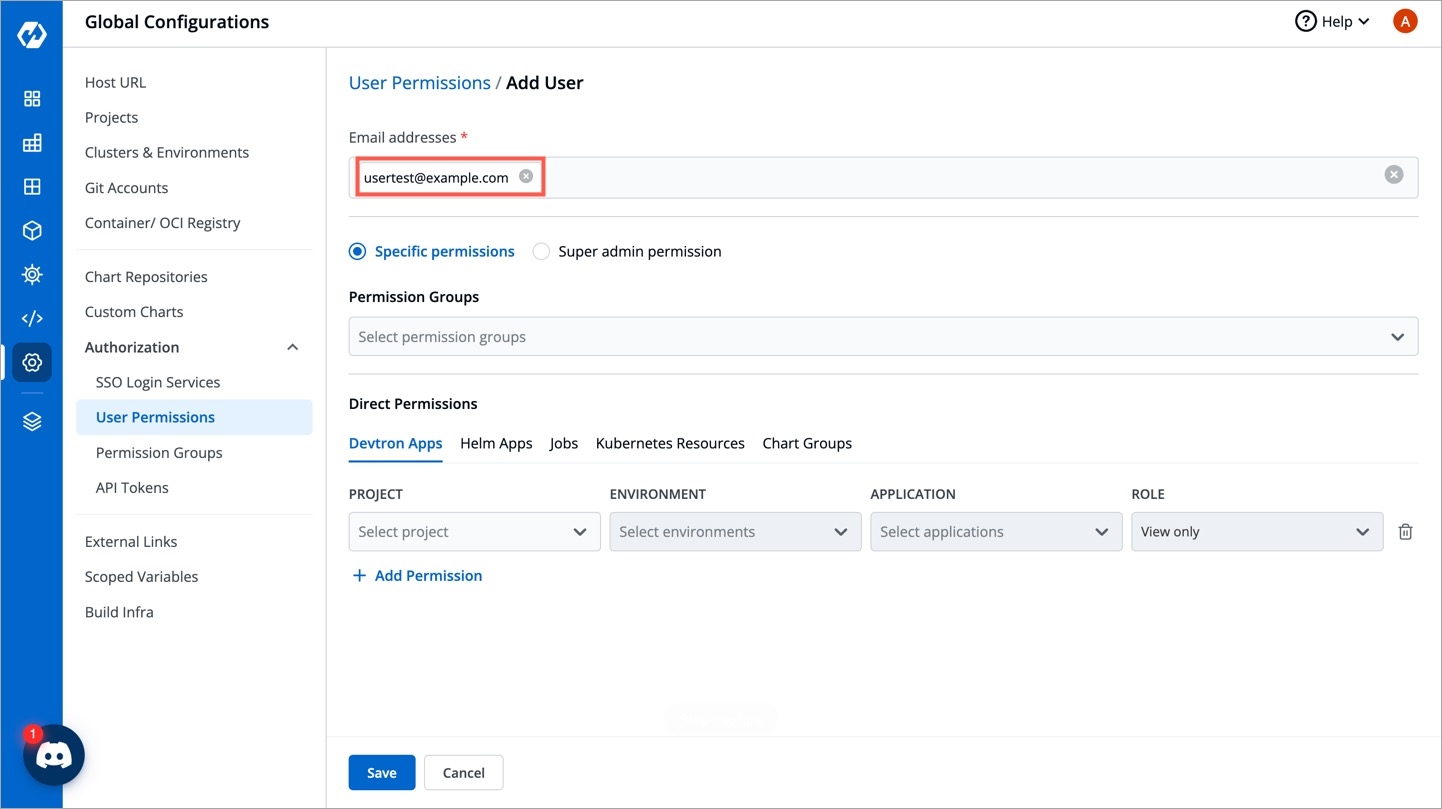
In the Email addresses field, enter the email address of the user you created in Keycloak.
Assign necessary permissions to this new user. Refer user permissions to know more.
Click Save.
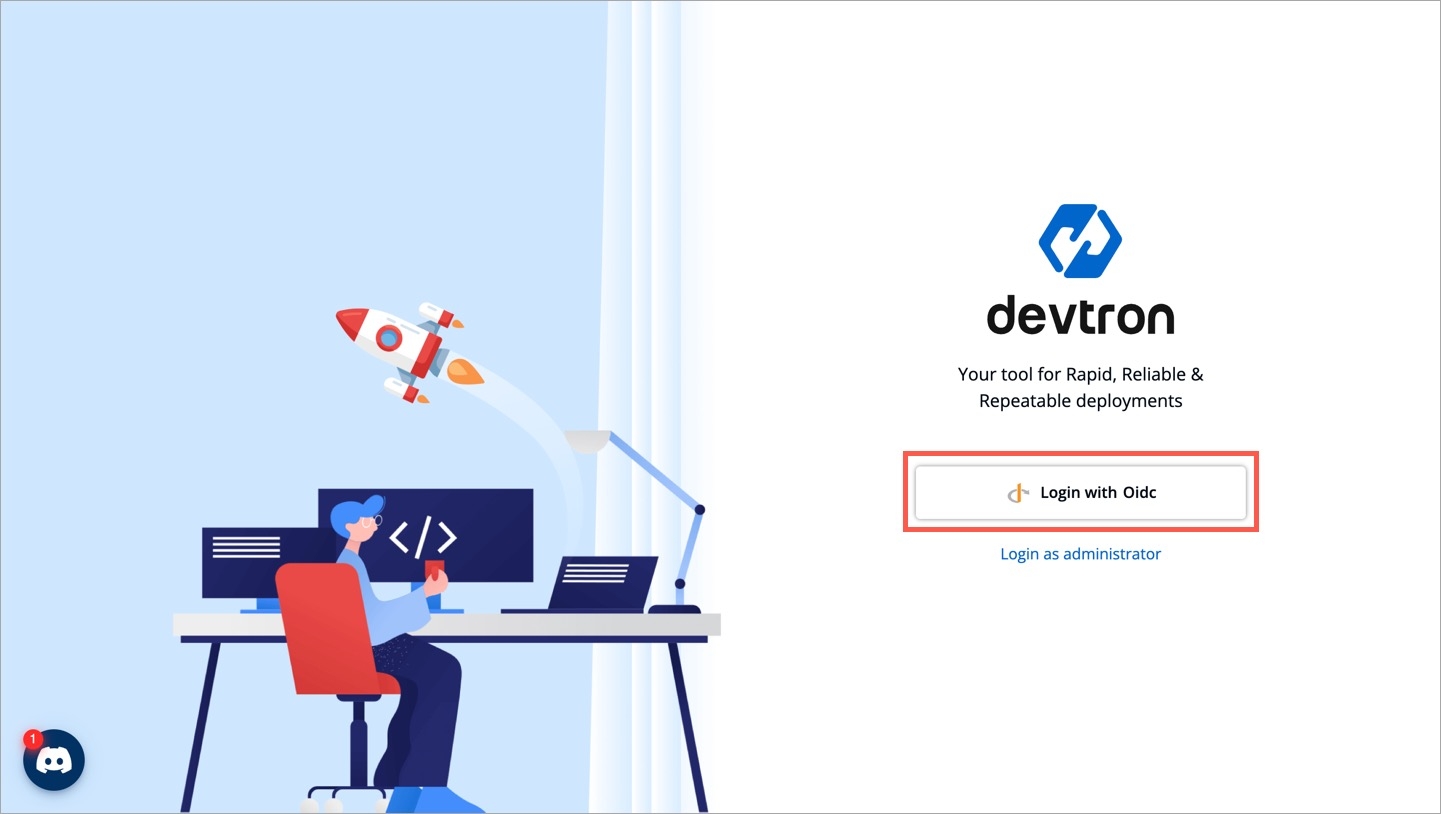
Now, you may log out and test the Keycloak OIDC login method using the user credentials. Clicking the Login with Oidc button will land you on Keycloak's login page.
A verified account on Okta. Okta activates your account only if email verification is successful.
Here's a reference guide to set up your Okta org and application: Link
Once your Okta org is set up, create an app integration on Okta to get a Client ID and Client Secret.
In the Admin Console, go to Applications → Applications.
Click Create App Integration.
Select OIDC - OpenID Connect as the Sign-in method.
OIDC stands for OpenID Connect. Click here to read more.
Select Web as the application type and click Next.
On the App Integration page:
Give a name to your application.
Select the Interaction Code and Refresh Token checkbox.
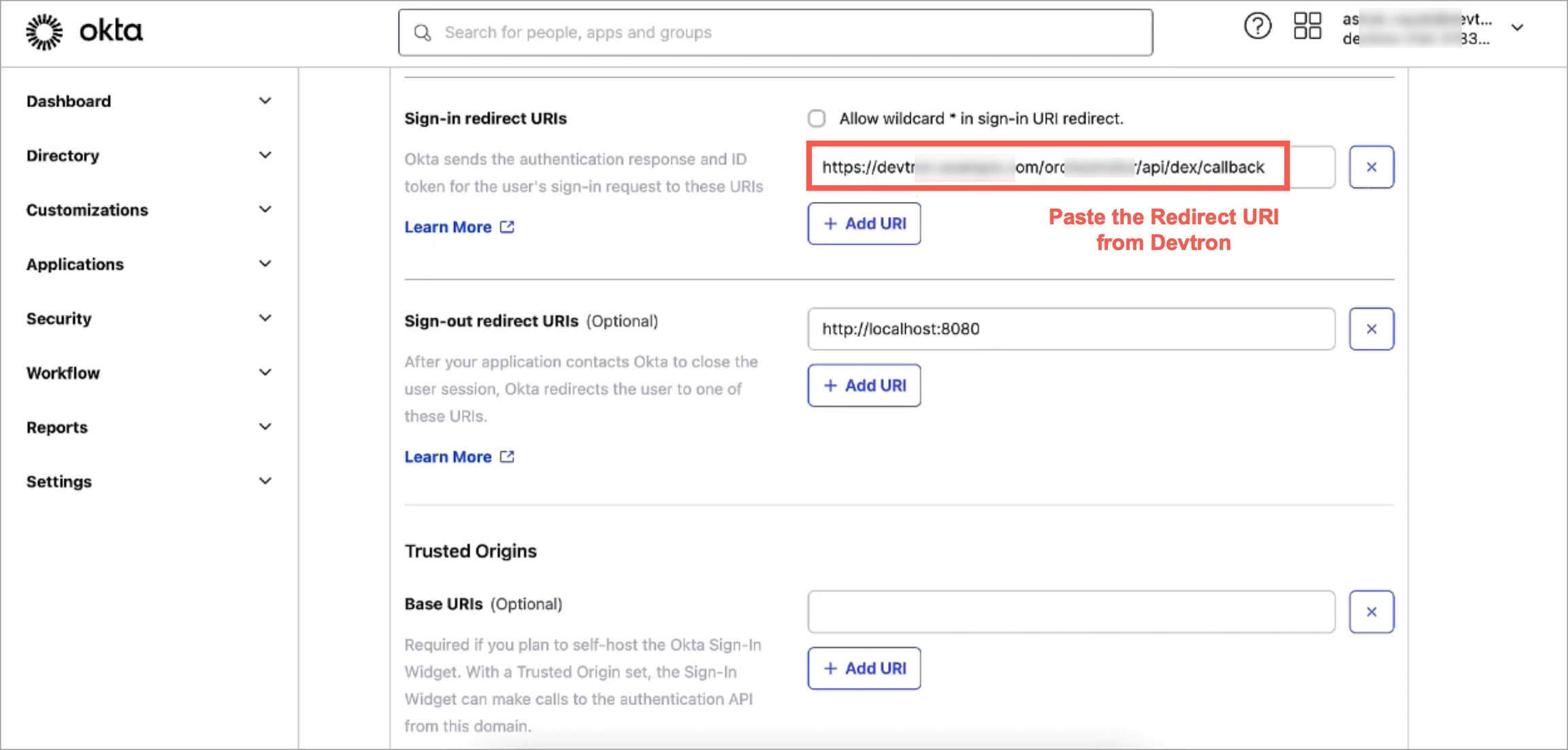
Now go to Devtron's Global Configurations → SSO Login Services → OIDC.
Copy the redirect URI given in the helper text (might look like: https://xxx.xxx.xxx/xxx/callback).
Return to the Okta screen, and remove the prefilled value in Sign-in redirect URIs.
Paste the copied URI in Sign-in redirect URIs.
Click Save.
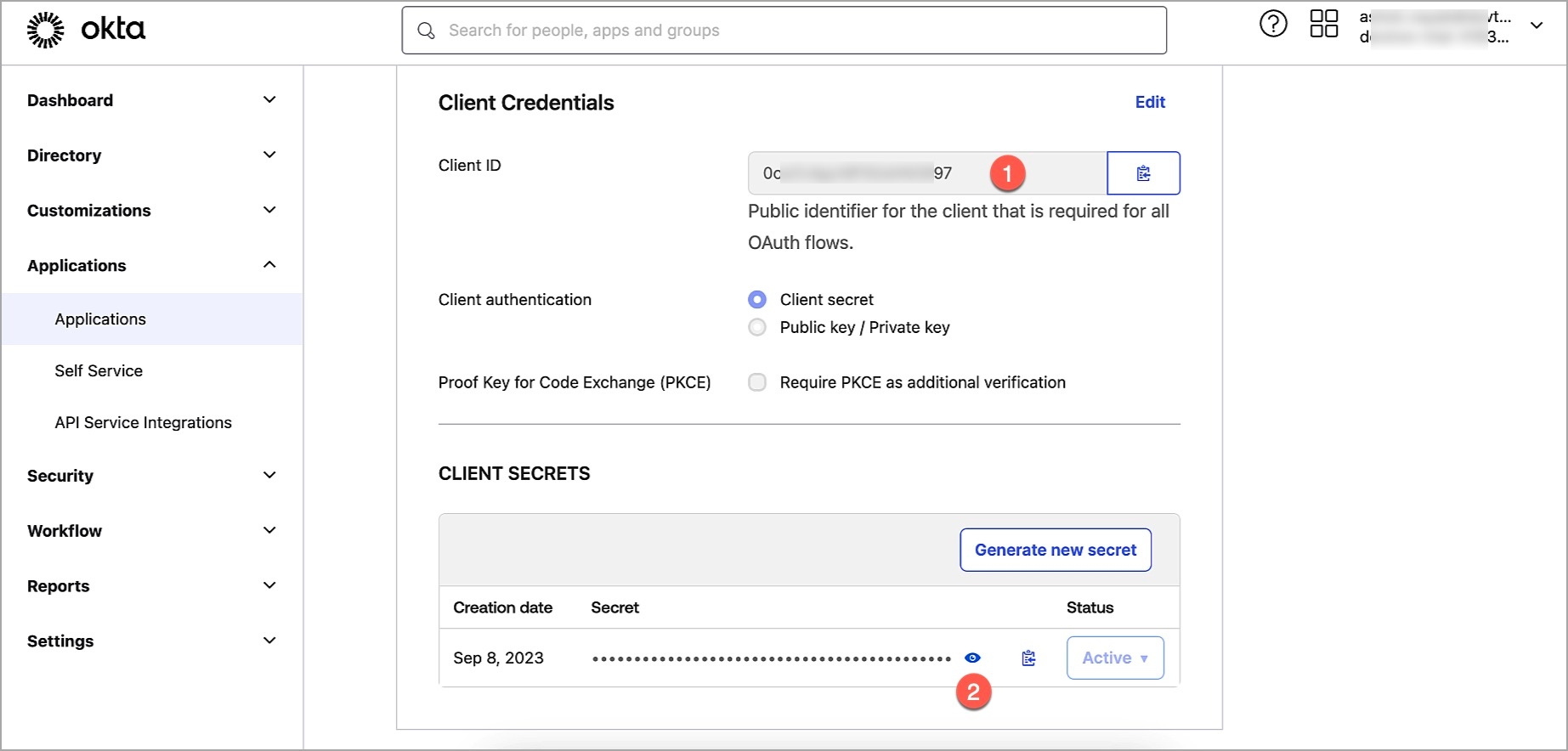
On the General tab:
Note the Client ID value.
Click the Edit option.
In Client Authentication, choose Client Secret.
Click Save.
Click Generate new secret.
Note the Client Secret value.
Go to the Global Configurations → SSO Login Services → OIDC.
In the URL field, enter the Devtron application URL (a valid https link) where it is hosted.
Under Configuration tab, locate the config object, and provide the clientID and clientSecret of the app integration you created on Okta.
Add a key insecureSkipEmailVerified: true. Note that this key is only required for Okta SSO. For other types of OIDC SSO, refer OIDC supported configurations.
Provide issuer value as https://${yourOktaDomain}. Replace ${yourOktaDomain} with your domain on Okta as shown in the video.
For providing redirectURI or callbackURI registered with the SSO provider, you can either select Configuration or Sample Script. Note that the redirect URI is already given in the helper text (as seen in the previous section).
Click Save to create and activate Okta SSO login.
Now your users will be able to log in to Devtron using the Okta authentication method. Note that existing signed-in users will be logged out and they have to log in again using their OIDC account.
Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
clientSecret
redirectURI (already provided in SSO Login Services by Devtron)


Devtron provides a sample configuration out of the box. There are some values that you need to either get from your SSO provider or give to your SSO provider.
clientID
clientSecret
redirectURI (provided in SSO Login Services by Devtron)