Security
Last updated
Was this helpful?
Last updated
Was this helpful?
Devtron provides DevSecOps capabilities across your software development life cycle for both: the default CI/CD solution by Devtron as well as your existing CI/CD Tools.
One of the key components of DevSecOps is the detection of security risks. Currently, Devtron supports the following types of scanning:
Image Scan
You can integrate a scanning tool of your choice. By default, Devtron integrates with Trivy using which you can scan for the following issues:
Vulnerability
License Risks
Misconfigurations
Exposed Secrets
When you commit the code, it's essential to scan it before building a container image. By scanning early, you can catch and fix problems before they become expensive or time-consuming to remediate later.
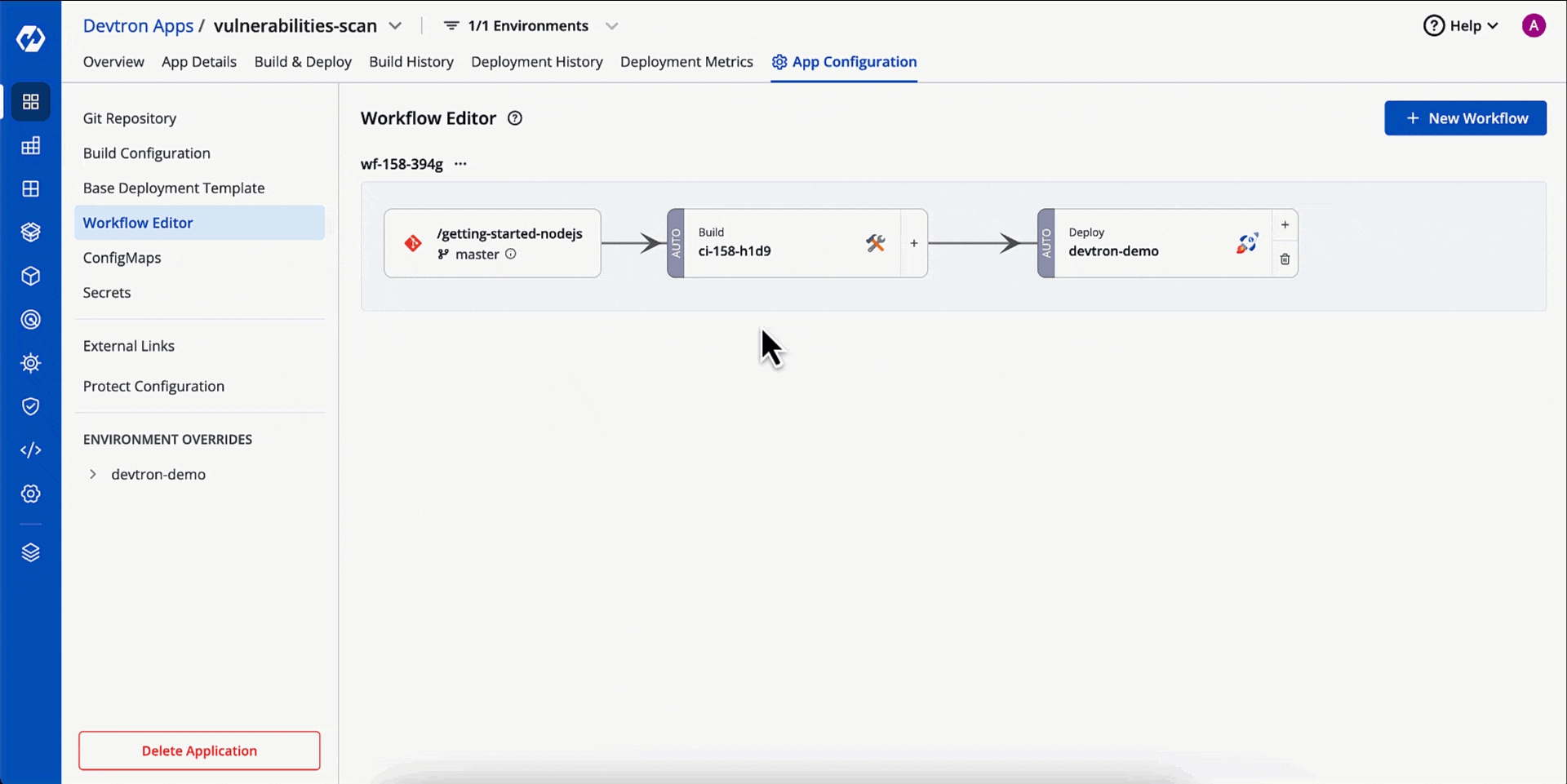
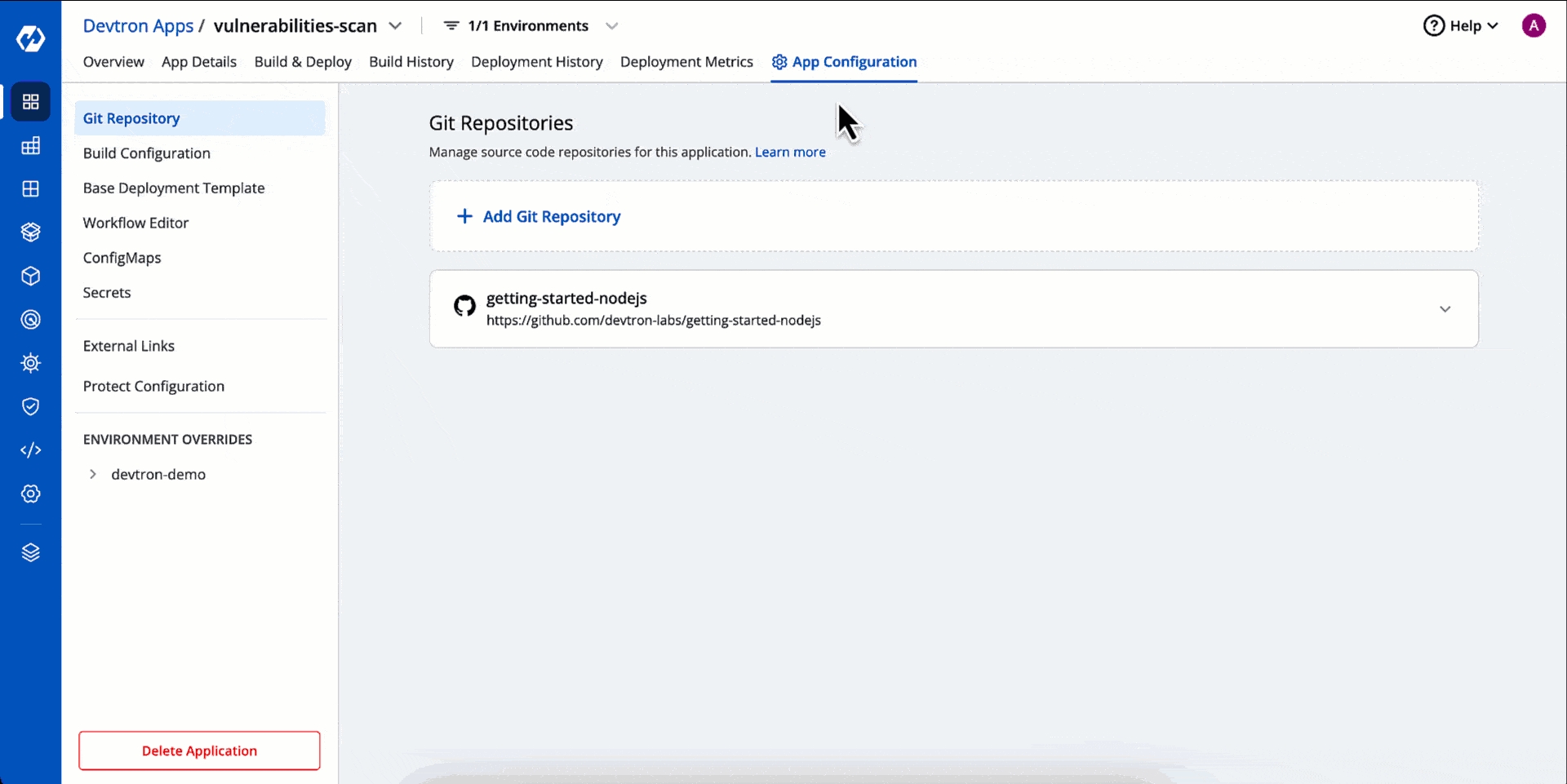
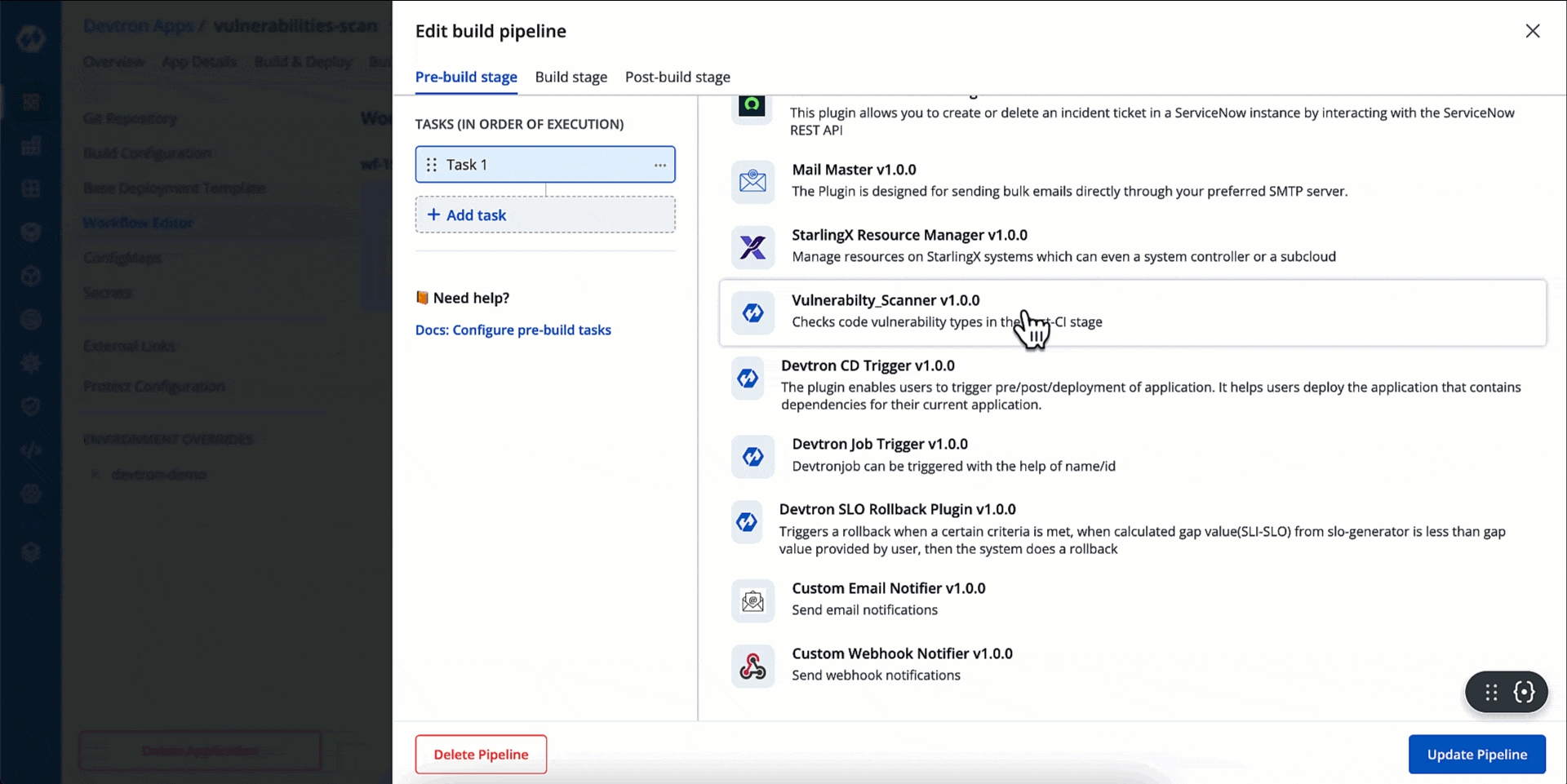
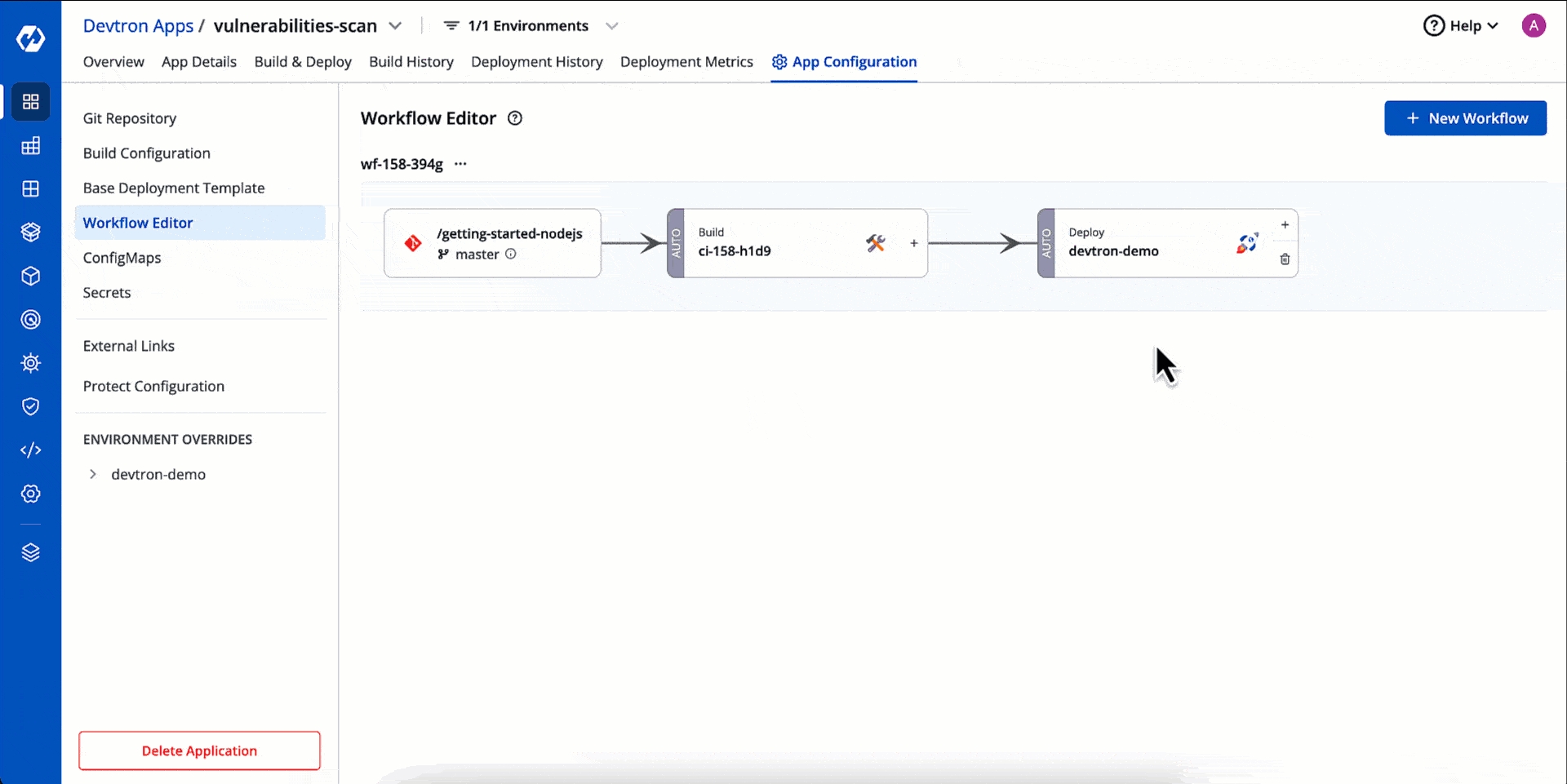
In your application, go to App Configuration → Workflow Editor.
Click the CI pipeline of your preferred workflow.
Go to the Pre-build stage (tab).
Click + Add Task.
Choose Vulnerability_Scanner v1.0.0 plugin from the list.
Click Update Pipeline.
Based on the results of the scanner, you can also decide whether your CI should proceed further or not. This is possible through Pass/Failure Condition setting in the plugin. In the below example, we are allowing image build only if the no. of high vulnerability is zero.
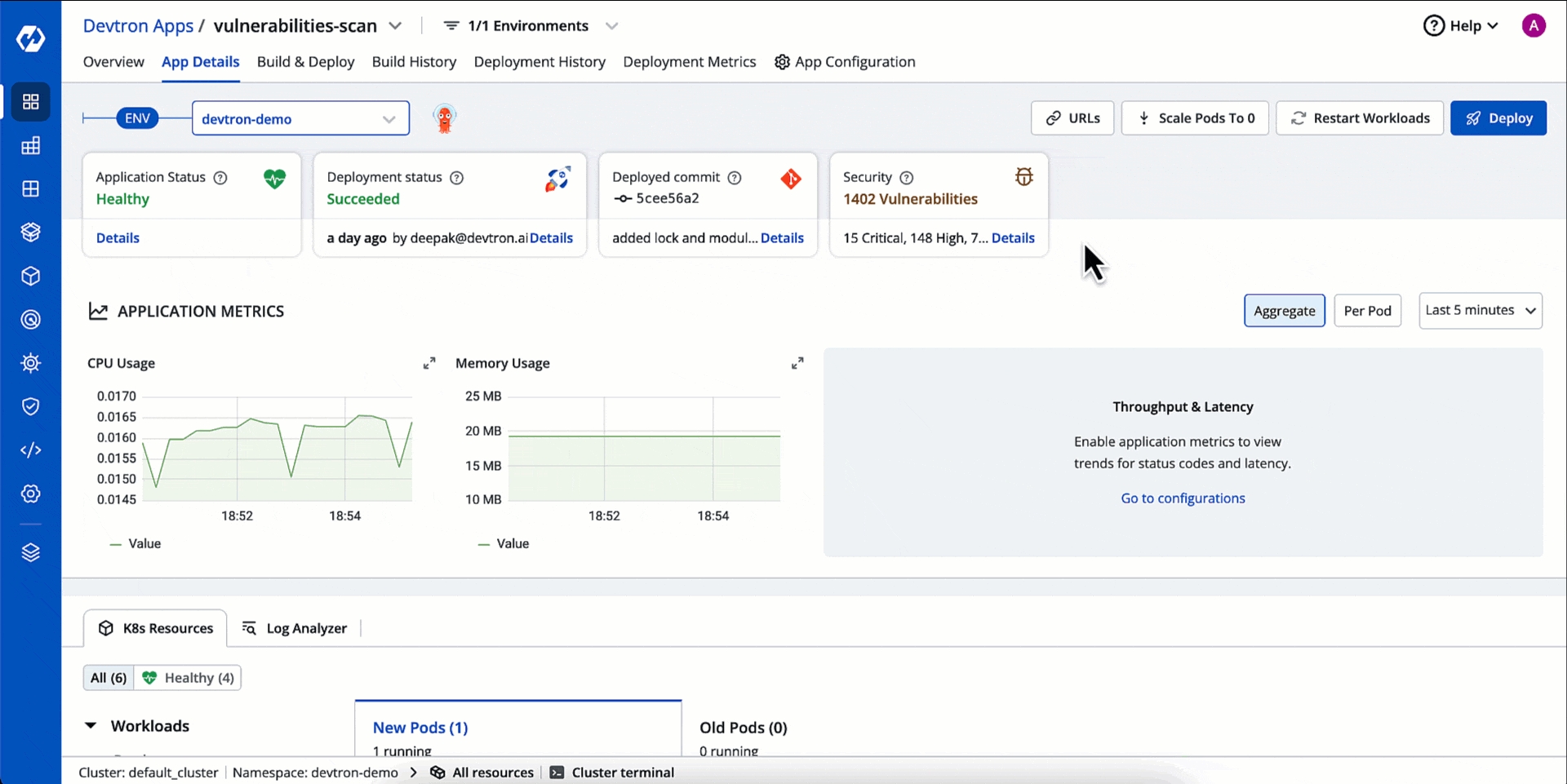
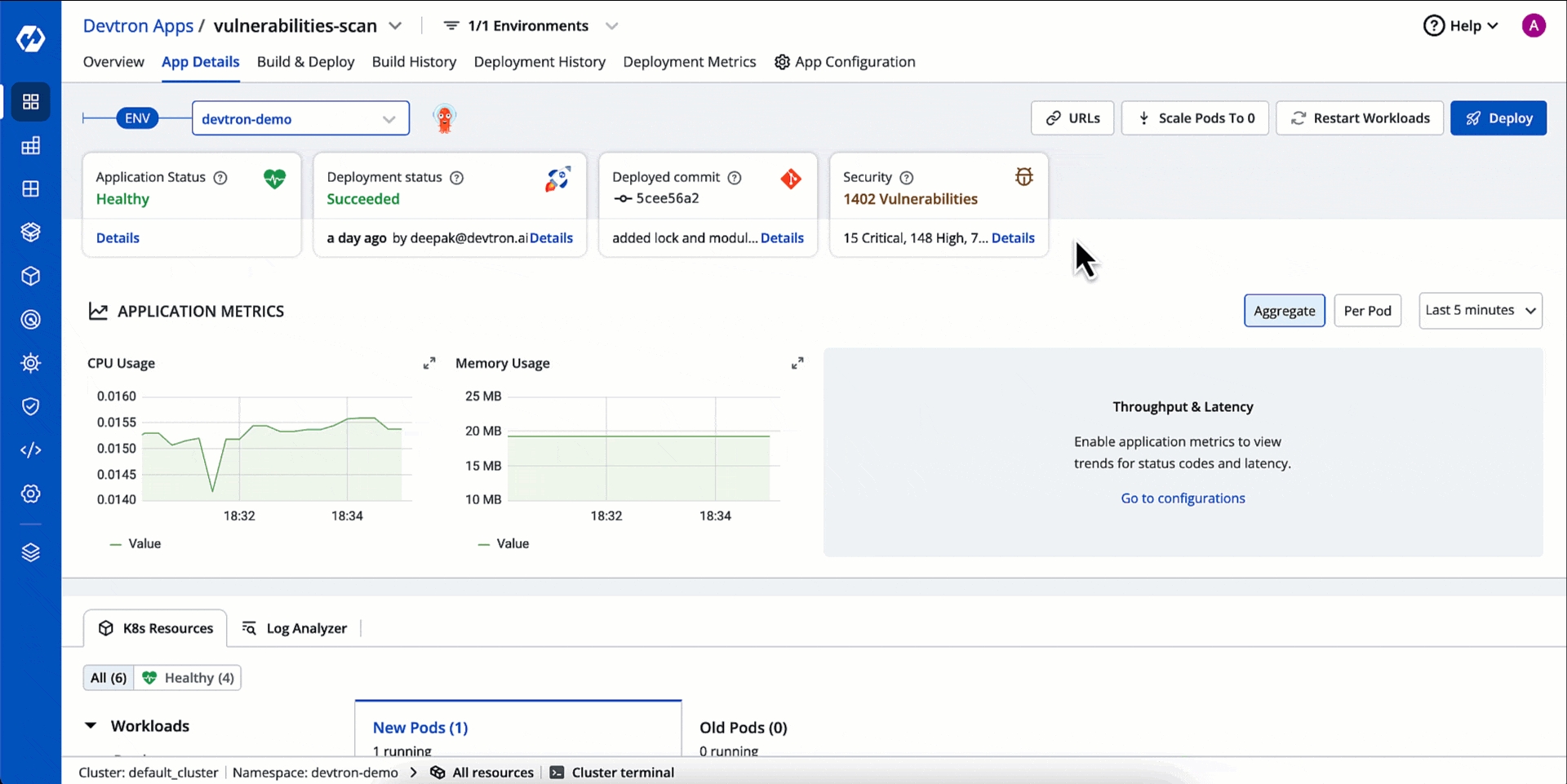
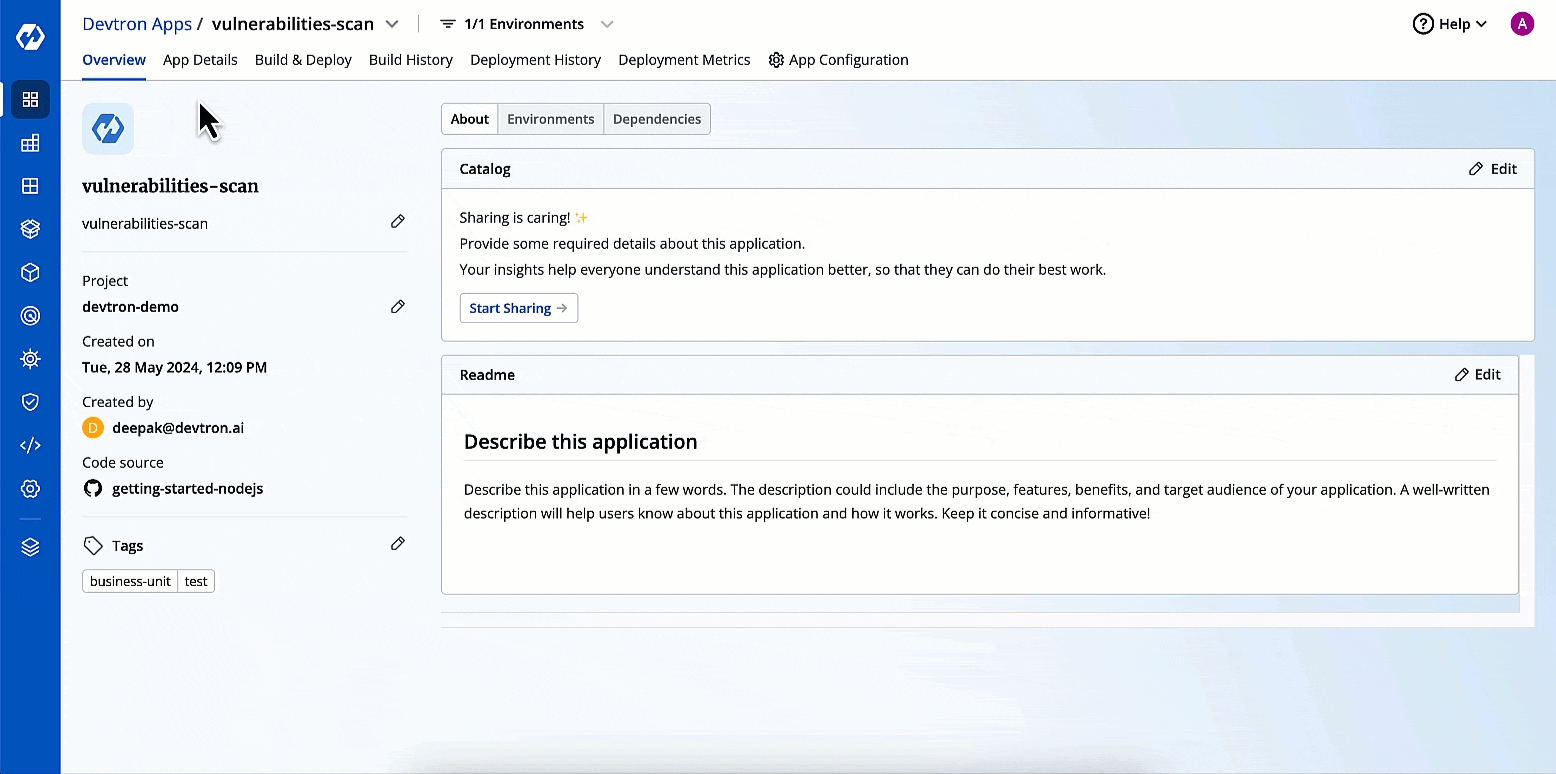
Results of Pre-CI scan will be visible under Code Scan in the App Details page as shown below.
Once a container image is ready, you can scan its base image libraries, stale files, compromised licenses, and many more.
There are 2 options available:
Image scan in the Build stage (refer Security Scans)
Comprehensive scan in Post-Build stage
This section contains the steps for comprehensive scan.
Go to the Post-build stage (tab) of your CI pipeline.
Click + Add Task and choose Vulnerability_Scanner v1.0.0.
Click Update Pipeline.
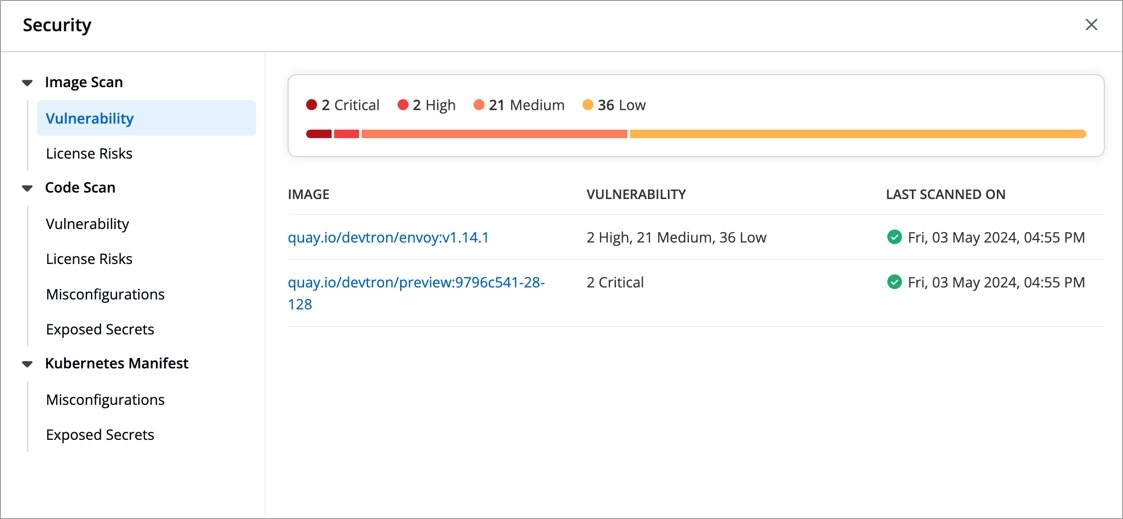
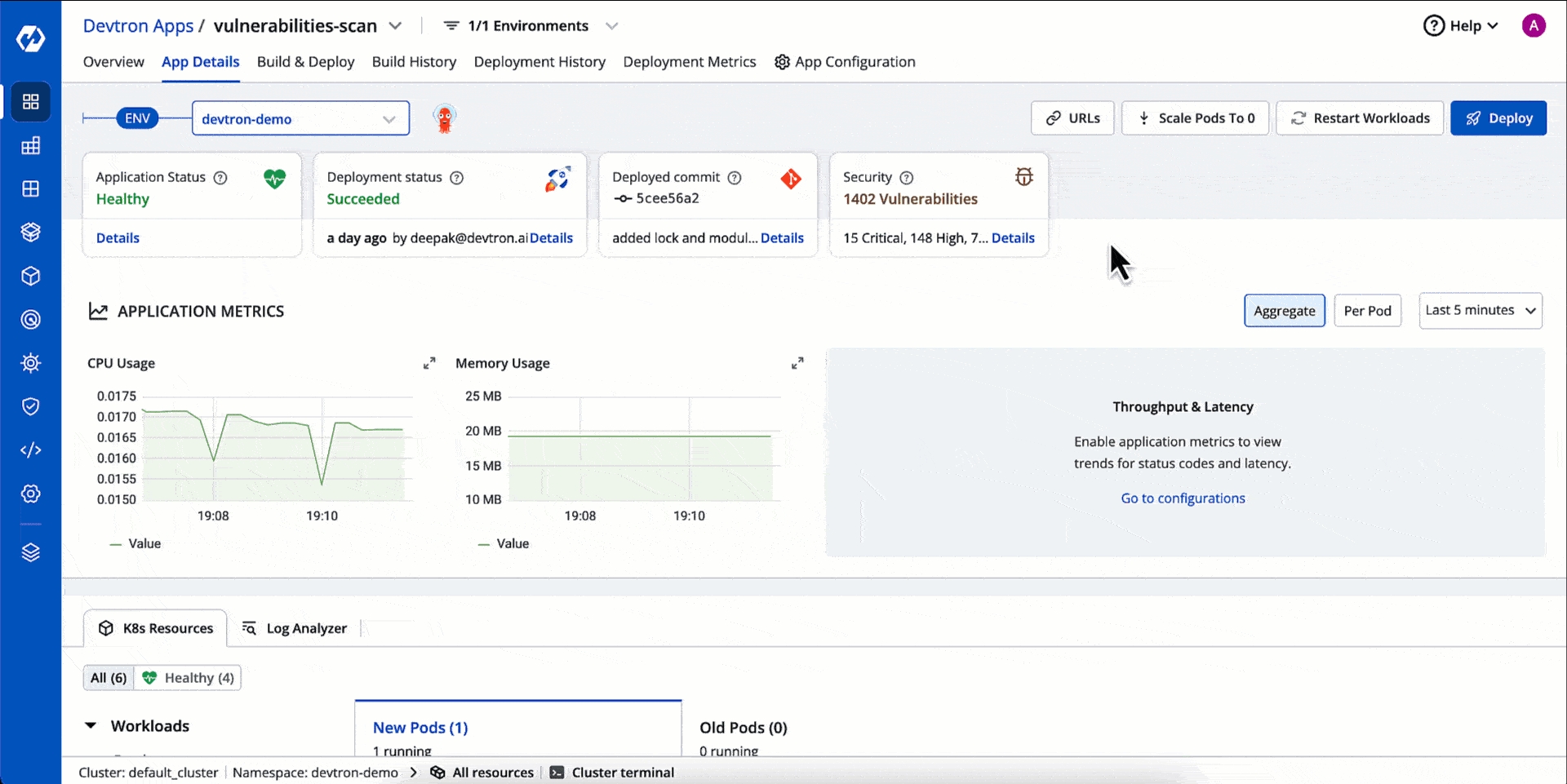
Results of Post-CI scan will be visible under Image Scan in the App Details page as shown below.
There can be a loophole where the original image built in the CI stage gets compromised later (say, in publicly accessible repository). Therefore, you can scan the image and catch issues before deploying it. On top of that, you can also scan manifests to detect misconfigurations and exposed secrets.
Go to the Pre-Deployment stage (tab) of your CD pipeline.
Click + Add Task and choose Vulnerability_Scanner v1.0.0.
Click Update Pipeline.
Results of Pre-CD scan will be visible under Image Scan and Kubernetes Manifest in the App Details page as shown below.
When you deploy a helm chart, Devtron will scan the image associated with that helm chart and also the manifests, but unlike Devtron Apps, there is no code scan involved.
Results of helm app scan will be visible under Image Scan and Kubernetes Manifest in the App Details page as shown below.
You can also check for vulnerabilities within a specific workload such as job, pod, deployment, etc. There are two ways to perform it:
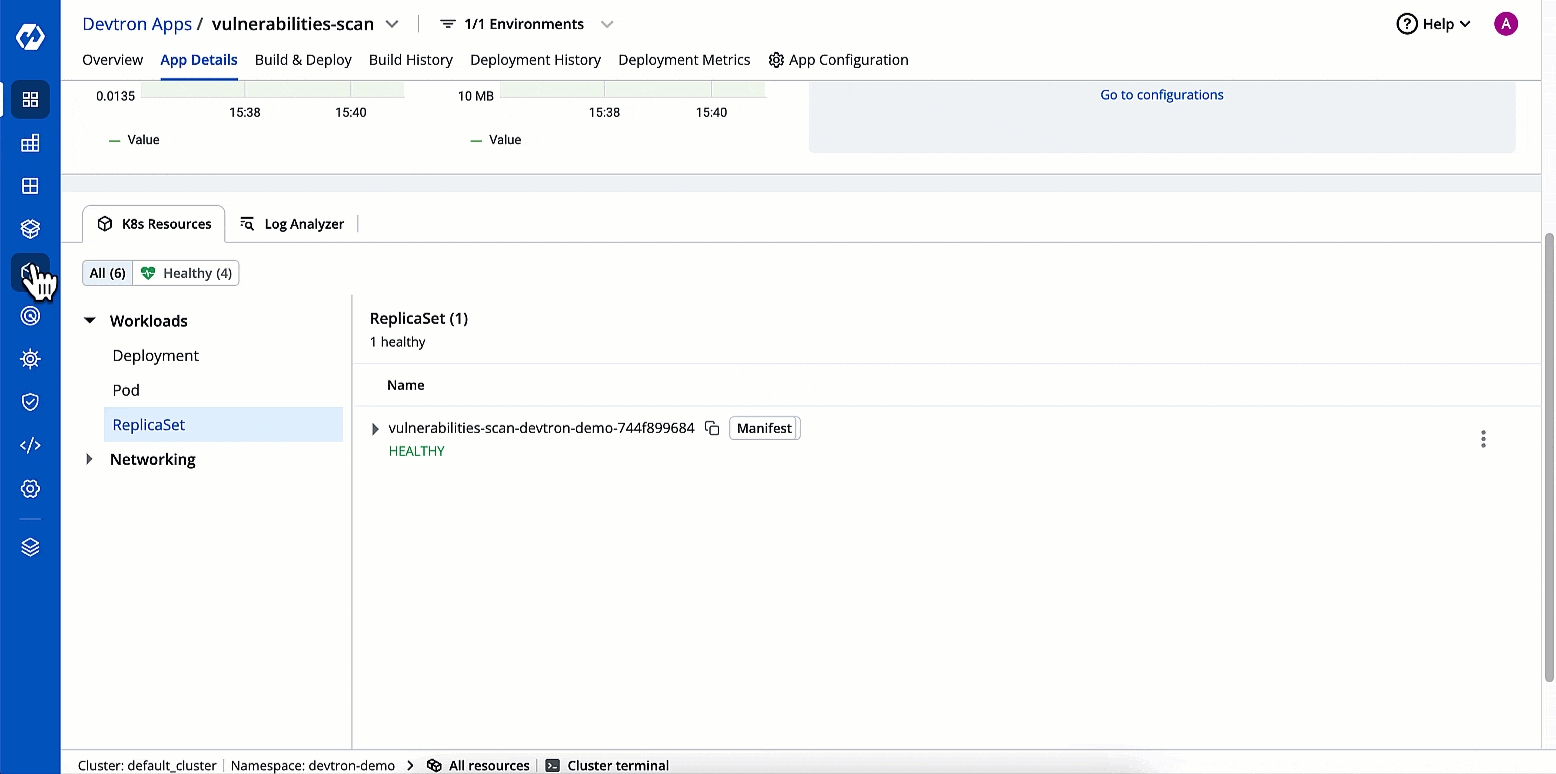
Go to App Details (Devtron App/Helm App) → Workloads (under K8 Resources tab).
Click a workload, e.g., Pod.
On the right-hand side, click the kebab menu (3 vertical dots).
Click Check Vulnerabilities.
Go to Resource Browser.
Select a cluster.
Click a workload within the Workloads dropdown.
Access the Check Vulnerabilities option from the kebab menu present to your selected workload.
Users need to have super-admin permission to enable vulnerability scanning and to define security policies in Devtron.
Devtron's Security feature has two primary sections:
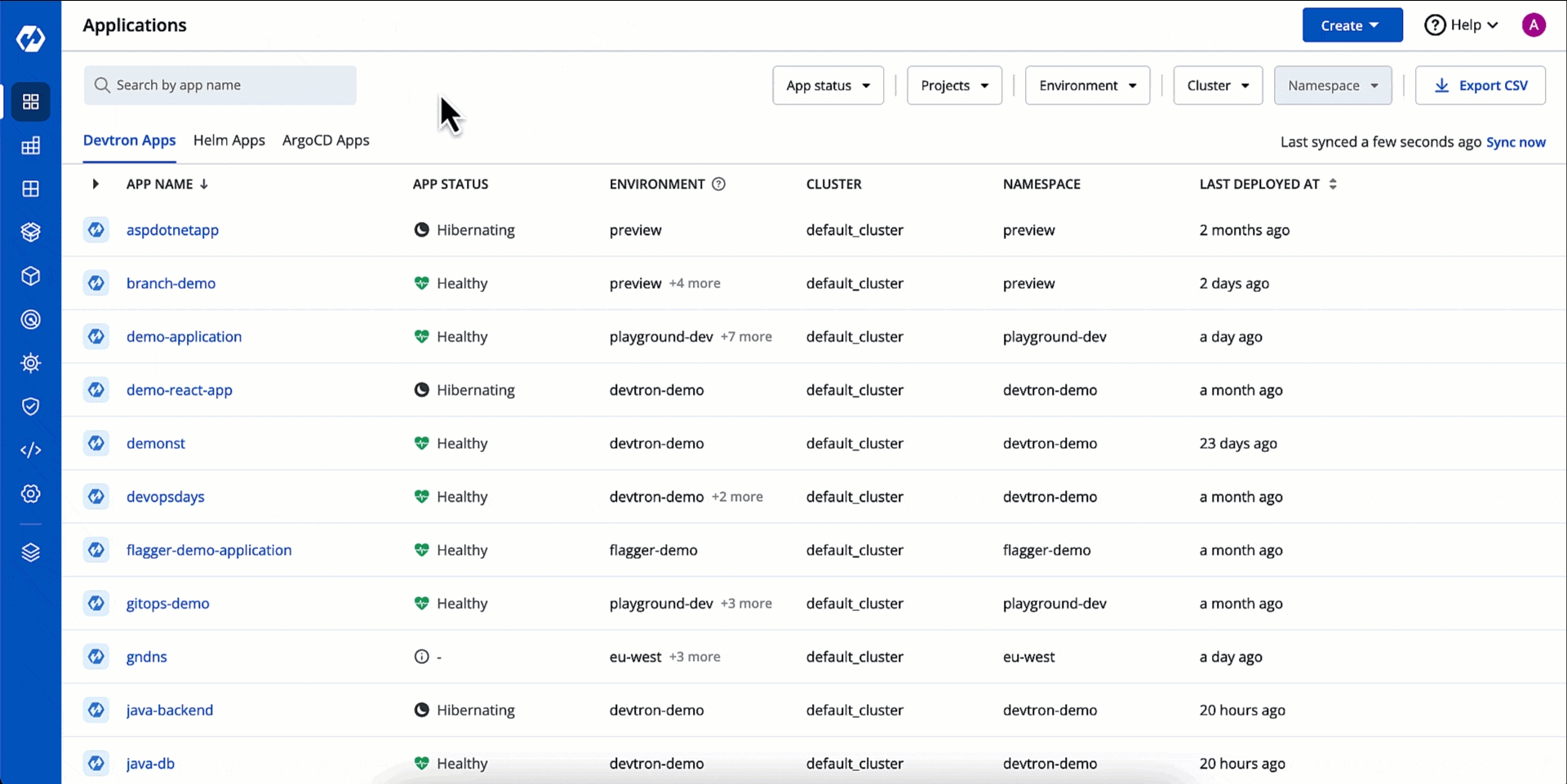
Security Scans - You can view the vulnerabilities detected across your applications.
Security Policies - This allows you to define guardrails to block or allow the deployment of container images depending on the vulnerabilities detected.