Secrets and configmaps both are used to store environment variables but there is one major difference between them: Configmap stores key-values in normal text format while secrets store them in base64 encrypted form. Devtron hides the data of secrets for the normal users and it is only visible to the users having edit permission.
Secret objects let you store and manage sensitive information, such as passwords, authentication tokens, and ssh keys. Embedding this information in secrets is safer and more flexible than putting it verbatim in a Pod definition or in a container image.
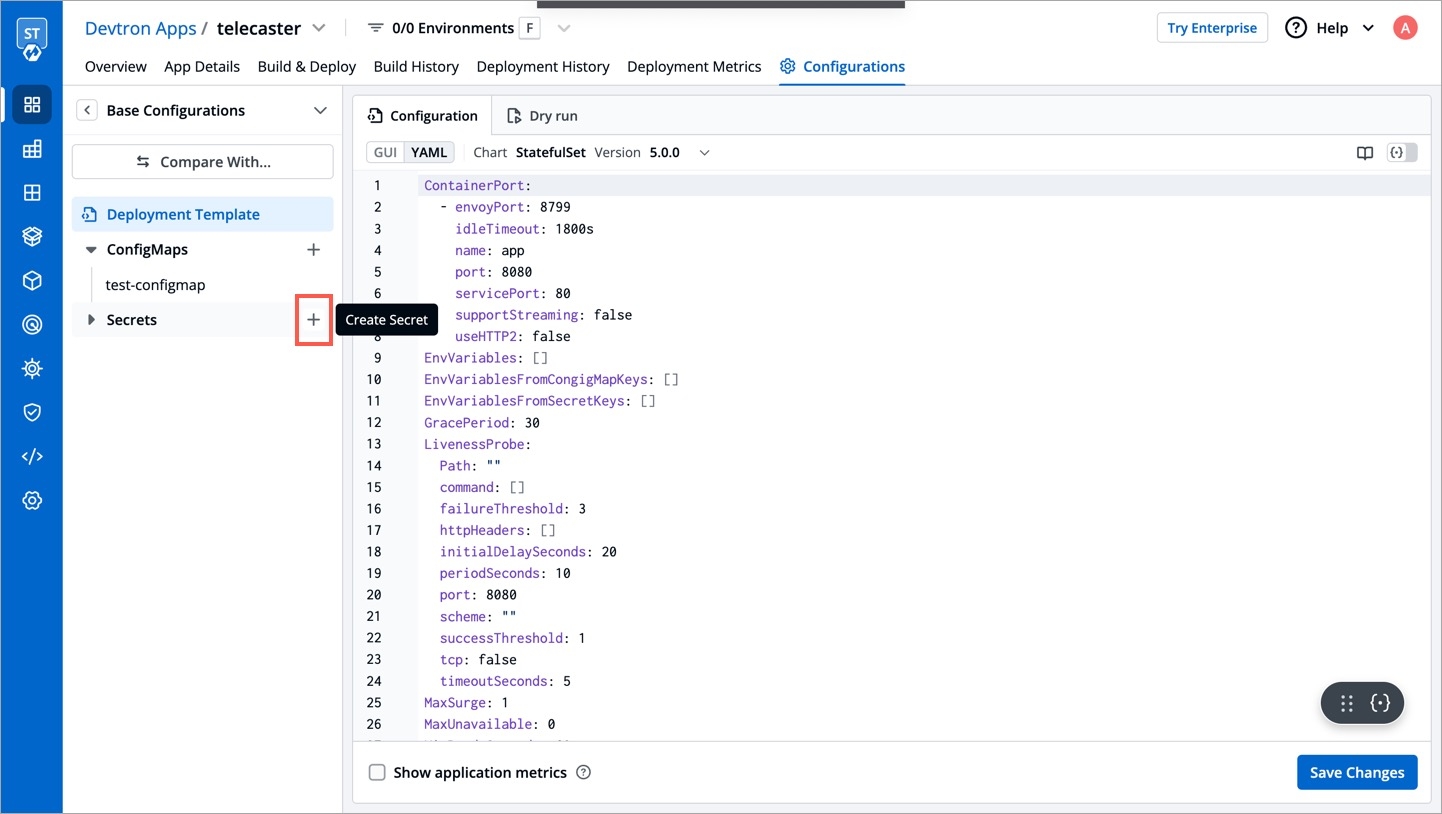
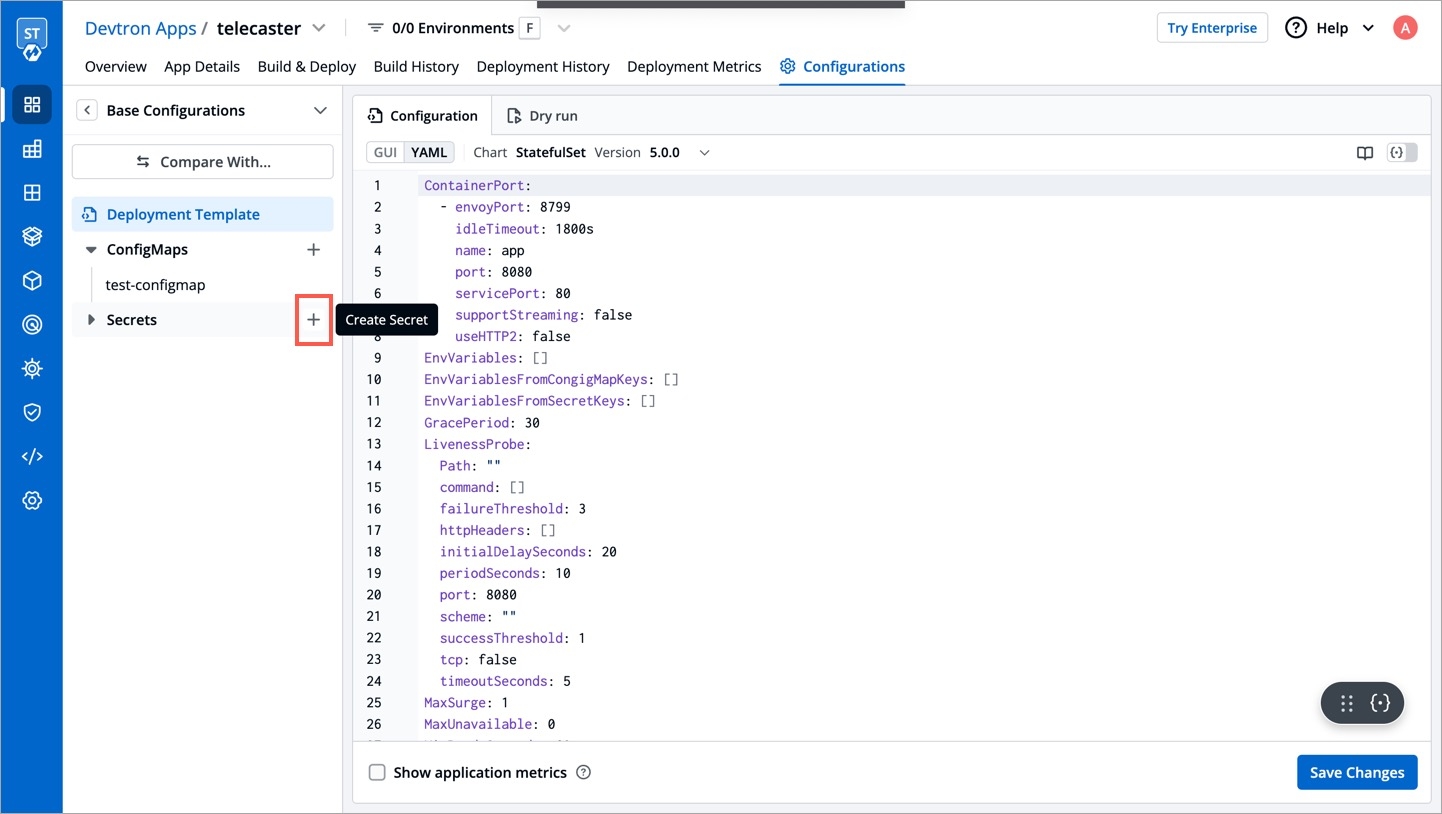
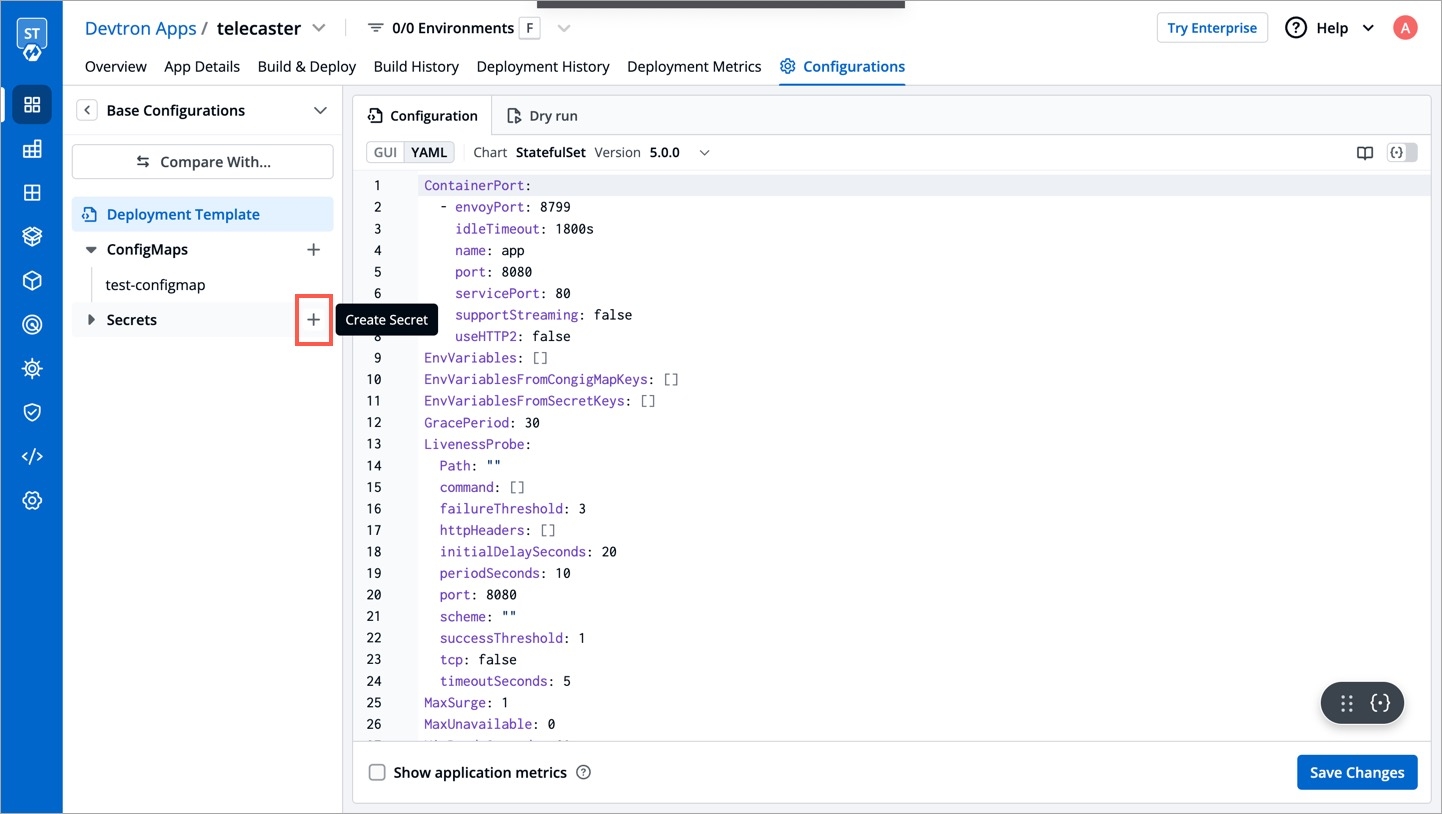
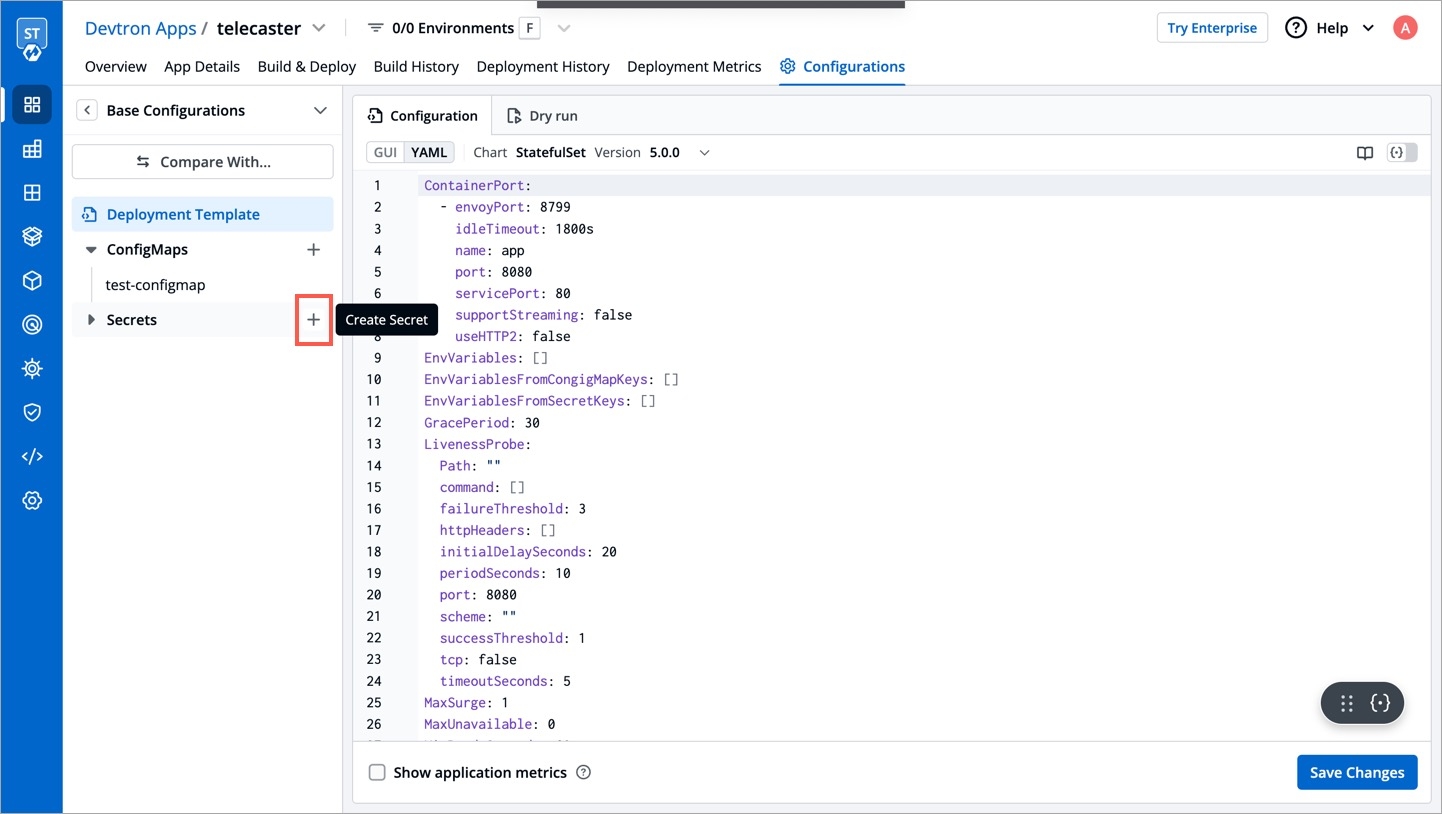
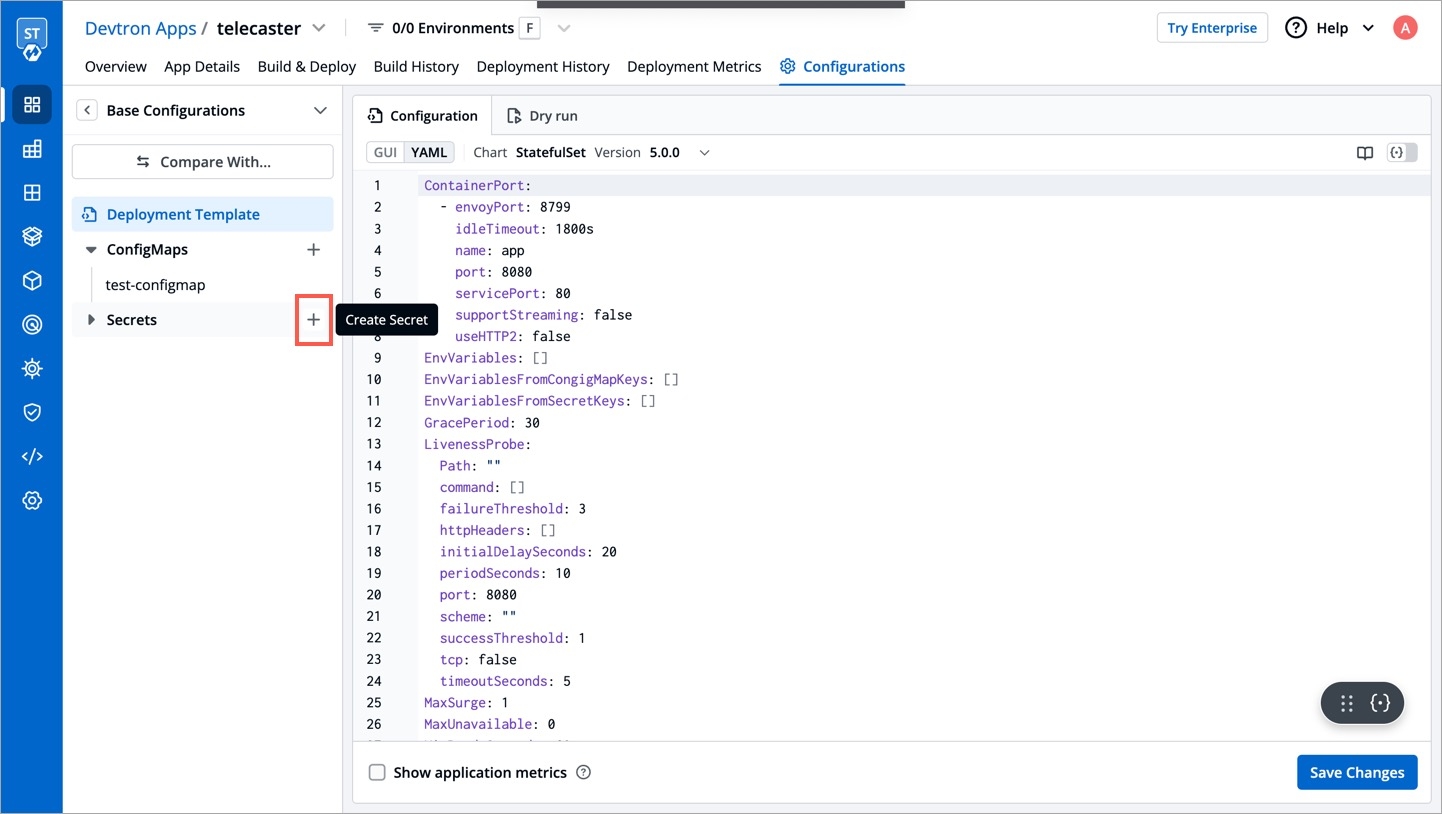
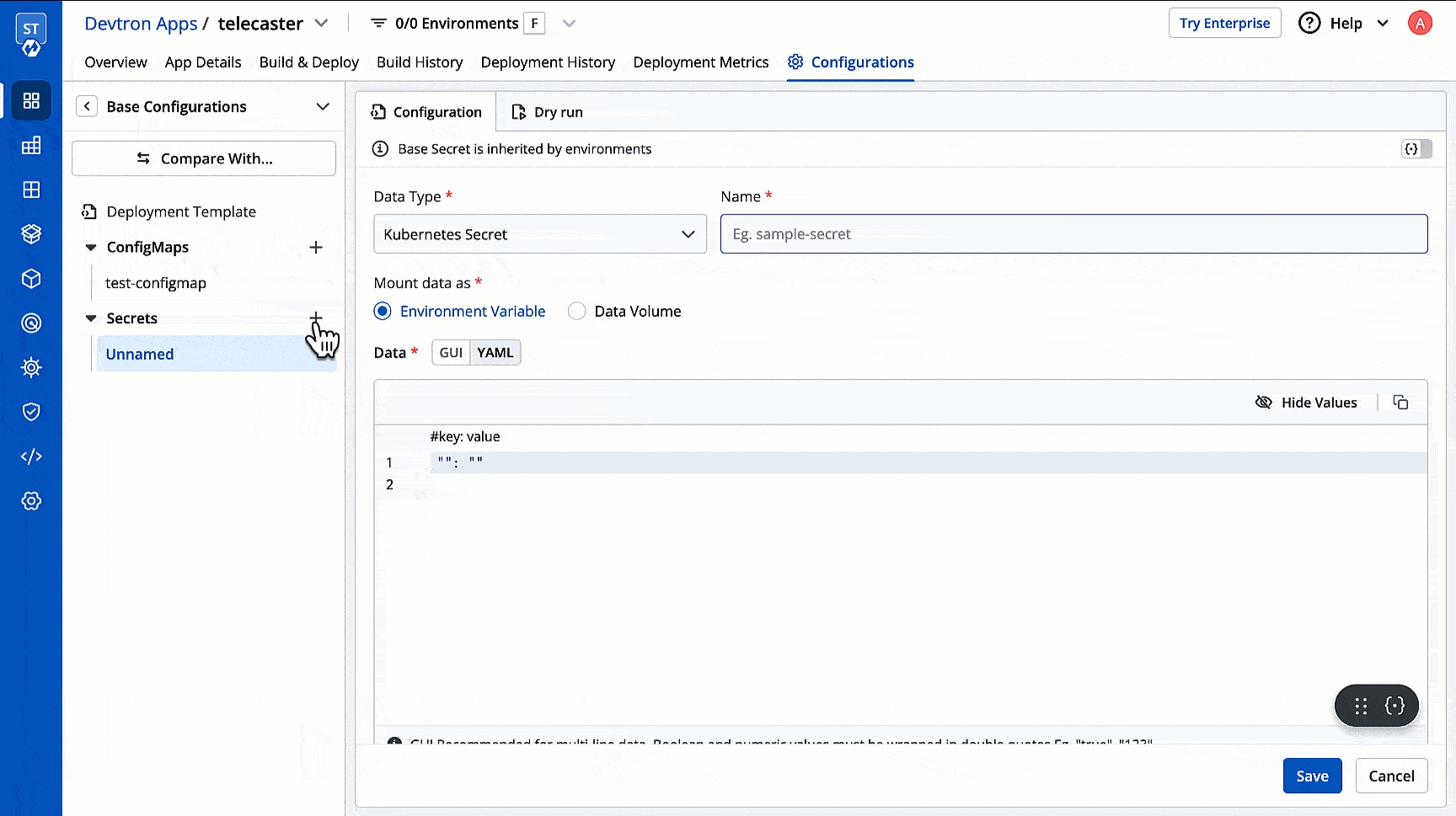
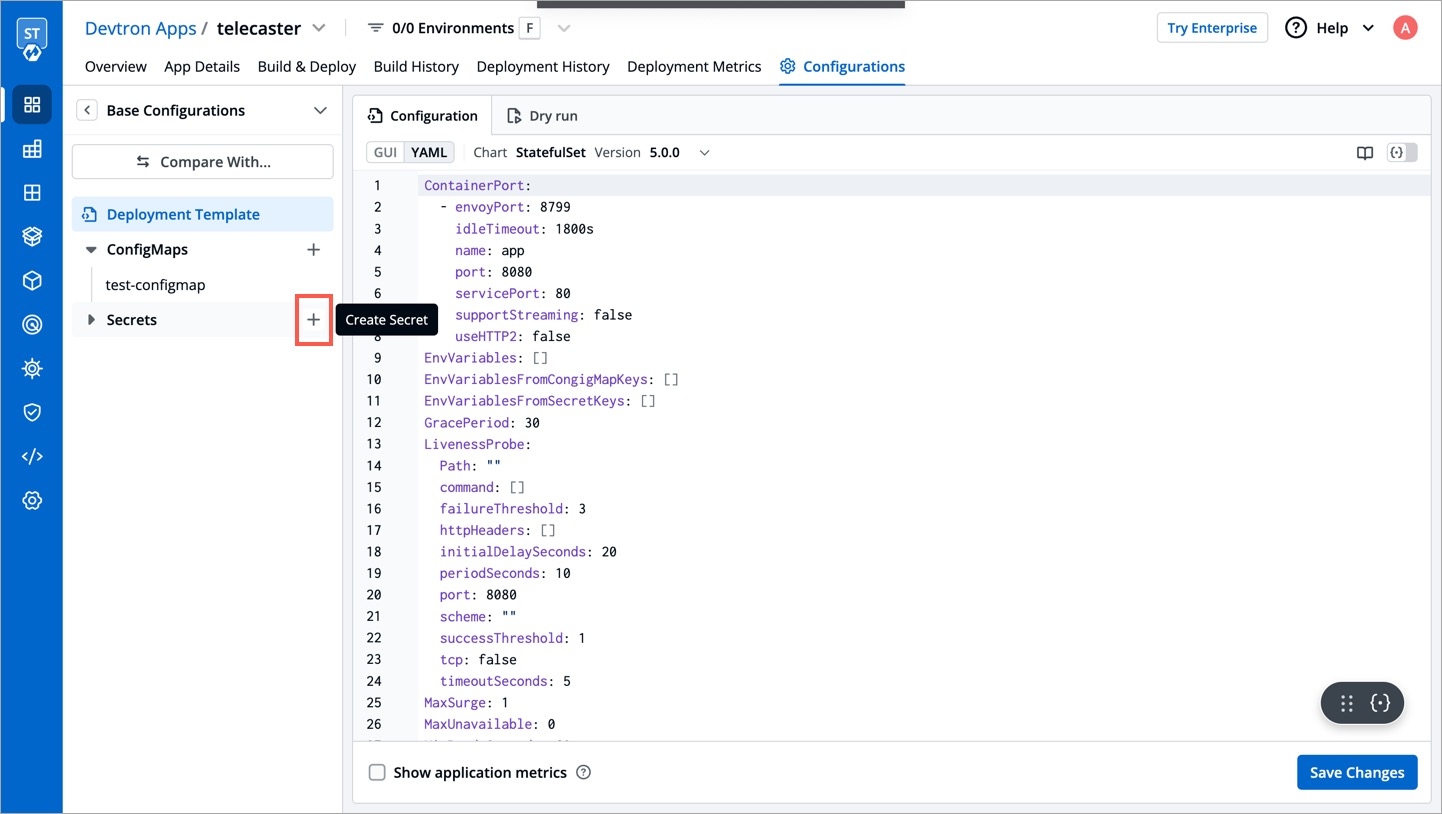
Click Add Secret to add a new secret.
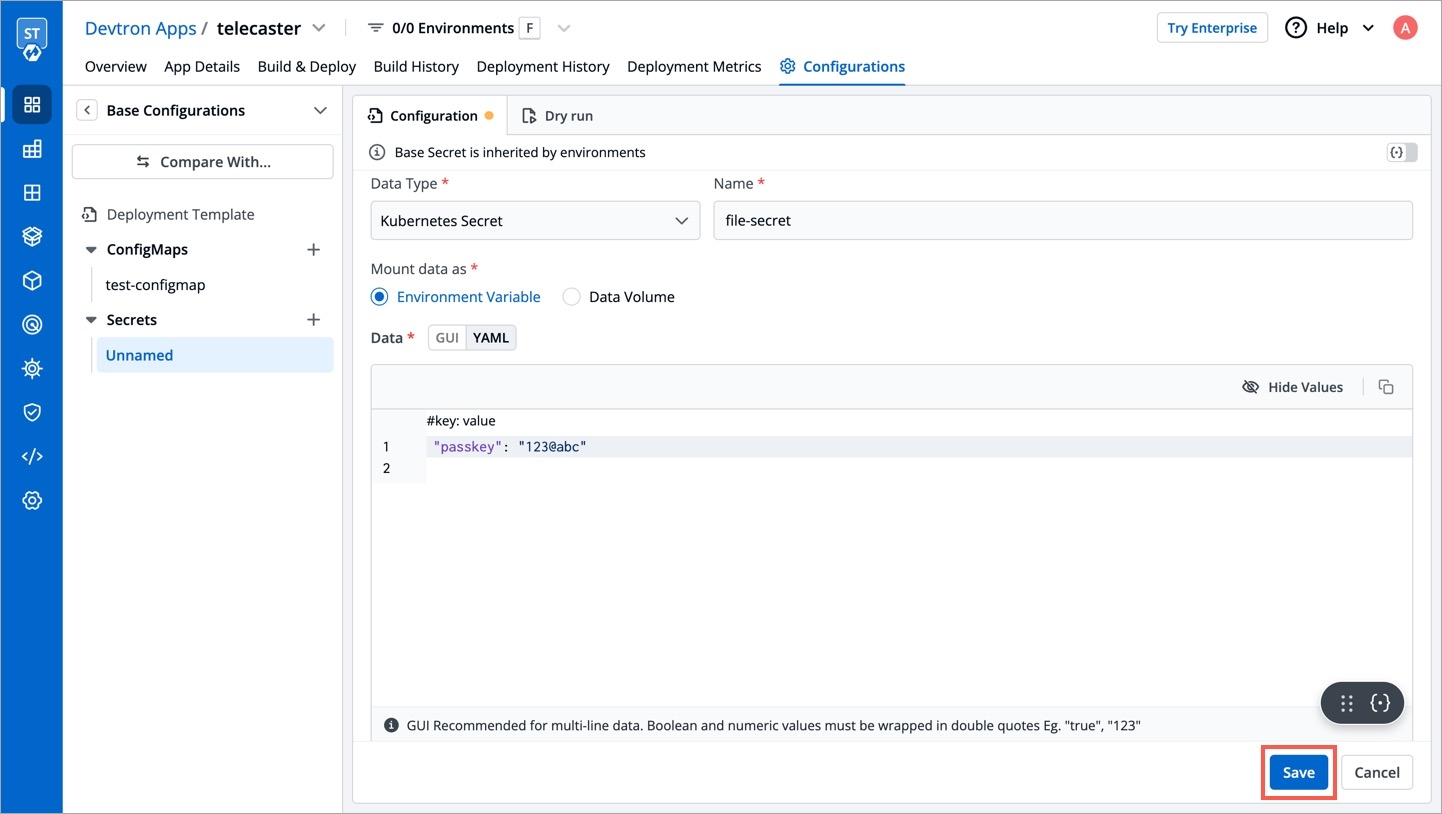
Name
Provide a name to your Secret
Data Type
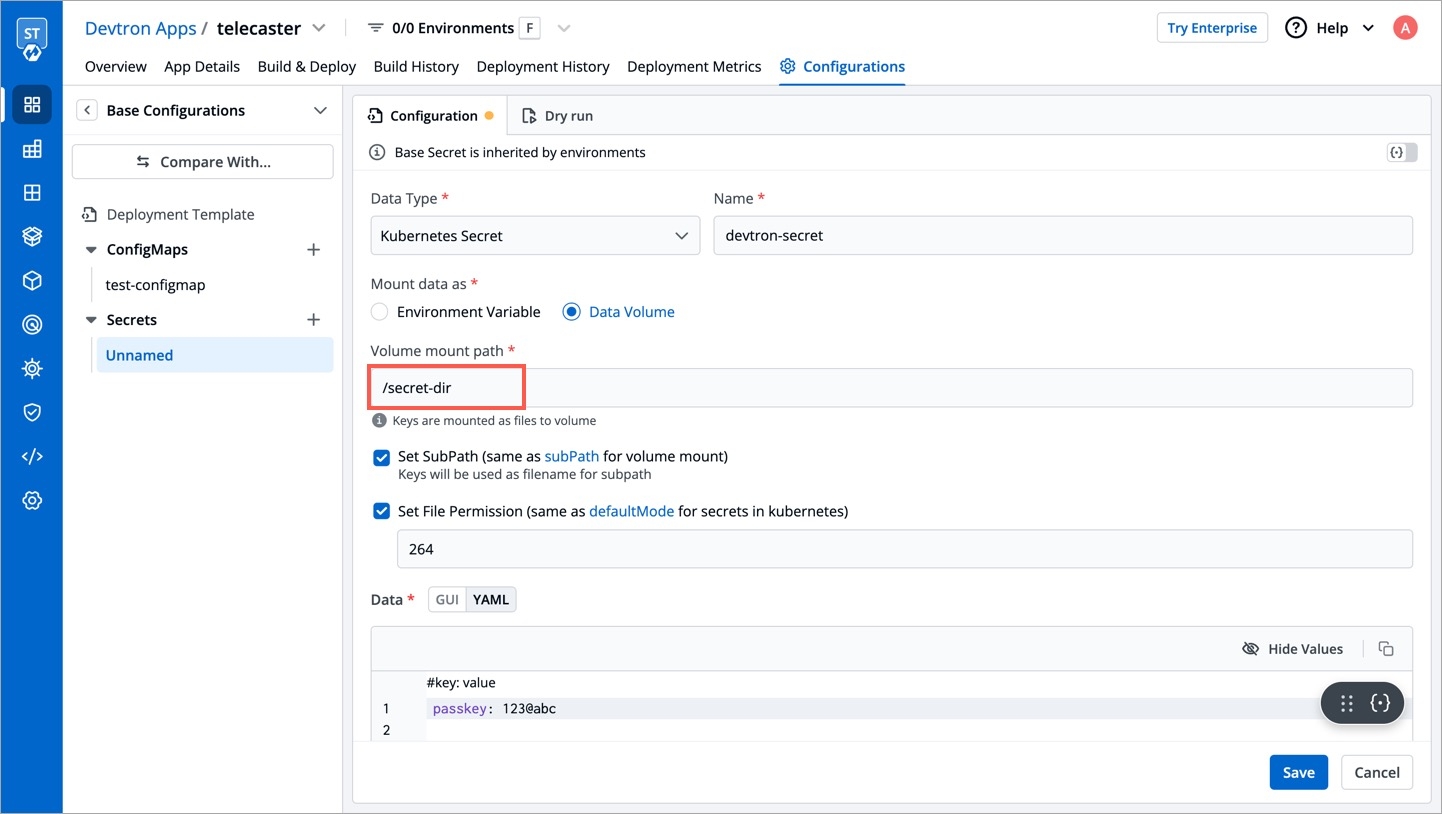
Data Volume
Specify if there is a need to add a volume that is accessible to the Containers running in a pod.
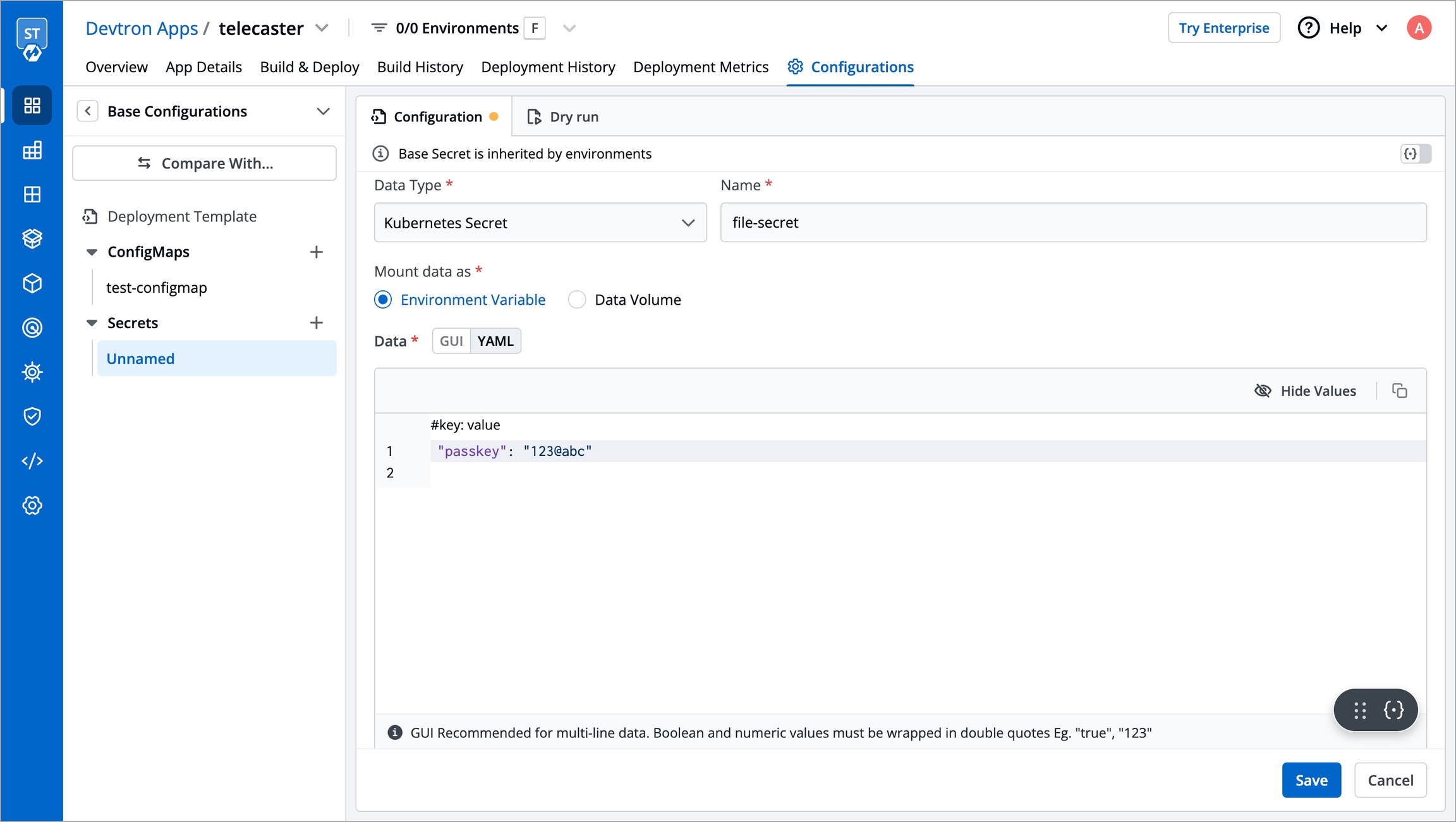
Use secrets as Environment Variable
Select this option if you want to inject Environment Variables in your pods using Secrets.
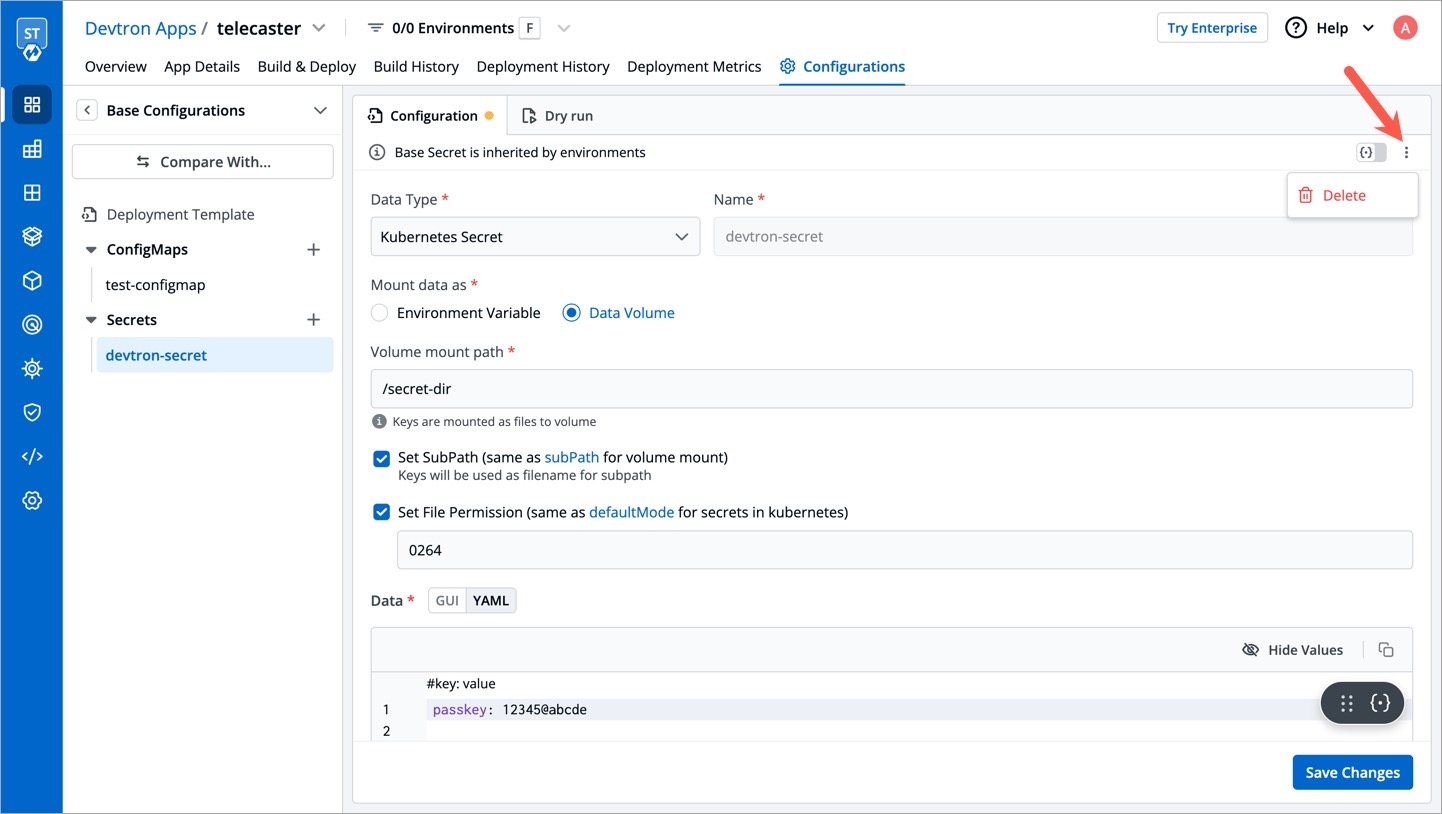
Use secrets as Data Volume
Select this option if you want to configure a Data Volume that is accessible to Containers running in a pod. Ensure that you provide a Volume mount path for the same.
Key-Value
Provide a key and the corresponding value of the provided key.
Specify the volume mount folder path in Volume Mount Path, a path where the data volume needs to be mounted. This volume will be accessible to the containers running in a pod.
For multiple files mount at the same location you need to check sub path bool field, it will use the file name (key) as sub path. Sub Path feature is not applicable in case of external configmap except AWS Secret Manager, AWS System Manager and Hashi Corp Vault, for these cases Name (Secret key) as sub path will be picked up automatically.
File permission will be provide at the configmap level not on the each key of the configmap. it will take 3 digit standard permission for the file.
Click Save Secret to save the secret.
You can see the Secret is added.
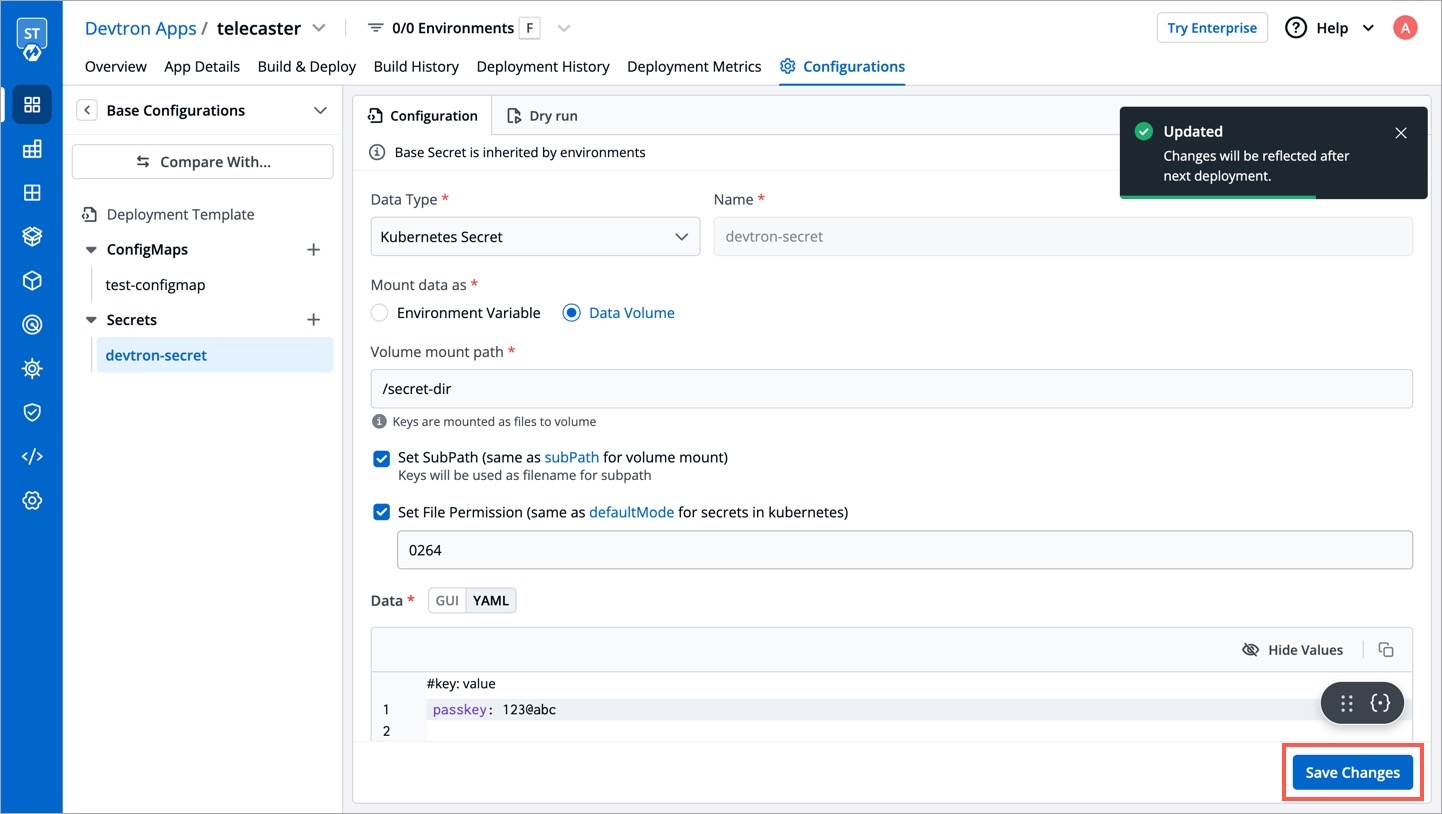
You can update your secrets anytime later, but you cannot change the name of your secrets. If you want to change your name of secrets then you have to create a new secret.
To update secrets, click the secret you wish to update.
Click Update Secret to update your secret.
You can delete your secret. Click your secret and click the delete sign to delete your secret.
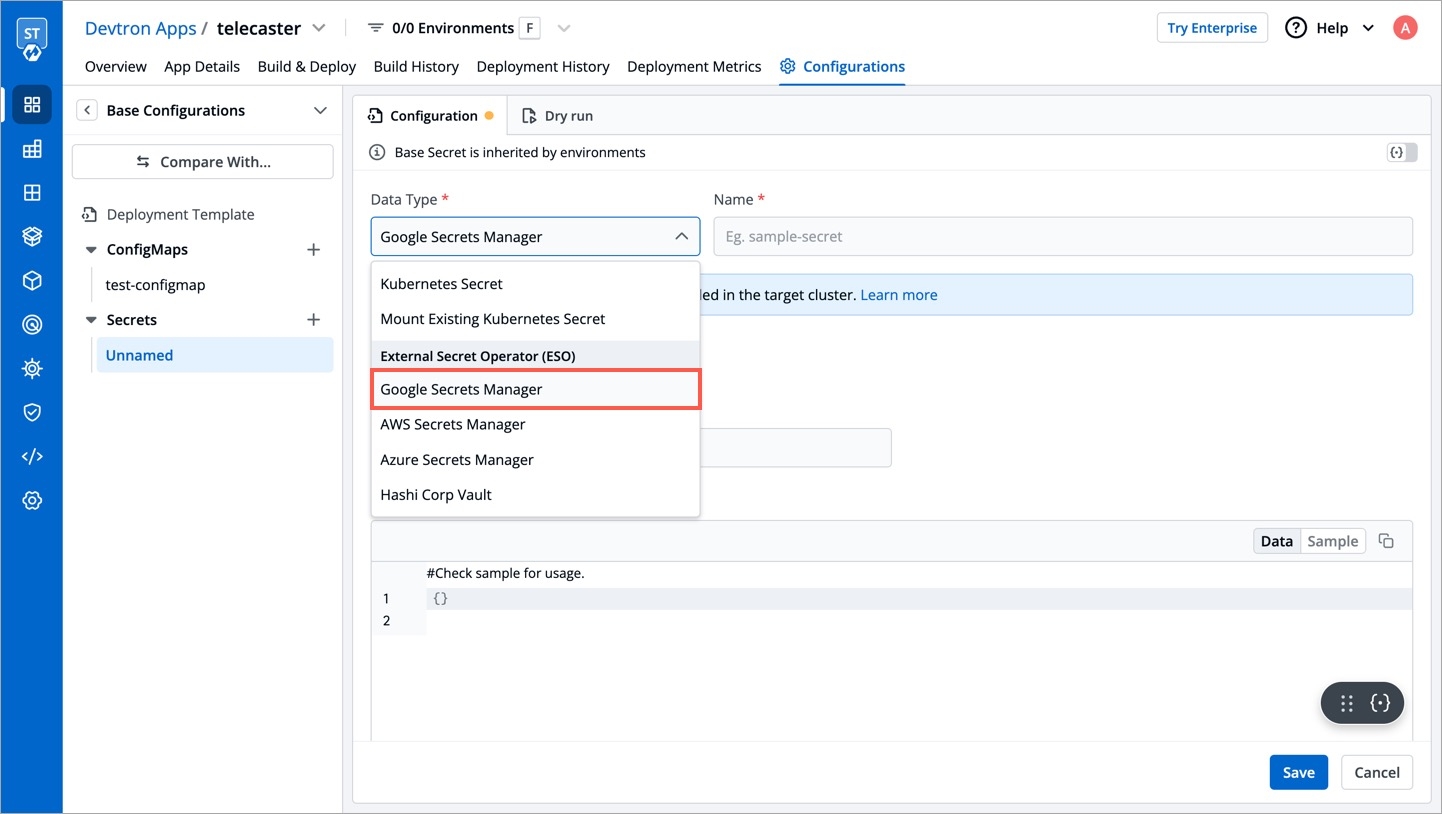
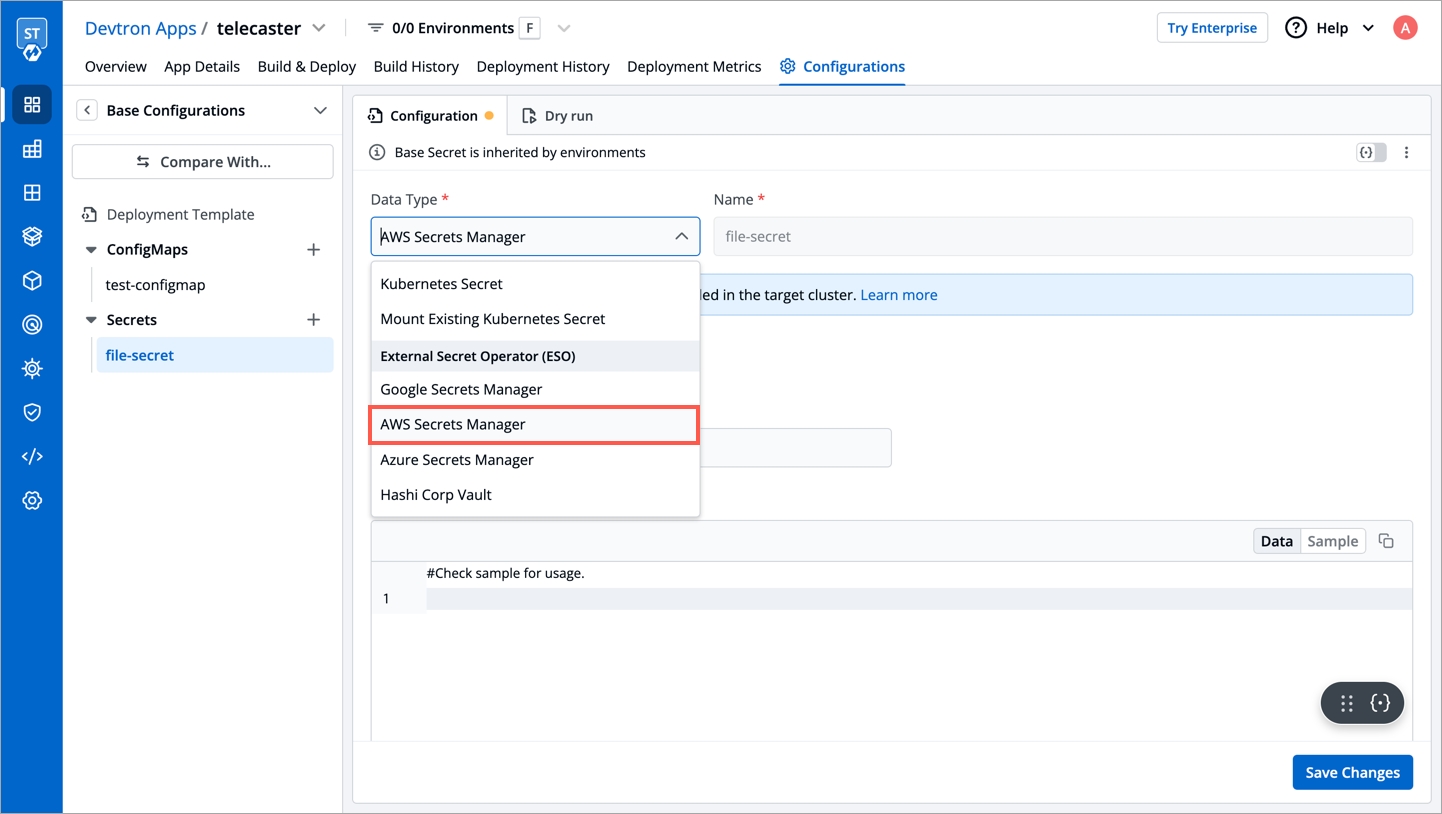
There are five Data types that you can use to save your secret.
Kubernetes Secret: The secret that you create using Devtron.
Kubernetes External Secret: The secret data of your application is fetched by Devtron externally. Then the Kubernetes External Secret is converted to Kubernetes Secret.
AWS Secret Manager: The secret data of your application is fetched from AWS Secret Manager and then converted to Kubernetes Secret from AWS Secret.
AWS System Manager: The secret data for your application is fetched from AWS System Secret Manager and all the secrets stored in AWS System Manager are converted to Kubernetes Secret.
HashiCorp Vault: The secret data for your application is fetched from HashiCorp Vault and the secrets stored in HashiCorp Vault are converted to Kubernetes Secret.
Note: The conversion of secrets from various data types to Kubernetes Secrets is done within Devtron and irrespective of the data type, after conversion, the Pods access secrets normally.
Use this option to mount an existing Kubernetes Secret in your application pods. A Secret will not be created by system so please ensure that the secret already exist within the namespace else the deployment will fail.
The secret that is already created and stored in the environment and being used by Devtron externally is referred here as Kubernetes External Secret. For this option, Devtron will not create any secret by itself but they can be used within the pods. Before adding secret from kubernetes external secret, please make sure that secret with the same name is present in the environment. To add secret from kubernetes external secret, follow the steps mentioned below:
Navigate to Secrets of the application.
Click Add Secret to add a new secret.
Select Kubernetes External Secret from dropdown of Data type.
Provide a name to your secret. Devtron will search secret in the environment with the same name that you mention here.
Before adding any external secrets on Devtron, kubernetes-external-secrets must be installed on the target cluster. Kubernetes External Secrets allows you to use external secret management systems (e.g., AWS Secrets Manager, Hashicorp Vault, etc) to securely add secrets in Kubernetes.
To install the chart with the release named my-release:
To install the chart with AWS IAM Roles for Service Accounts:
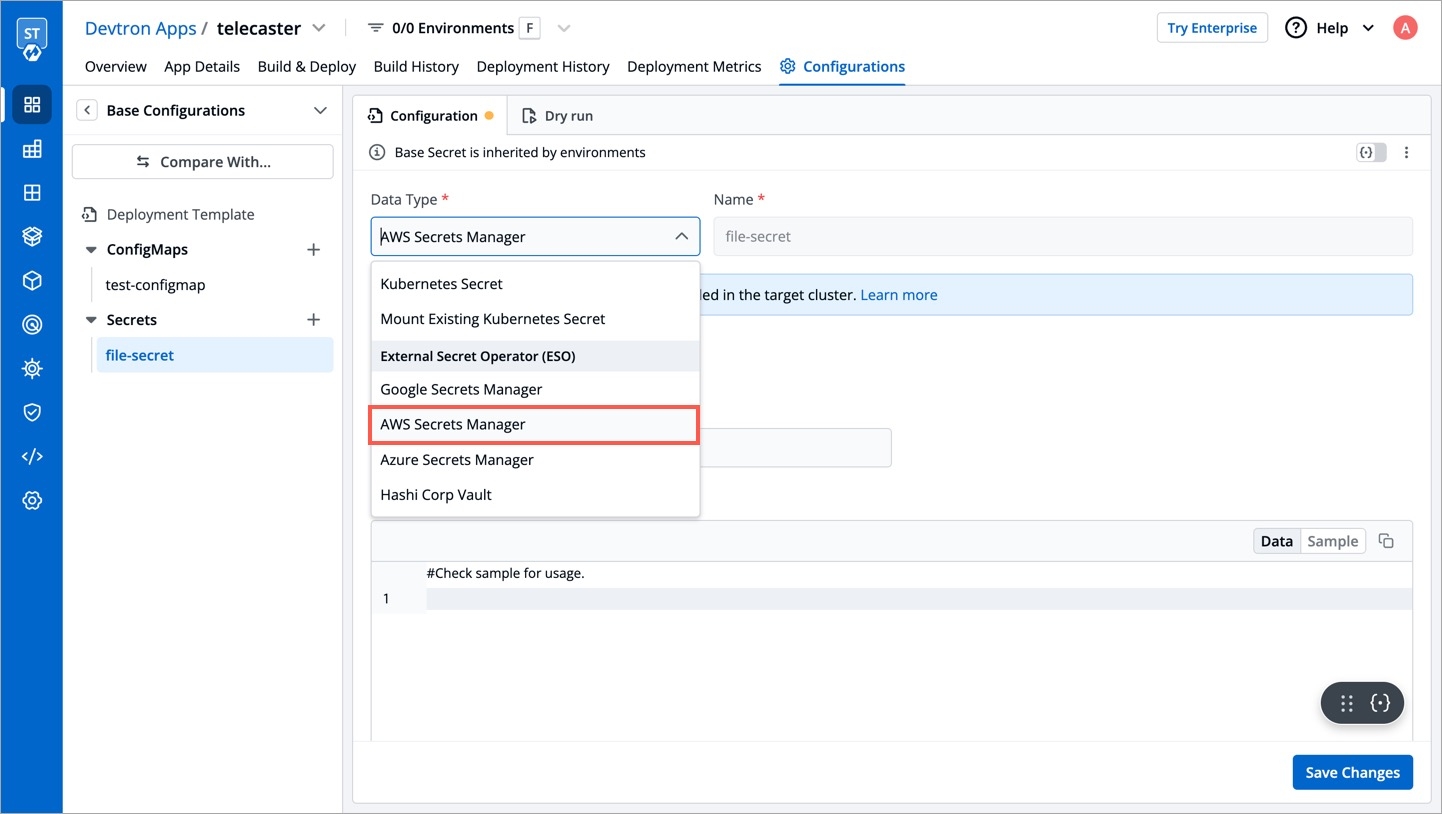
To add secrets from AWS secret manager, navigate to Secrets of the application and follow the steps mentioned below :
Click Add Secret to add a new secret.
Select AWS Secret Manager from dropdown of Data type.
Provide a name to your secret.
Select how you want to use the secret. You may leave it selected as environment variable and also you may leave Role ARN empty.
In Data section, you will have to provide data in key-value format.
All the required field to pass your data to fetch secrets on Devtron are described below :
key
Secret key in backend
name
Name for this key in the generated secret
property
Property to extract if secret in backend is a JSON object
isBinary
Set this to true if configuring an item for a binary file stored else set false
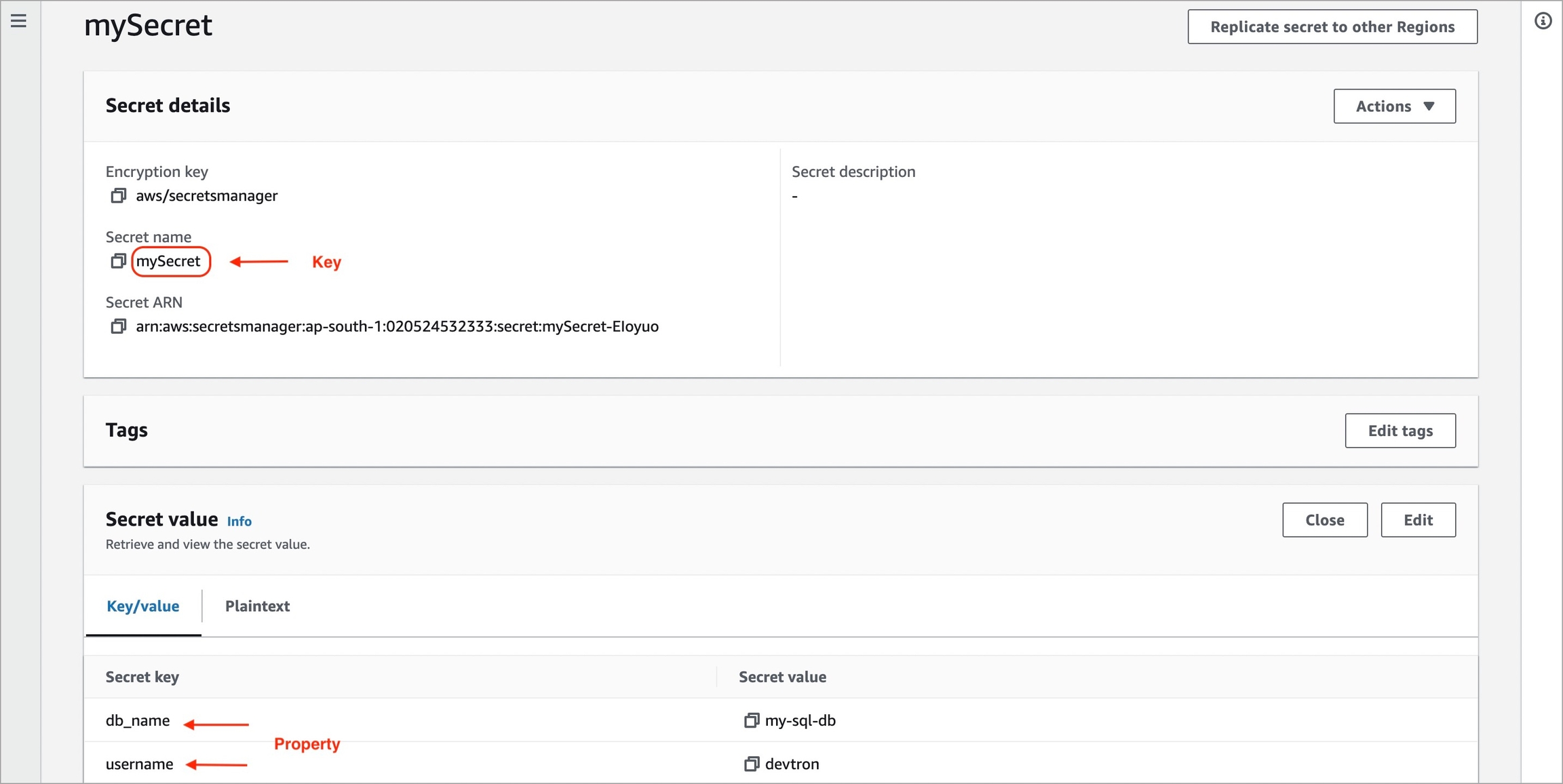
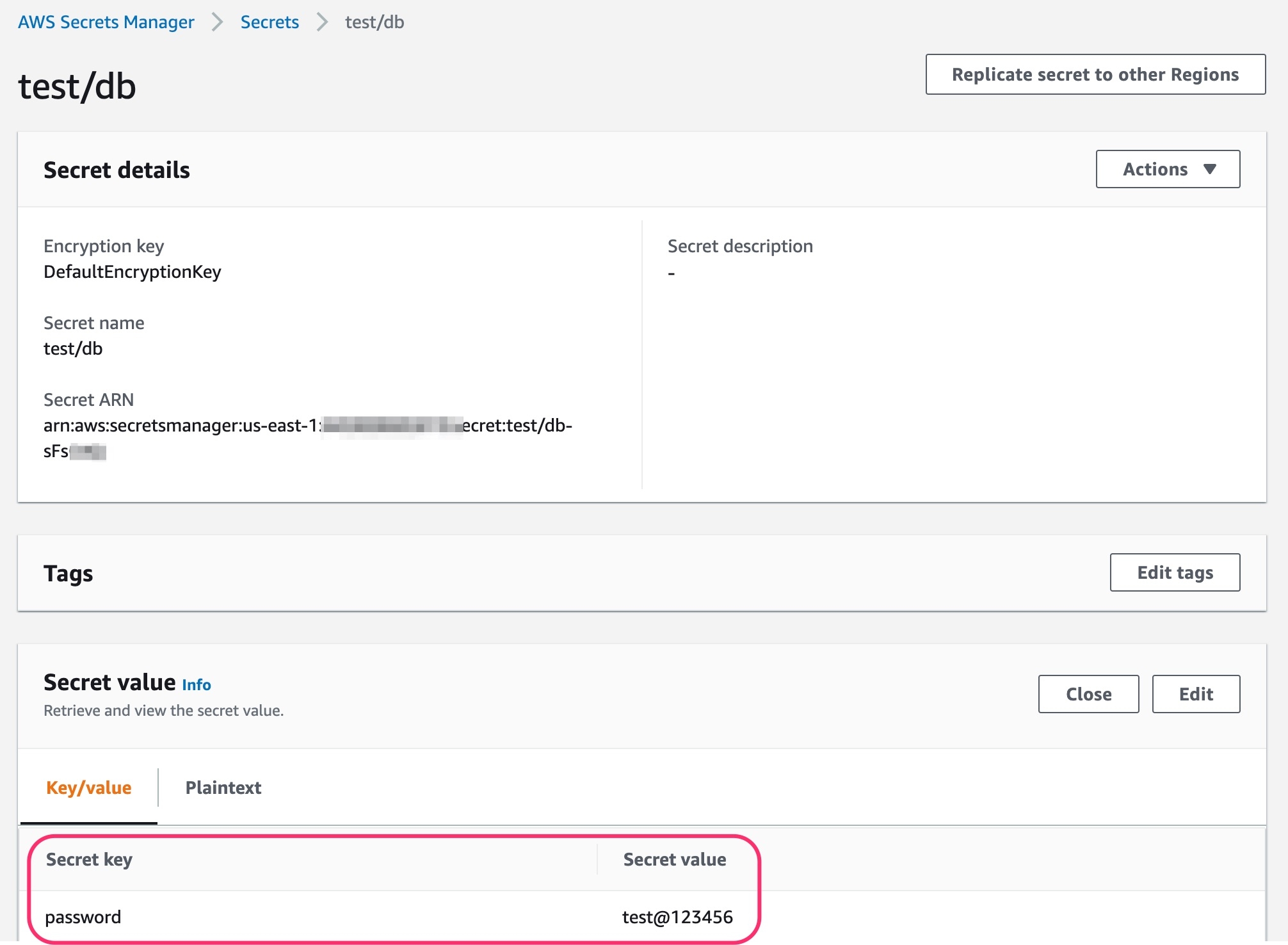
To add secrets in AWS secret manager, do the following steps :
Go to AWS secret manager console.
Click Store a new secret.
Add and save your secret.
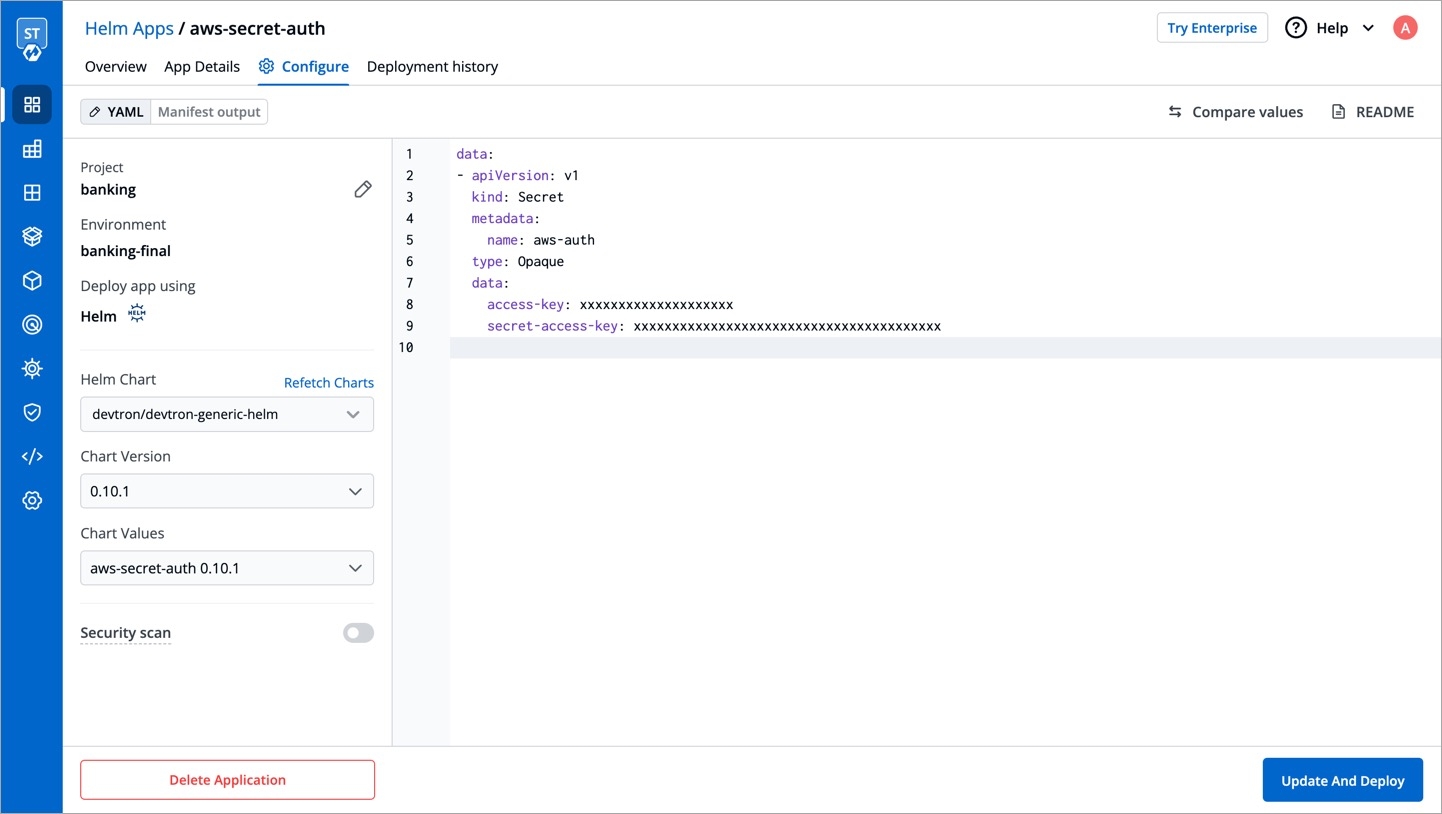
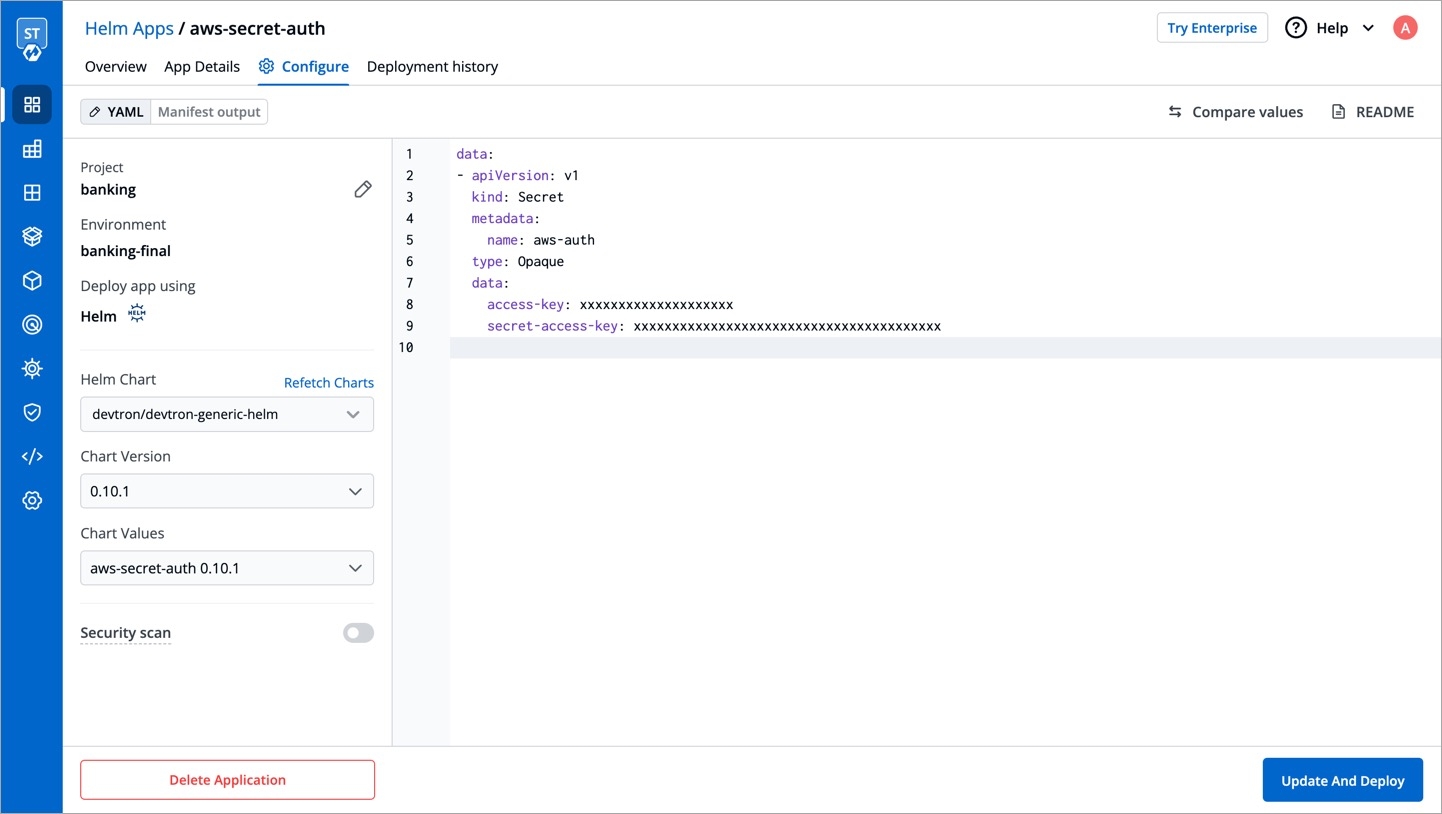
To add secrets from AWS Secrets Manager, we need to create a generic Kubernetes secret for AWS authentication.
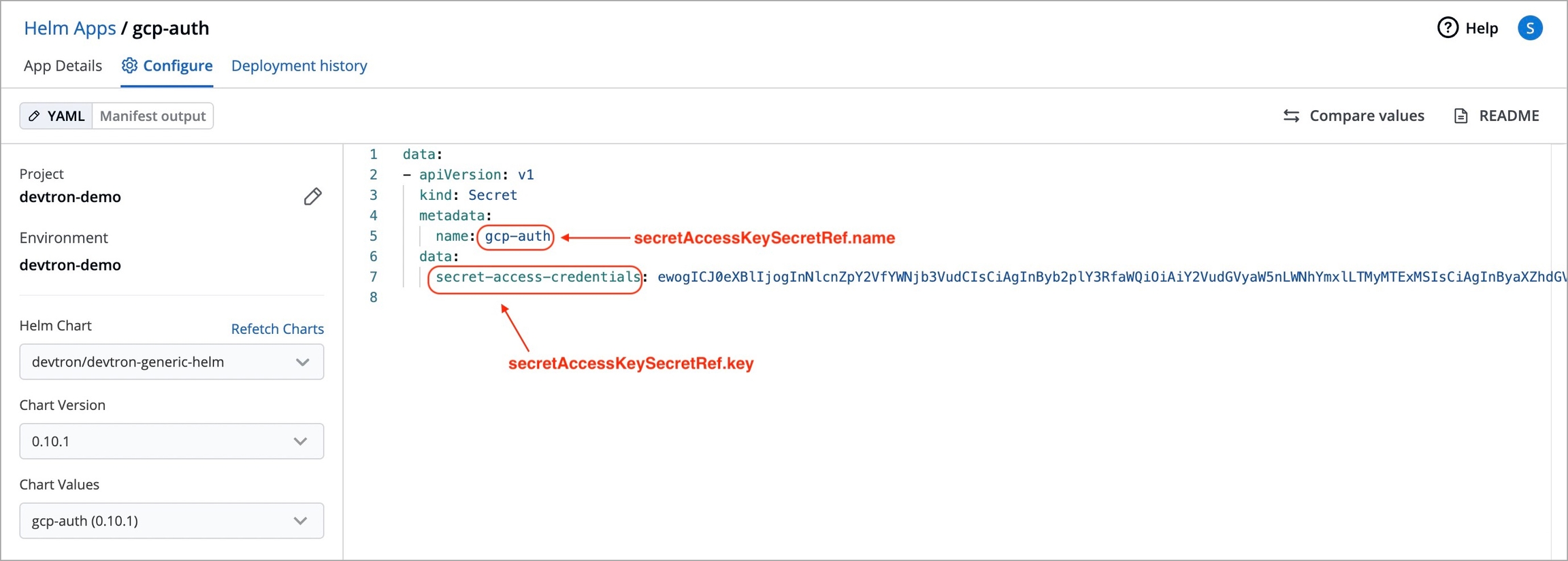
Create a Kubernetes secret in the namespace in which the application is to be deployed using base64 encoded AWS access-key and secret-access-key. You can use a Devtron generic chart for it.
Note: You don't have to create the Kubernetes secret every time you create external secret for the respective namespace.
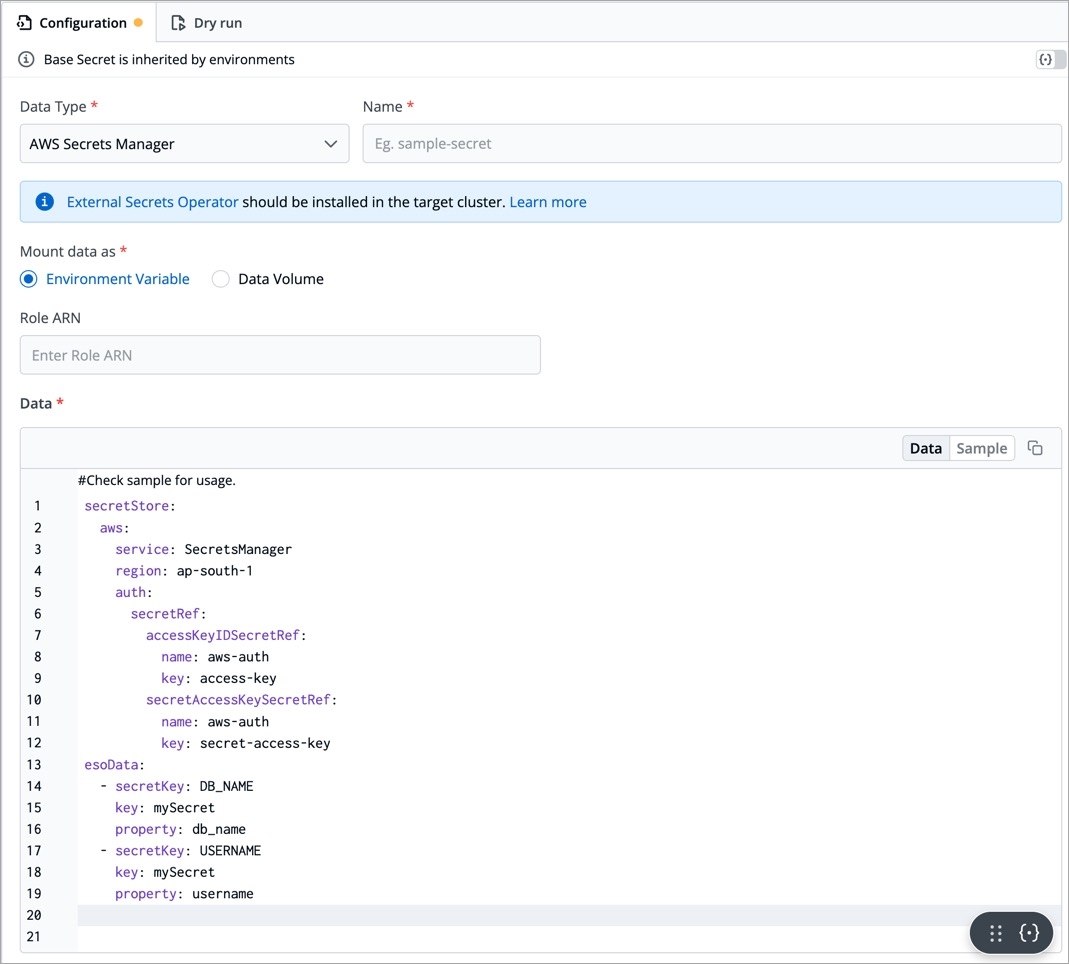
After creating the generic secret, navigate to Secrets section of the application and follow the steps mentioned below :
1. Click Add Secret to add a new secret
2. Select AWS Secret Manager under External Secret Operator (ESO) from the dropdown of Data type
3. Configure the secret
region
AWS region in which secret is created
accessKeyIDSecretRef.name
Name of secret created that would be used for authentication
accessKeyIDSecretRef.key
In generic secret created for AWS authentication, variable name in which base64 encoded AWS access-key is stored
secretAccessKeySecretRef.name
Name of secret created that would be used for authentication
secretAccessKeySecretRef.key
In generic secret created for AWS authentication, variable name in which base64 encoded secret-access-key is stored
secretKey
Key name to store secret
key
AWS Secrets Manager secret name
property
AWS Secrets Manager secret key
4. Save the secret
ClusterSecretStore provides a secure and centralized storage solution for managing and accessing sensitive information, such as passwords, API keys, certificates, and other credentials, within a cluster or application environment.
Requirement: Devtron deployment template chart version should be 4.17 and above.
To setup ESO AWS secrets manager with Devtron using ClusterSecretsStore, follow the mentined steps:
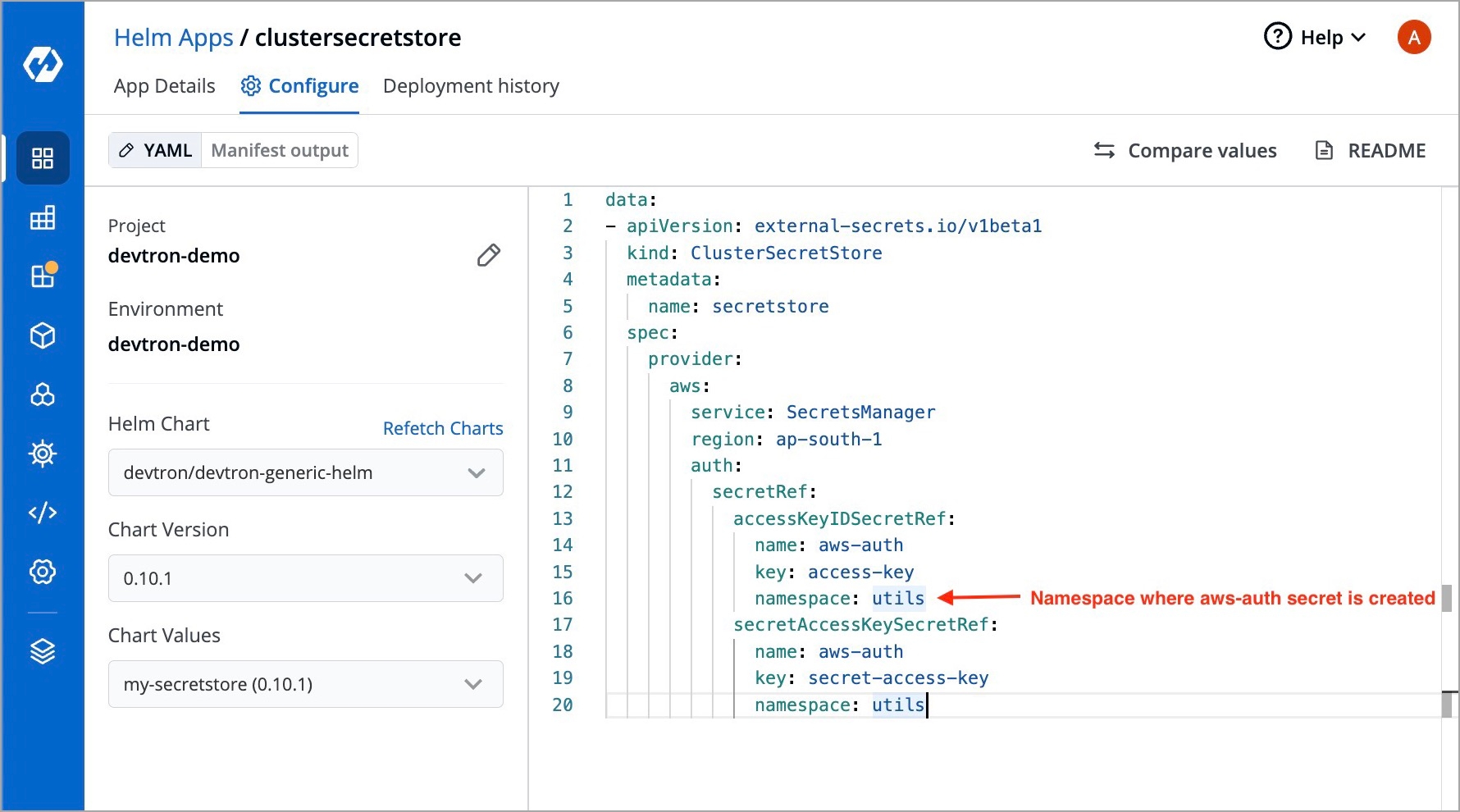
1. Create a secret for AWS authentication
Create a Kubernetes secret in any namespace using base64 encoded AWS access-key and secret-access-key. You can use the devtron generic chart for this.
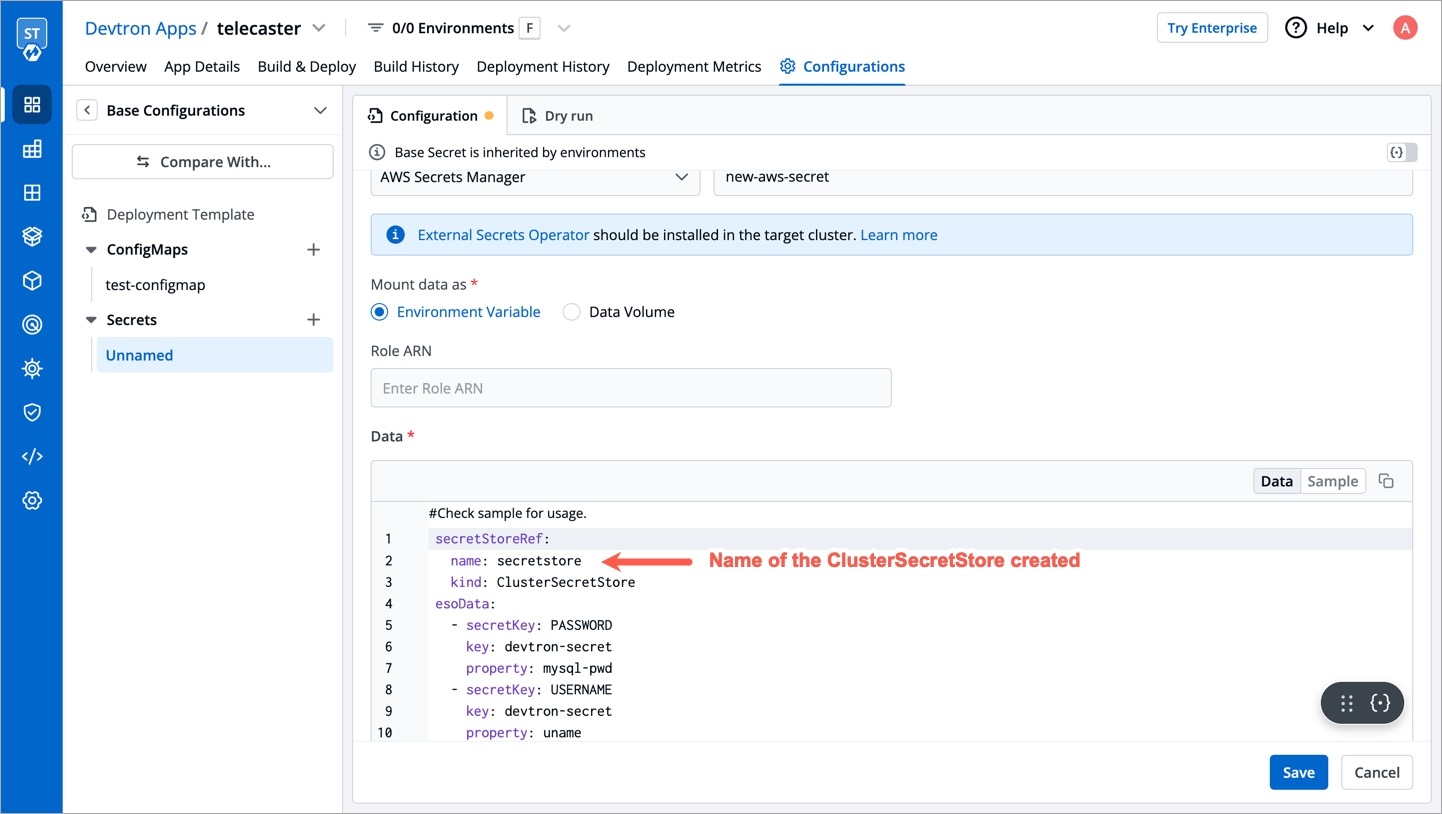
2. Create a ClusterSecretStore
Create a ClusterSecretStore using the secret created for AWS authentication in step 1.
3. Create a secret in the application using ESO AWS Secrets Manager
Go to the application where you want to create an external secret. Navigate to secrets section under application configuration and create a secret using ESO AWS Secrets Manager.
Provide the Data Type of your secret. To know about different Data Types available click on
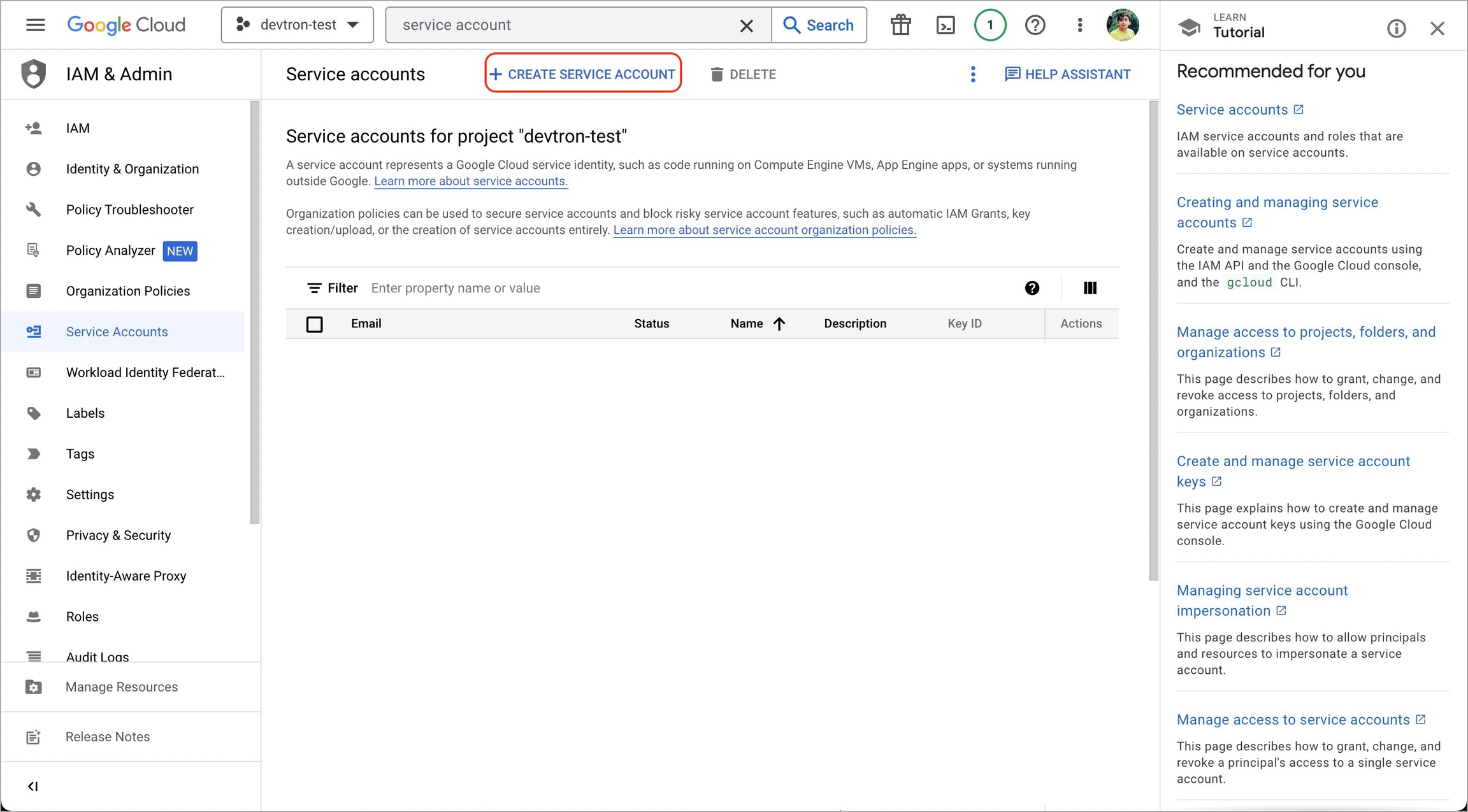
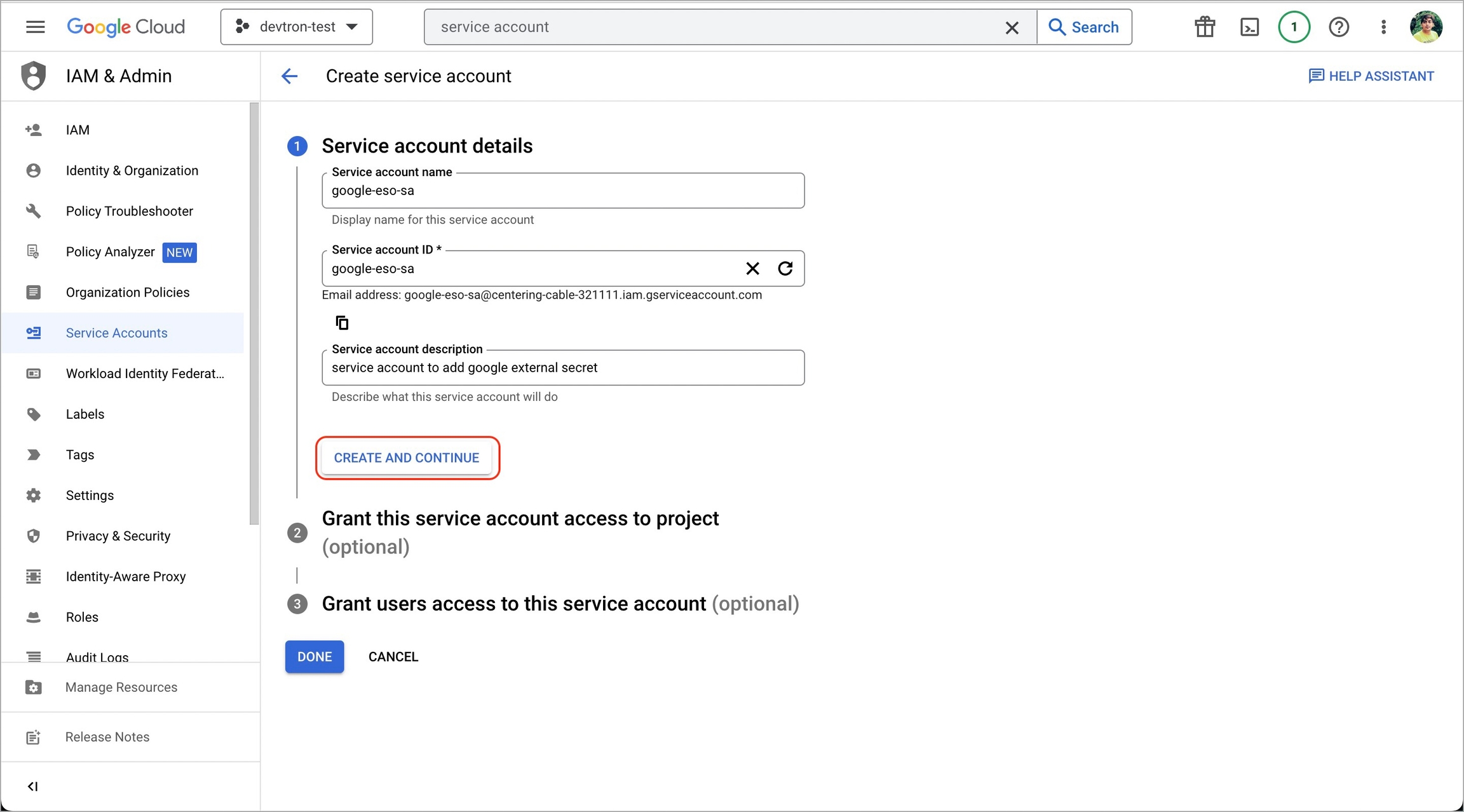
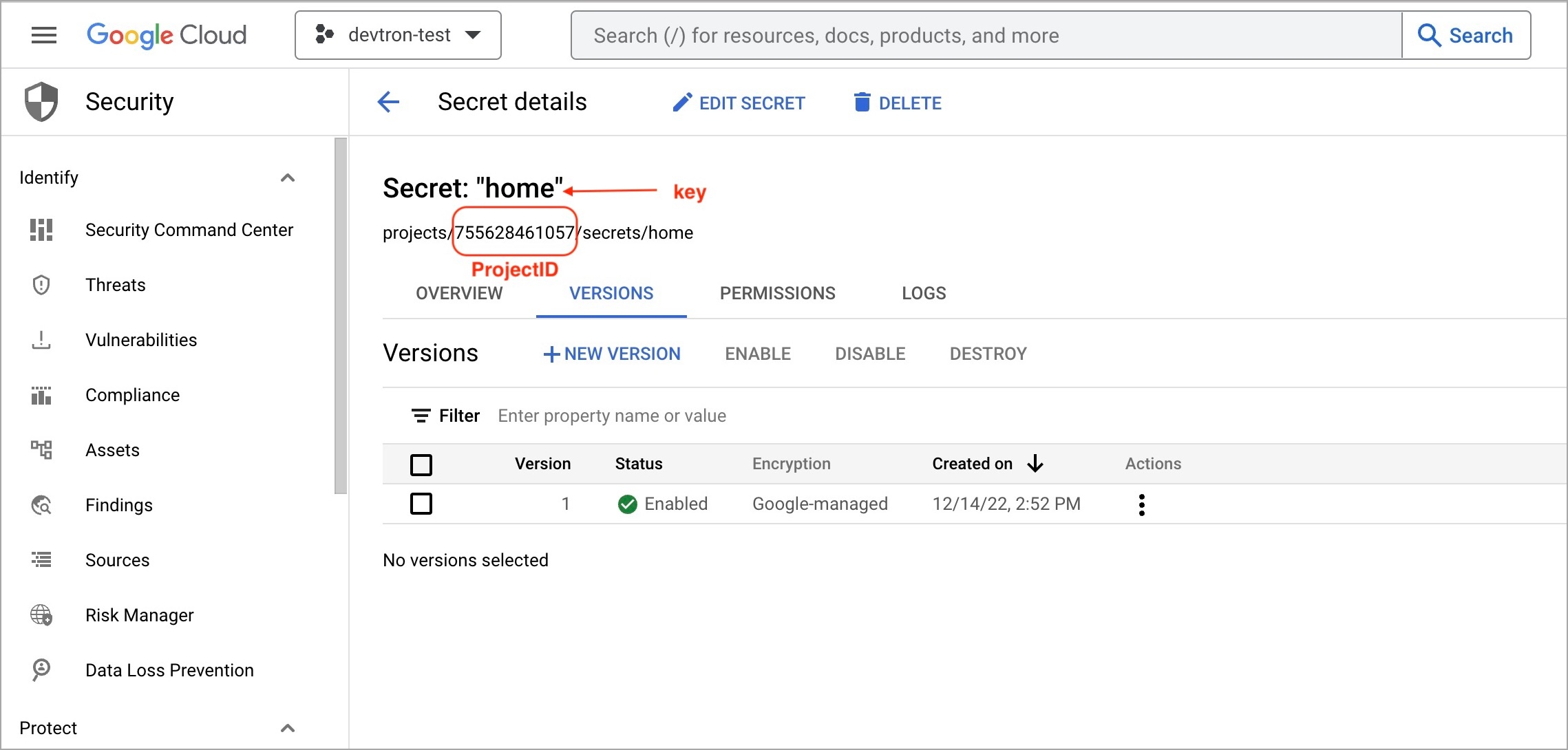
To add secrets from Google Secrets Manager, follow the steps mentioned below :
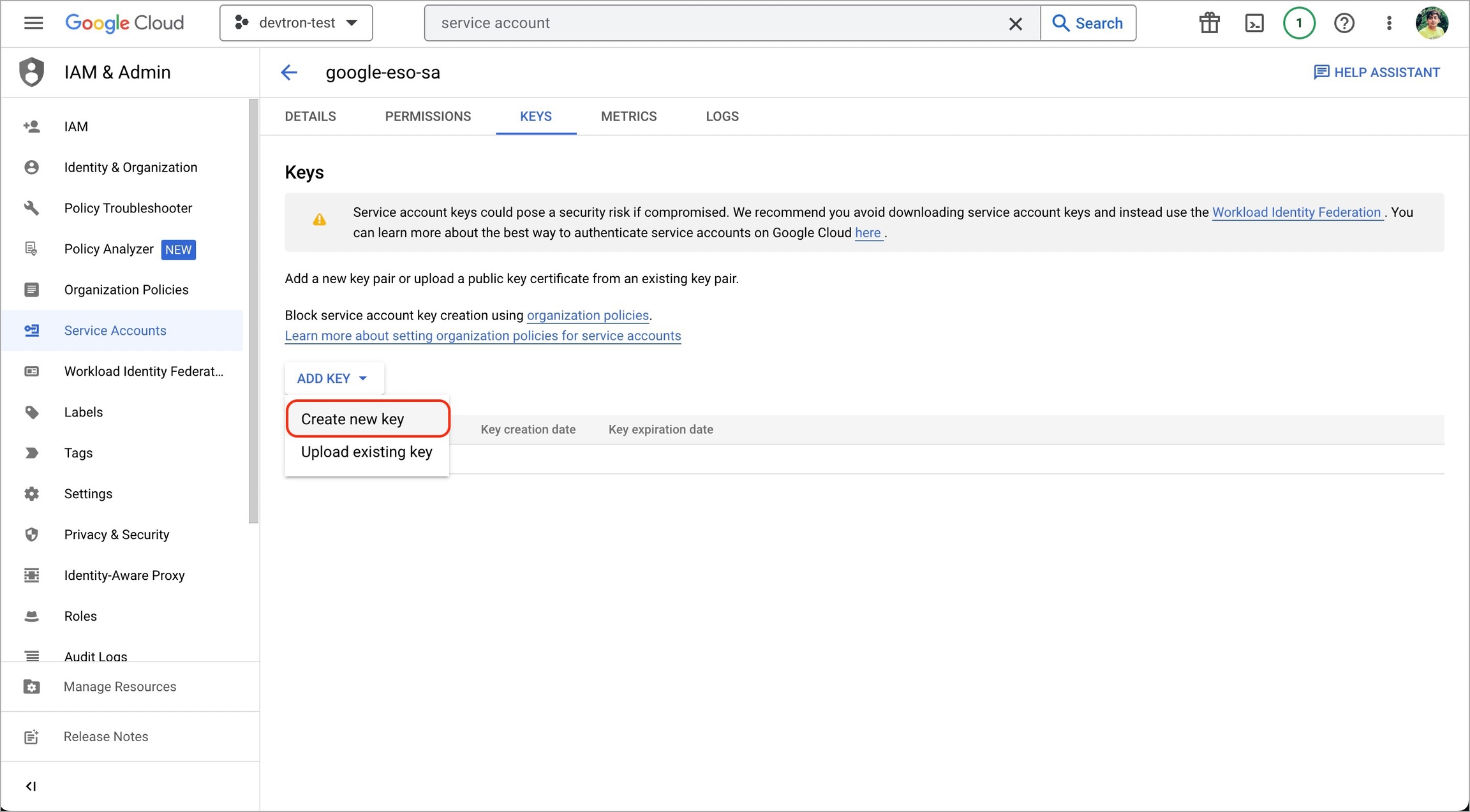
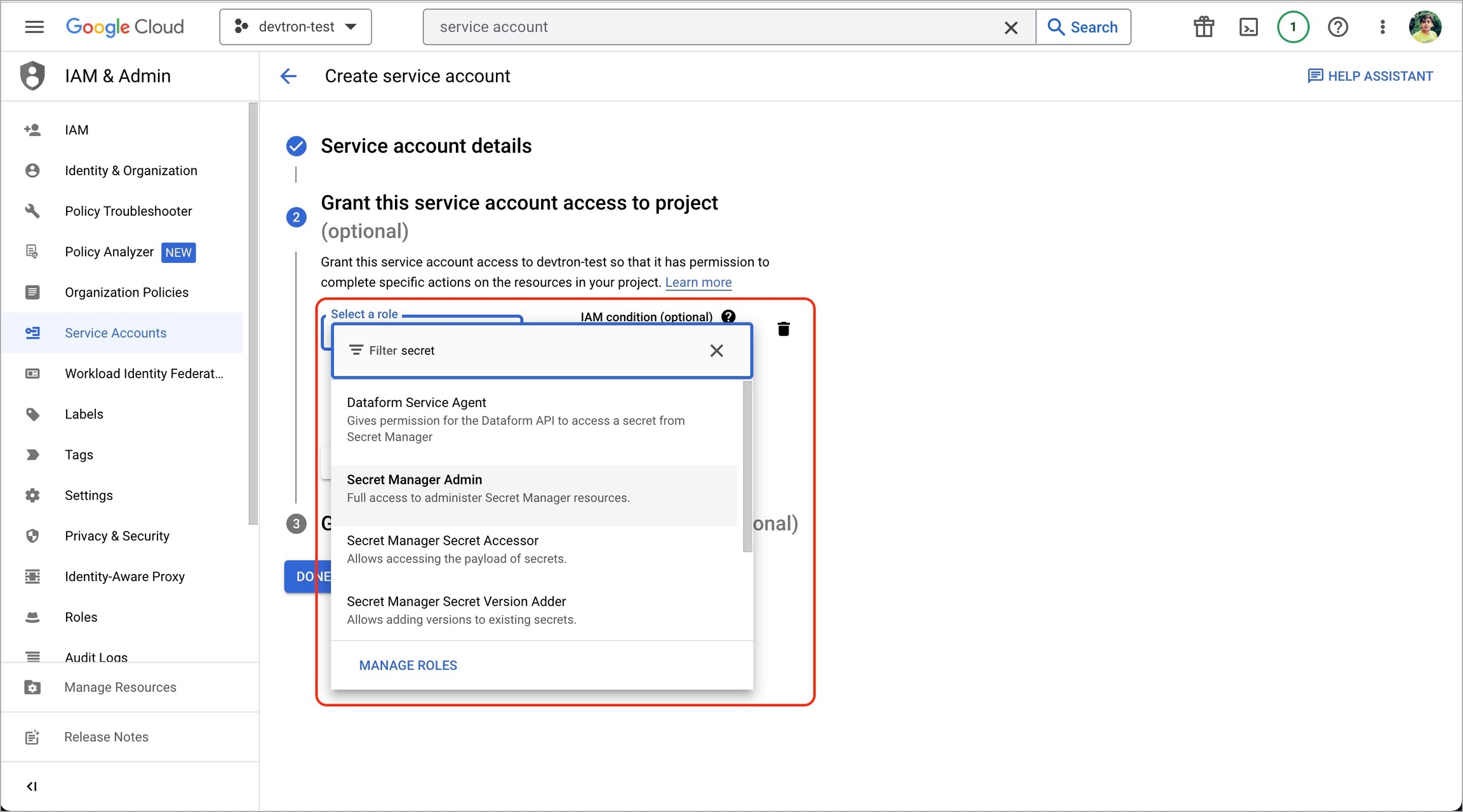
1. Go to Google cloud console and create a Service Account.
2. Assign roles to the service account.
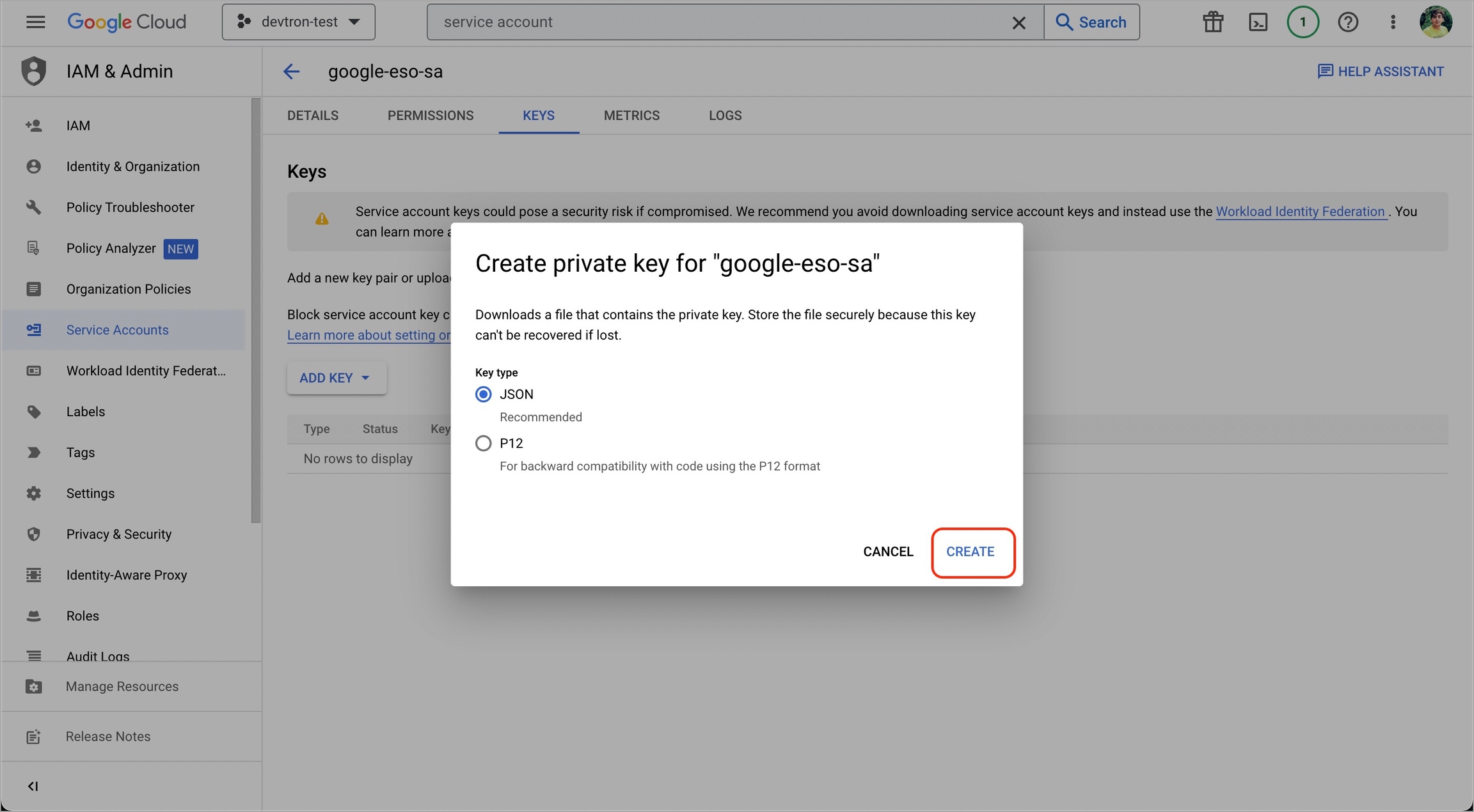
3. Add and create a new key.
5. Create a Kubernetes secret in the namespace in which the application is to be deployed using base64 encoded service account key.
You can use devtron generic chart for this.
6. After creating the generic secret, navigate to Secrets section of the application and click Add Secret to add a new secret.
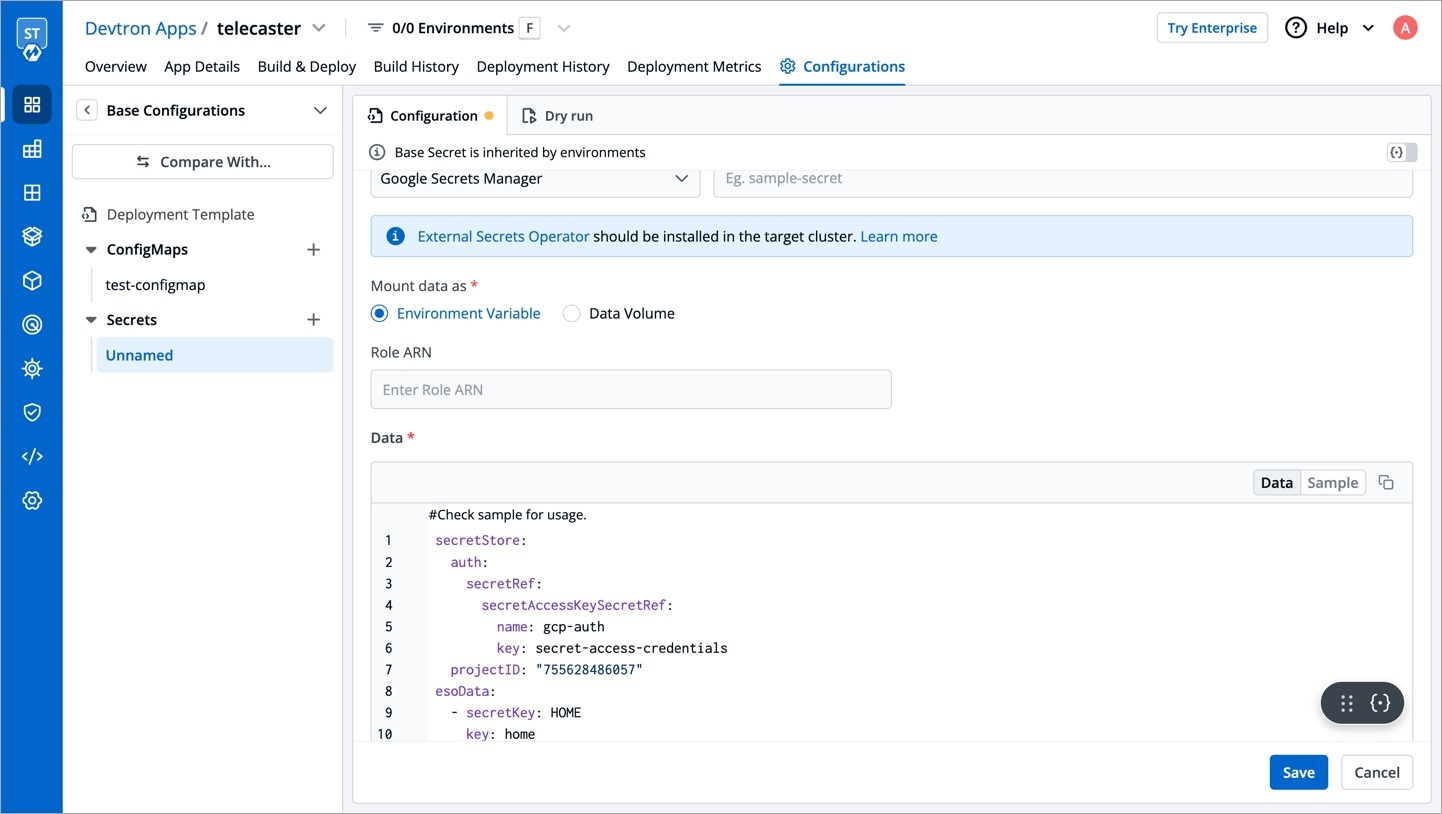
7. Select Google Secrets Manager under External Secret Operator (ESO) from the dropdown of Data type.
8. Configure secret:
secretAccessKeySecretRef.name
Name of secret created that would be used for authentication.
secretAccessKeySecretRef.key
In generic secret created for GCP authentication, variable name in which base64 encoded service account key is stored.
ProjectID
GCP Project ID where secret is created.
secretKey
Key name to store secret.
key
GCP Secrets Manager secret name.
9. Save secret.
Prerequisites: Chart version should be > 4.14.0
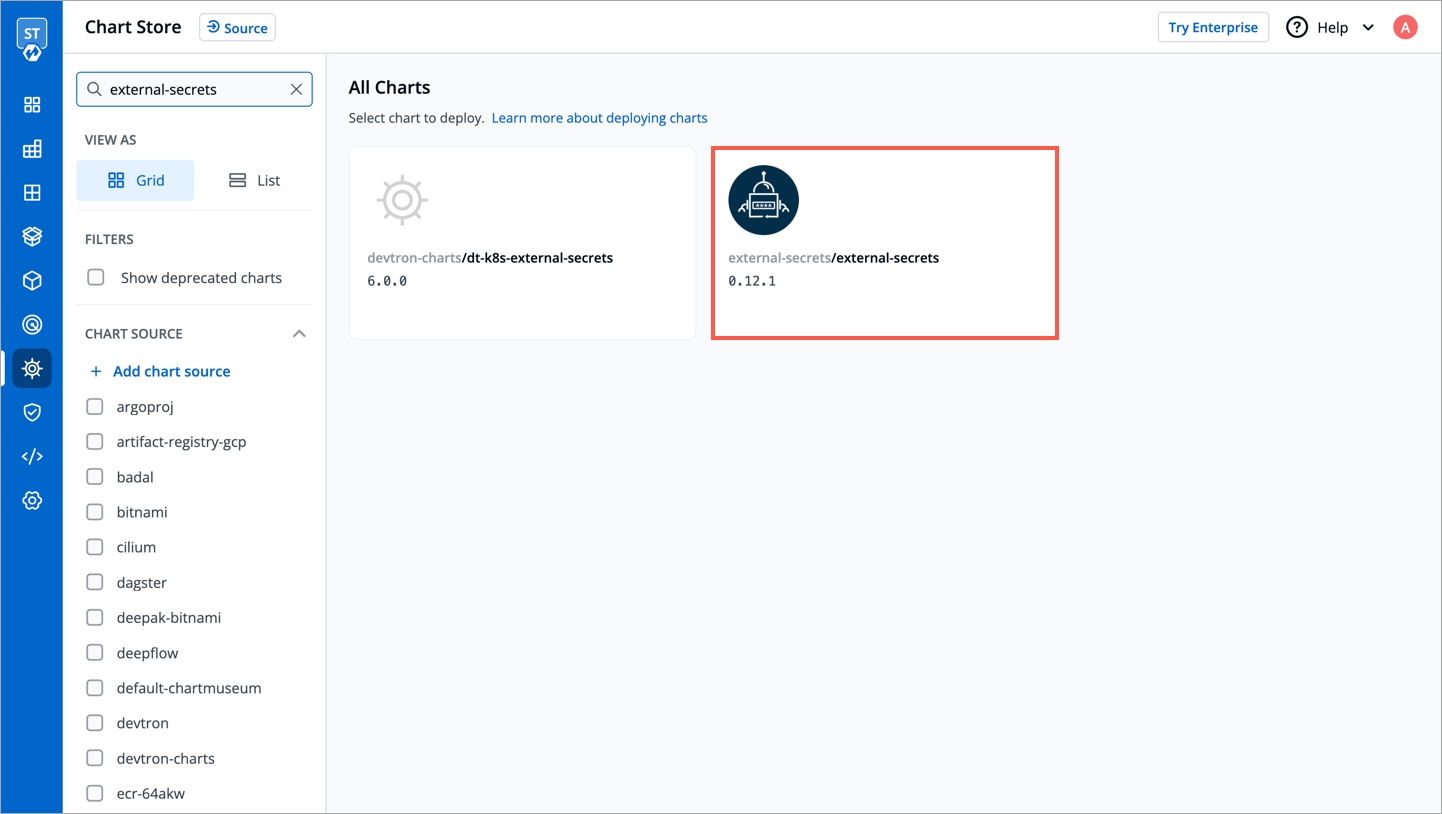
External Secrets Operator is a Kubernetes operator that integrates external secret management systems like AWS Secrets Manager, HashiCorp Vault, Google Secrets Manager, Azure Key Vault and many more. The operator reads information from external APIs and automatically injects the values into a Kubernetes Secret.
Before creating any external secrets on Devtron, External Secret Operator must be installed on the target cluster. External Secret Operator allows you to use external secret management systems (e.g., AWS Secrets Manager, Hashicorp Vault, Azure Secrets Manager, Google Secrets Manager etc.) to securely inject secrets in Kubernetes.
You can install External Secrets Operator using charts store:
Go to charts store.
Search chart with name external-secrets.
Deploy the chart.
If you don't find any chart with this name i.e external-secrets, add chart repository using repository url https://charts.external-secrets.io. Please follow this for adding chart repository.
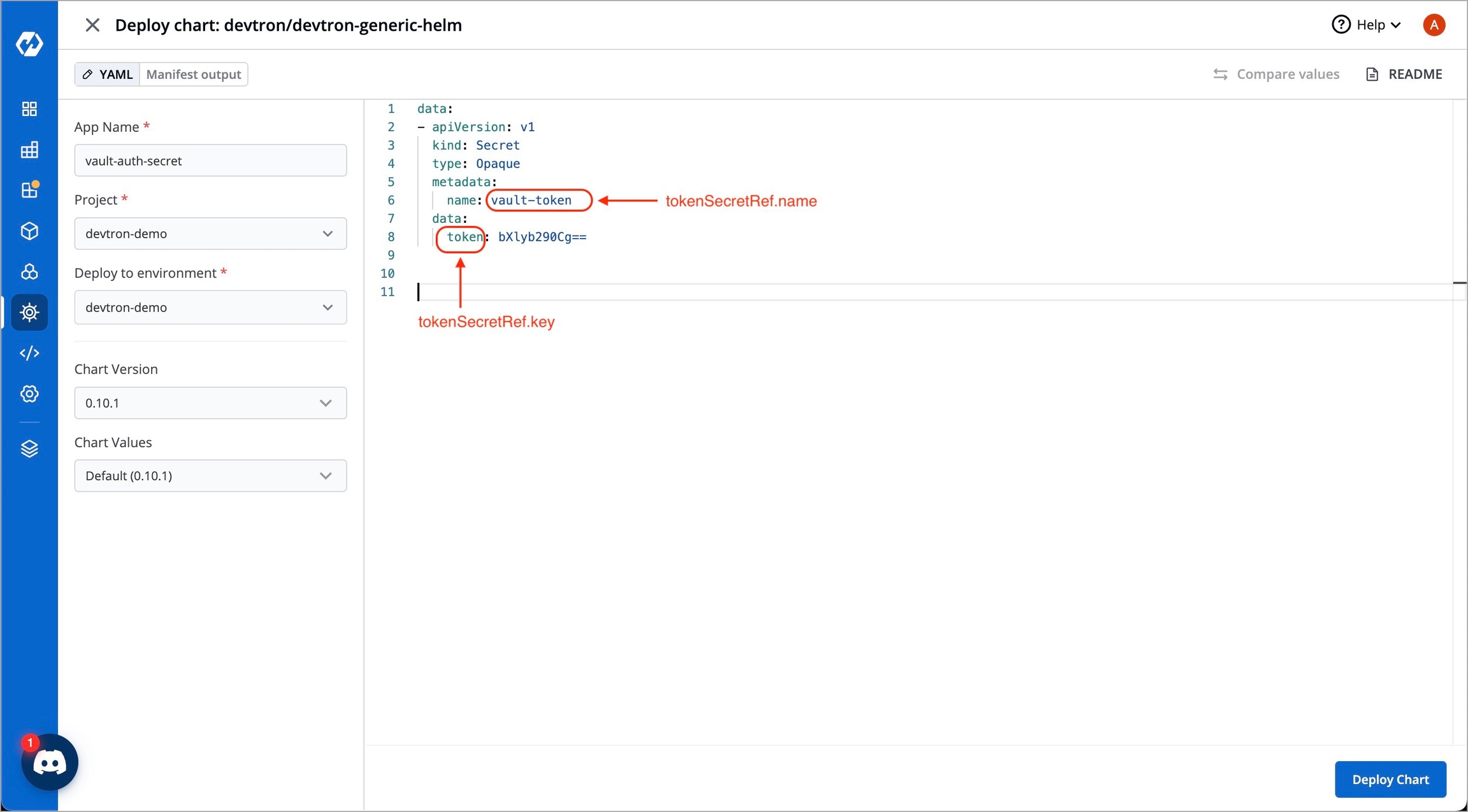
To incorporate secrets from HashiCorp Vault, you need to create a generic Kubernetes secret that will be used for vault authentication. This involves creating a Kubernetes secret in the specific namespace where your application will be deployed. The secret should store the base64-encoded password or token obtained from vault. To simplify the process, you can utilize the Devtron generic chart. An example yaml is given below:
Note: Please note that you don't need to create the Kubernetes secret every time you create an External Secret for the corresponding namespace.
Once you have created the generic secret, follow these steps in the application's Secrets section:
1. Create a new secret
To add a new secret to the application, go to the App Configuration section of the application. Then, navigate to the left pane and select the Secrets option and click the Add Secret button.
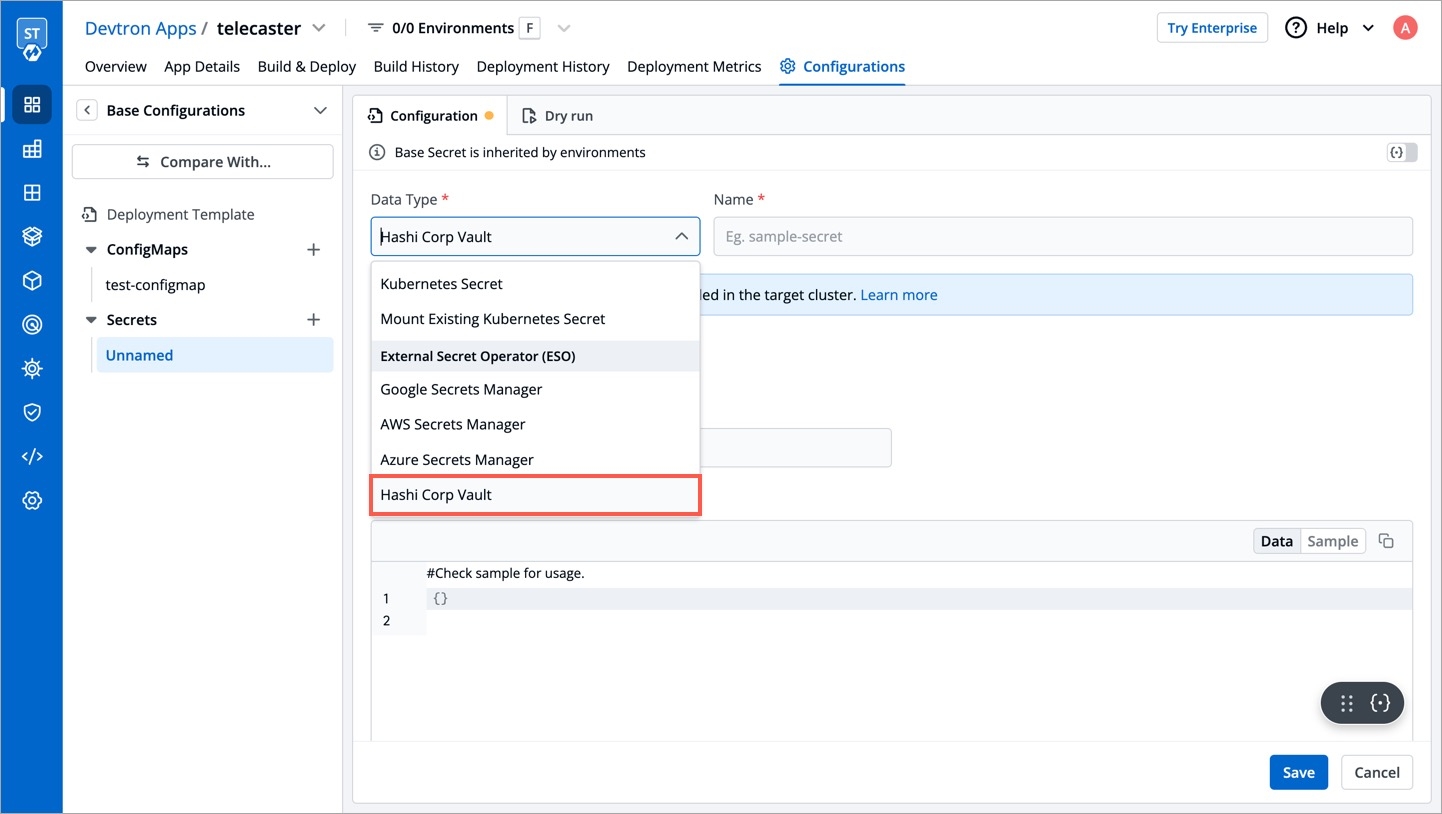
2. Select HashiCorp Vault as the External Secret Operator
After clicking the Add Secret button, select HashiCorp Vault from the dropdown menu for the Data type option. Provide a name for the secret you are creating, and then proceed to configure the external secret as described in the next step.
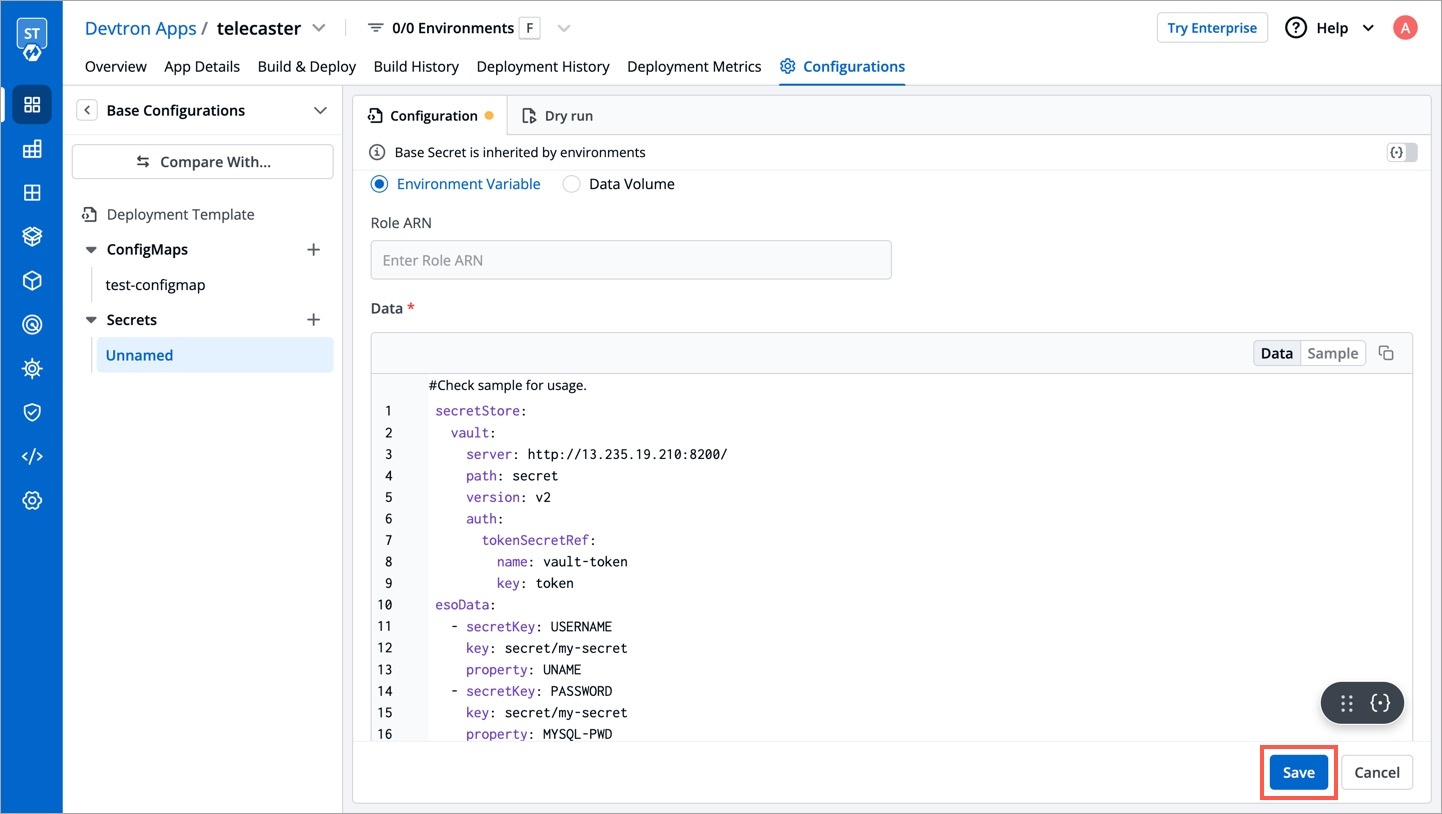
3. Configure the secret
To configure the external secret that will be fetched from HashiCorp Vault for your application, you will need to provide specific details using the following key-value pairs:
vault.server
Server is the connection address for the Vaultserver, e.g: "https://vault.example.com:8200"
vault.path
Specify the path where the secret is stored in Vault
tokenSecretRef.name
Enter the name of the secret that will be used for authentication
tokenSecretRef.key
Specify the key name within the secret that contains the token
secretKey
Provide a name for the secret in Kubernetes
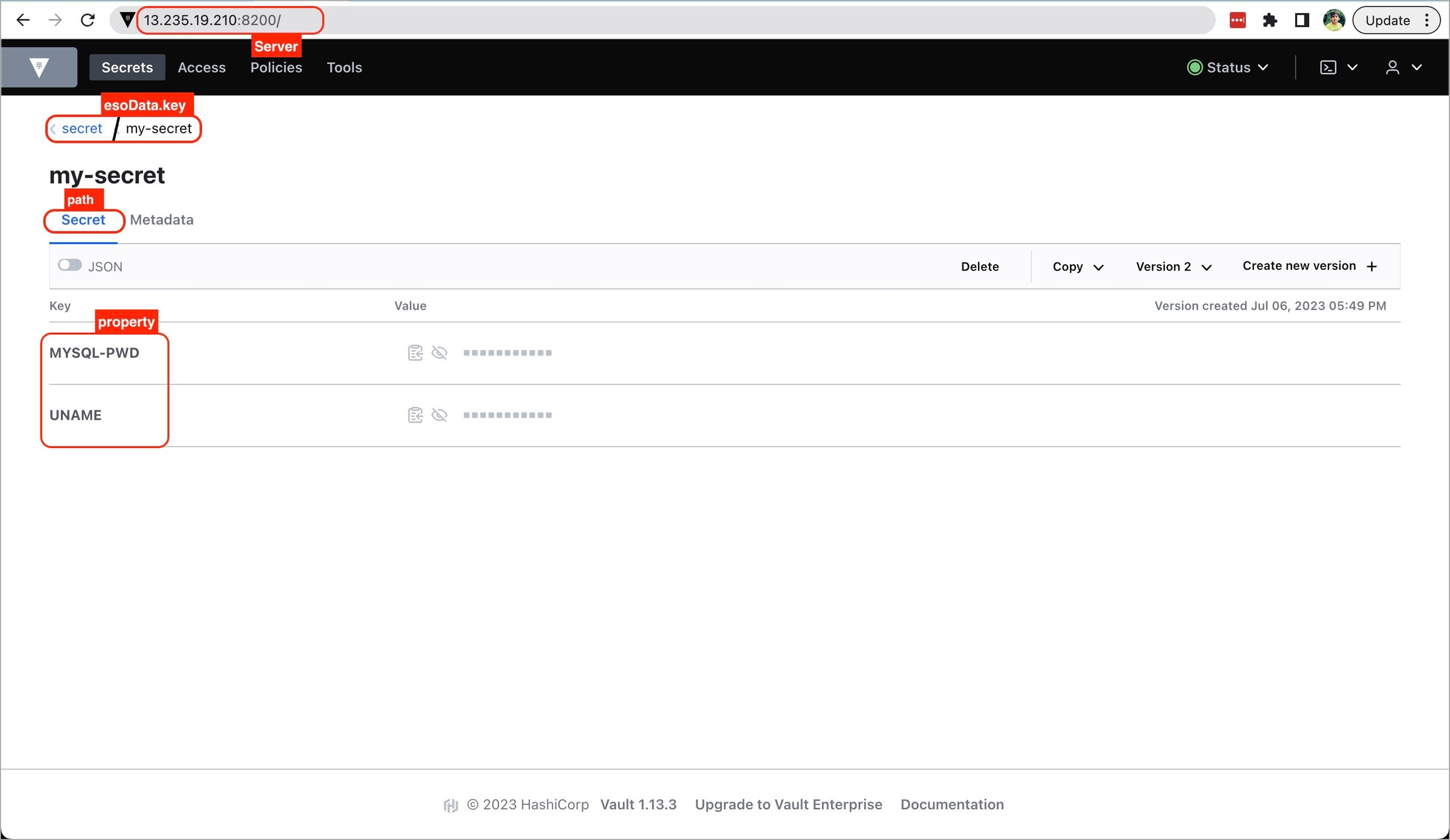
key
Enter the name of the secret in Vault
property
Specify the key within the Vault secret
4. Save the secret
After configuring the external secret from HashiCorp Vault, proceed to save the secret by clicking the Save button.
By following the steps mentioned above and configuring these values correctly, you can seamlessly fetch and utilize external secrets from HashiCorp Vault within your application environment by deploying the application.